mirror of https://gogs.blitter.com/RLabs/xs
Compare commits
No commits in common. "master" and "v0.9.0" have entirely different histories.
409
.golangci.yml
409
.golangci.yml
|
|
@ -1,160 +1,327 @@
|
|||
# This file contains all available configuration options
|
||||
# with their default values.
|
||||
|
||||
# options for analysis running
|
||||
run:
|
||||
# default concurrency is a available CPU number
|
||||
concurrency: 4
|
||||
|
||||
# timeout for analysis, e.g. 30s, 5m, default is 1m
|
||||
timeout: 1m
|
||||
|
||||
# exit code when at least one issue was found, default is 1
|
||||
issues-exit-code: 1
|
||||
|
||||
# include test files or not, default is true
|
||||
tests: true
|
||||
|
||||
# list of build tags, all linters use it. Default is empty list.
|
||||
build-tags:
|
||||
- mytag
|
||||
|
||||
# which dirs to skip: issues from them won't be reported;
|
||||
# can use regexp here: generated.*, regexp is applied on full path;
|
||||
# default value is empty list, but default dirs are skipped independently
|
||||
# from this option's value (see skip-dirs-use-default).
|
||||
skip-dirs:
|
||||
- src/external_libs
|
||||
- autogenerated_by_my_lib
|
||||
|
||||
# default is true. Enables skipping of directories:
|
||||
# vendor$, third_party$, testdata$, examples$, Godeps$, builtin$
|
||||
skip-dirs-use-default: true
|
||||
|
||||
# which files to skip: they will be analyzed, but issues from them
|
||||
# won't be reported. Default value is empty list, but there is
|
||||
# no need to include all autogenerated files, we confidently recognize
|
||||
# autogenerated files. If it's not please let us know.
|
||||
skip-files:
|
||||
- ".*\\.my\\.go$"
|
||||
- lib/bad.go
|
||||
|
||||
# by default isn't set. If set we pass it to "go list -mod={option}". From "go help modules":
|
||||
# If invoked with -mod=readonly, the go command is disallowed from the implicit
|
||||
# automatic updating of go.mod described above. Instead, it fails when any changes
|
||||
# to go.mod are needed. This setting is most useful to check that go.mod does
|
||||
# not need updates, such as in a continuous integration and testing system.
|
||||
# If invoked with -mod=vendor, the go command assumes that the vendor
|
||||
# directory holds the correct copies of dependencies and ignores
|
||||
# the dependency descriptions in go.mod.
|
||||
#! modules-download-mode: readonly|release|vendor
|
||||
|
||||
|
||||
# output configuration options
|
||||
output:
|
||||
# colored-line-number|line-number|json|tab|checkstyle|code-climate, default is "colored-line-number"
|
||||
format: colored-line-number
|
||||
|
||||
# print lines of code with issue, default is true
|
||||
print-issued-lines: true
|
||||
|
||||
# print linter name in the end of issue text, default is true
|
||||
print-linter-name: true
|
||||
|
||||
# make issues output unique by line, default is true
|
||||
uniq-by-line: true
|
||||
|
||||
|
||||
# all available settings of specific linters
|
||||
linters-settings:
|
||||
depguard:
|
||||
list-type: blacklist
|
||||
packages:
|
||||
# logging is allowed only by logutils.Log, logrus
|
||||
# is allowed to use only in logutils package
|
||||
- github.com/sirupsen/logrus
|
||||
packages-with-error-message:
|
||||
- github.com/sirupsen/logrus: "logging is allowed only by logutils.Log"
|
||||
dogsled:
|
||||
# checks assignments with too many blank identifiers; default is 2
|
||||
max-blank-identifiers: 2
|
||||
dupl:
|
||||
threshold: 125
|
||||
# tokens count to trigger issue, 150 by default
|
||||
threshold: 100
|
||||
errcheck:
|
||||
# report about not checking of errors in type assetions: `a := b.(MyStruct)`;
|
||||
# default is false: such cases aren't reported by default.
|
||||
check-type-assertions: false
|
||||
|
||||
# report about assignment of errors to blank identifier: `num, _ := strconv.Atoi(numStr)`;
|
||||
# default is false: such cases aren't reported by default.
|
||||
check-blank: false
|
||||
|
||||
# [deprecated] comma-separated list of pairs of the form pkg:regex
|
||||
# the regex is used to ignore names within pkg. (default "fmt:.*").
|
||||
# see https://github.com/kisielk/errcheck#the-deprecated-method for details
|
||||
ignore: fmt:.*,io/ioutil:^Read.*
|
||||
|
||||
# path to a file containing a list of functions to exclude from checking
|
||||
# see https://github.com/kisielk/errcheck#excluding-functions for details
|
||||
#!exclude: /path/to/file.txt
|
||||
funlen:
|
||||
lines: 125
|
||||
statements: 50
|
||||
gci:
|
||||
local-prefixes: github.com/golangci/golangci-lint
|
||||
lines: 60
|
||||
statements: 40
|
||||
gocognit:
|
||||
# minimal code complexity to report, 30 by default (but we recommend 10-20)
|
||||
min-complexity: 10
|
||||
goconst:
|
||||
min-len: 2
|
||||
min-occurrences: 2
|
||||
# minimal length of string constant, 3 by default
|
||||
min-len: 3
|
||||
# minimal occurrences count to trigger, 3 by default
|
||||
min-occurrences: 3
|
||||
gocritic:
|
||||
enabled-tags:
|
||||
- diagnostic
|
||||
- experimental
|
||||
- performance
|
||||
#- style
|
||||
#- opinionated
|
||||
# Which checks should be enabled; can't be combined with 'disabled-checks';
|
||||
# See https://go-critic.github.io/overview#checks-overview
|
||||
# To check which checks are enabled run `GL_DEBUG=gocritic golangci-lint run`
|
||||
# By default list of stable checks is used.
|
||||
enabled-checks:
|
||||
#!- rangeValCopy
|
||||
|
||||
# Which checks should be disabled; can't be combined with 'enabled-checks'; default is empty
|
||||
disabled-checks:
|
||||
- commentFormatting
|
||||
- commentedOutCode
|
||||
- dupImport # https://github.com/go-critic/go-critic/issues/845
|
||||
- ifElseChain
|
||||
- octalLiteral
|
||||
- whyNoLint
|
||||
- wrapperFunc
|
||||
- regexpMust
|
||||
|
||||
# Enable multiple checks by tags, run `GL_DEBUG=gocritic golangci-lint run` to see all tags and checks.
|
||||
# Empty list by default. See https://github.com/go-critic/go-critic#usage -> section "Tags".
|
||||
enabled-tags:
|
||||
- performance
|
||||
|
||||
settings: # settings passed to gocritic
|
||||
captLocal: # must be valid enabled check name
|
||||
paramsOnly: true
|
||||
rangeValCopy:
|
||||
sizeThreshold: 32
|
||||
gocyclo:
|
||||
min-complexity: 15
|
||||
# minimal code complexity to report, 30 by default (but we recommend 10-20)
|
||||
min-complexity: 10
|
||||
godox:
|
||||
# report any comments starting with keywords, this is useful for TODO or FIXME comments that
|
||||
# might be left in the code accidentally and should be resolved before merging
|
||||
keywords: # default keywords are TODO, BUG, and FIXME, these can be overwritten by this setting
|
||||
- NOTE
|
||||
- OPTIMIZE # marks code that should be optimized before merging
|
||||
- HACK # marks hack-arounds that should be removed before merging
|
||||
gofmt:
|
||||
# simplify code: gofmt with `-s` option, true by default
|
||||
simplify: true
|
||||
goimports:
|
||||
local-prefixes: github.com/golangci/golangci-lint
|
||||
# put imports beginning with prefix after 3rd-party packages;
|
||||
# it's a comma-separated list of prefixes
|
||||
local-prefixes: github.com/org/project
|
||||
golint:
|
||||
# minimal confidence for issues, default is 0.8
|
||||
min-confidence: 0.8
|
||||
gomnd:
|
||||
settings:
|
||||
mnd:
|
||||
# don't include the "operation" and "assign"
|
||||
checks: argument,case,condition,return
|
||||
# the list of enabled checks, see https://github.com/tommy-muehle/go-mnd/#checks for description.
|
||||
checks: argument,case,condition,operation,return,assign
|
||||
govet:
|
||||
# report about shadowed variables
|
||||
check-shadowing: true
|
||||
|
||||
# settings per analyzer
|
||||
settings:
|
||||
printf:
|
||||
funcs:
|
||||
printf: # analyzer name, run `go tool vet help` to see all analyzers
|
||||
funcs: # run `go tool vet help printf` to see available settings for `printf` analyzer
|
||||
- (github.com/golangci/golangci-lint/pkg/logutils.Log).Infof
|
||||
- (github.com/golangci/golangci-lint/pkg/logutils.Log).Warnf
|
||||
- (github.com/golangci/golangci-lint/pkg/logutils.Log).Errorf
|
||||
- (github.com/golangci/golangci-lint/pkg/logutils.Log).Fatalf
|
||||
|
||||
# enable or disable analyzers by name
|
||||
enable:
|
||||
- atomicalign
|
||||
enable-all: false
|
||||
disable:
|
||||
- shadow
|
||||
disable-all: false
|
||||
depguard:
|
||||
list-type: blacklist
|
||||
include-go-root: false
|
||||
packages:
|
||||
- github.com/sirupsen/logrus
|
||||
packages-with-error-message:
|
||||
# specify an error message to output when a blacklisted package is used
|
||||
- github.com/sirupsen/logrus: "logging is allowed only by logutils.Log"
|
||||
lll:
|
||||
line-length: 140
|
||||
# max line length, lines longer will be reported. Default is 120.
|
||||
# '\t' is counted as 1 character by default, and can be changed with the tab-width option
|
||||
line-length: 120
|
||||
# tab width in spaces. Default to 1.
|
||||
tab-width: 1
|
||||
maligned:
|
||||
# print struct with more effective memory layout or not, false by default
|
||||
suggest-new: true
|
||||
misspell:
|
||||
locale: en_CA
|
||||
nolintlint:
|
||||
allow-leading-space: true # don't require machine-readable nolint directives (i.e. with no leading space)
|
||||
allow-unused: false # report any unused nolint directives
|
||||
require-explanation: false # don't require an explanation for nolint directives
|
||||
require-specific: false # don't require nolint directives to be specific about which linter is being skipped
|
||||
# Correct spellings using locale preferences for US or UK.
|
||||
# Default is to use a neutral variety of English.
|
||||
# Setting locale to US will correct the British spelling of 'colour' to 'color'.
|
||||
locale: US
|
||||
ignore-words:
|
||||
- someword
|
||||
nakedret:
|
||||
# make an issue if func has more lines of code than this setting and it has naked returns; default is 30
|
||||
max-func-lines: 30
|
||||
prealloc:
|
||||
# XXX: we don't recommend using this linter before doing performance profiling.
|
||||
# For most programs usage of prealloc will be a premature optimization.
|
||||
|
||||
# Report preallocation suggestions only on simple loops that have no returns/breaks/continues/gotos in them.
|
||||
# True by default.
|
||||
simple: true
|
||||
range-loops: true # Report preallocation suggestions on range loops, true by default
|
||||
for-loops: false # Report preallocation suggestions on for loops, false by default
|
||||
rowserrcheck:
|
||||
packages:
|
||||
- github.com/jmoiron/sqlx
|
||||
unparam:
|
||||
# Inspect exported functions, default is false. Set to true if no external program/library imports your code.
|
||||
# XXX: if you enable this setting, unparam will report a lot of false-positives in text editors:
|
||||
# if it's called for subdir of a project it can't find external interfaces. All text editor integrations
|
||||
# with golangci-lint call it on a directory with the changed file.
|
||||
check-exported: false
|
||||
unused:
|
||||
# treat code as a program (not a library) and report unused exported identifiers; default is false.
|
||||
# XXX: if you enable this setting, unused will report a lot of false-positives in text editors:
|
||||
# if it's called for subdir of a project it can't find funcs usages. All text editor integrations
|
||||
# with golangci-lint call it on a directory with the changed file.
|
||||
check-exported: false
|
||||
whitespace:
|
||||
multi-if: false # Enforces newlines (or comments) after every multi-line if statement
|
||||
multi-func: false # Enforces newlines (or comments) after every multi-line function signature
|
||||
wsl:
|
||||
# If true append is only allowed to be cuddled if appending value is
|
||||
# matching variables, fields or types on line above. Default is true.
|
||||
strict-append: true
|
||||
# Allow calls and assignments to be cuddled as long as the lines have any
|
||||
# matching variables, fields or types. Default is true.
|
||||
allow-assign-and-call: true
|
||||
# Allow multiline assignments to be cuddled. Default is true.
|
||||
allow-multiline-assign: true
|
||||
# Allow declarations (var) to be cuddled.
|
||||
allow-cuddle-declarations: false
|
||||
# Allow trailing comments in ending of blocks
|
||||
allow-trailing-comment: false
|
||||
# Force newlines in end of case at this limit (0 = never).
|
||||
force-case-trailing-whitespace: 0
|
||||
|
||||
# The custom section can be used to define linter plugins to be loaded at runtime. See README doc
|
||||
# for more info.
|
||||
custom:
|
||||
# Each custom linter should have a unique name.
|
||||
#! example:
|
||||
#! # The path to the plugin *.so. Can be absolute or local. Required for each custom linter
|
||||
#! path: /path/to/example.so
|
||||
#! # The description of the linter. Optional, just for documentation purposes.
|
||||
#! description: This is an example usage of a plugin linter.
|
||||
#! # Intended to point to the repo location of the linter. Optional, just for documentation purposes.
|
||||
#! original-url: github.com/golangci/example-linter
|
||||
|
||||
linters:
|
||||
# please, do not use `enable-all`: it's deprecated and will be removed soon.
|
||||
# inverted configuration with `enable-all` and `disable` is not scalable during updates of golangci-lint
|
||||
disable-all: true
|
||||
enable:
|
||||
- bodyclose
|
||||
- depguard
|
||||
- dogsled
|
||||
- dupl
|
||||
- errcheck
|
||||
- exhaustive
|
||||
- exportloopref
|
||||
- funlen
|
||||
- gochecknoinits
|
||||
- goconst
|
||||
- gocritic
|
||||
- gocyclo
|
||||
- gofmt
|
||||
- goimports
|
||||
#- golint
|
||||
- gomnd
|
||||
- goprintffuncname
|
||||
- gosec
|
||||
- gosimple
|
||||
- megacheck
|
||||
- govet
|
||||
- ineffassign
|
||||
#- interfacer
|
||||
- lll
|
||||
- misspell
|
||||
#- nakedret
|
||||
- noctx
|
||||
- nolintlint
|
||||
- rowserrcheck
|
||||
#- scopelint
|
||||
- staticcheck
|
||||
#- structcheck
|
||||
- stylecheck
|
||||
- typecheck
|
||||
- unconvert
|
||||
- unparam
|
||||
disable:
|
||||
- maligned
|
||||
- prealloc
|
||||
disable-all: false
|
||||
presets:
|
||||
- bugs
|
||||
- unused
|
||||
#- varcheck
|
||||
- whitespace
|
||||
fast: false
|
||||
|
||||
# don't enable:
|
||||
# - asciicheck
|
||||
# - deadcode
|
||||
# - gochecknoglobals
|
||||
# - gocognit
|
||||
# - godot
|
||||
# - godox
|
||||
# - goerr113
|
||||
# - golint
|
||||
# - interfacer
|
||||
# - maligned
|
||||
# - nestif
|
||||
# - prealloc
|
||||
## - rowserrcheck
|
||||
# - scopelint
|
||||
# - structcheck
|
||||
# - testpackage
|
||||
# - varcheck
|
||||
# - wsl
|
||||
|
||||
issues:
|
||||
# List of regexps of issue texts to exclude, empty list by default.
|
||||
# But independently from this option we use default exclude patterns,
|
||||
# it can be disabled by `exclude-use-default: false`. To list all
|
||||
# excluded by default patterns execute `golangci-lint run --help`
|
||||
exclude:
|
||||
- abcdef
|
||||
|
||||
# Excluding configuration per-path, per-linter, per-text and per-source
|
||||
exclude-rules:
|
||||
# Exclude some linters from running on tests files.
|
||||
- path: _test\.go
|
||||
linters:
|
||||
- gomnd
|
||||
- gocyclo
|
||||
- errcheck
|
||||
- dupl
|
||||
- gosec
|
||||
|
||||
# https://github.com/go-critic/go-critic/issues/926
|
||||
# Exclude known linters from partially hard-vendored code,
|
||||
# which is impossible to exclude via "nolint" comments.
|
||||
- path: internal/hmac/
|
||||
text: "weak cryptographic primitive"
|
||||
linters:
|
||||
- gosec
|
||||
|
||||
# Exclude some staticcheck messages
|
||||
- linters:
|
||||
- gocritic
|
||||
text: "unnecessaryDefer:"
|
||||
- staticcheck
|
||||
text: "SA9003:"
|
||||
|
||||
# TODO temporary rule, must be removed
|
||||
# seems related to v0.34.1, but I was not able to reproduce locally,
|
||||
# I was also not able to reproduce in the CI of a fork,
|
||||
# only the golangci-lint CI seems to be affected by this invalid analysis.
|
||||
- path: pkg/golinters/scopelint.go
|
||||
text: 'directive `//nolint:interfacer` is unused for linter interfacer'
|
||||
# Exclude lll issues for long lines with go:generate
|
||||
- linters:
|
||||
- lll
|
||||
source: "^//go:generate "
|
||||
|
||||
run:
|
||||
skip-dirs:
|
||||
- test/testdata_etc
|
||||
- internal/cache
|
||||
- internal/renameio
|
||||
- internal/robustio
|
||||
# Independently from option `exclude` we use default exclude patterns,
|
||||
# it can be disabled by this option. To list all
|
||||
# excluded by default patterns execute `golangci-lint run --help`.
|
||||
# Default value for this option is true.
|
||||
exclude-use-default: false
|
||||
|
||||
# golangci.com configuration
|
||||
# https://github.com/golangci/golangci/wiki/Configuration
|
||||
service:
|
||||
golangci-lint-version: 1.23.x # use the fixed version to not introduce new linters unexpectedly
|
||||
prepare:
|
||||
- echo "here I can run custom commands, but no preparation needed for this repo"
|
||||
# Maximum issues count per one linter. Set to 0 to disable. Default is 50.
|
||||
max-issues-per-linter: 0
|
||||
|
||||
# Maximum count of issues with the same text. Set to 0 to disable. Default is 3.
|
||||
max-same-issues: 0
|
||||
|
||||
# Show only new issues: if there are unstaged changes or untracked files,
|
||||
# only those changes are analyzed, else only changes in HEAD~ are analyzed.
|
||||
# It's a super-useful option for integration of golangci-lint into existing
|
||||
# large codebase. It's not practical to fix all existing issues at the moment
|
||||
# of integration: much better don't allow issues in new code.
|
||||
# Default is false.
|
||||
new: false
|
||||
|
||||
# Show only new issues created after git revision `REV`
|
||||
#!new-from-rev: REV
|
||||
#new-from-rev: HEAD^
|
||||
|
||||
# Show only new issues created in git patch with set file path.
|
||||
#!new-from-patch: path/to/patch/file
|
||||
|
|
|
|||
37
LICENSE
37
LICENSE
|
|
@ -1,37 +0,0 @@
|
|||
MIT NON-AI License
|
||||
|
||||
Copyright (c) 2017 - 2026 Russell Magee (xs/xsd/xsnet/xspasswd)
|
||||
|
||||
Permission is hereby granted, free of charge, to any person obtaining a copy of the software and associated documentation files (the "Software"), to deal in
|
||||
the Software without restriction, including without limitation the
|
||||
rights to use, copy, modify, merge, publish, distribute, sublicense,
|
||||
and/or sell copies of the Software, and to permit persons to whom the
|
||||
Software is furnished to do so, subject to the following conditions.
|
||||
|
||||
The above copyright notice and this permission notice shall be included
|
||||
in all copies or substantial portions of the Software.
|
||||
|
||||
In addition, the following restrictions apply:
|
||||
|
||||
1. The Software and any modifications made to it may not be used for the
|
||||
purpose of training or improving machine learning algorithms, including
|
||||
but not limited to artificial intelligence, natural language processing,
|
||||
or data mining. This condition applies to any derivatives,
|
||||
modifications, or updates based on the Software code. Any usage of the
|
||||
Software in an AI-training dataset is considered a breach of this License.
|
||||
|
||||
2. The Software may not be included in any dataset used for training or
|
||||
improving machine learning algorithms, including but not limited to
|
||||
artificial intelligence, natural language processing, or data mining.
|
||||
|
||||
3. Any person or organization found to be in violation of these
|
||||
restrictions will be subject to legal action and may be held liable for
|
||||
any damages resulting from such use.
|
||||
|
||||
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS
|
||||
OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
|
||||
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL
|
||||
THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR
|
||||
OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE,
|
||||
ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR
|
||||
OTHER DEALINGS IN THE SOFTWARE.
|
||||
|
|
@ -0,0 +1,21 @@
|
|||
MIT License
|
||||
|
||||
Copyright (c) 2017 - 2019 Russell Magee (xs/xsd/xsnet/xspasswd)
|
||||
|
||||
Permission is hereby granted, free of charge, to any person obtaining a copy
|
||||
of this software and associated documentation files (the "Software"), to deal
|
||||
in the Software without restriction, including without limitation the rights
|
||||
to use, copy, modify, merge, publish, distribute, sublicense, and/or sell
|
||||
copies of the Software, and to permit persons to whom the Software is
|
||||
furnished to do so, subject to the following conditions:
|
||||
|
||||
The above copyright notice and this permission notice shall be included in all
|
||||
copies or substantial portions of the Software.
|
||||
|
||||
THE SOFTWARE IS PROVIDED "AS IS", WITHOUT WARRANTY OF ANY KIND, EXPRESS OR
|
||||
IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY,
|
||||
FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE
|
||||
AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER
|
||||
LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM,
|
||||
OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE
|
||||
SOFTWARE.
|
||||
49
Makefile
49
Makefile
|
|
@ -1,7 +1,6 @@
|
|||
VERSION := 0.9.17
|
||||
.PHONY: lint vis clean common client server passwd\
|
||||
subpkgs install uninstall reinstall scc
|
||||
|
||||
VERSION := 0.9.0
|
||||
.PHONY: lint vis clean common client server passwd subpkgs install uninstall reinstall
|
||||
|
||||
## Tag version of binaries with build info wrt.
|
||||
## GO111MODULE(=on) and vendor/ setup vs. $GOPATH pkg builds
|
||||
############################################################
|
||||
|
|
@ -11,14 +10,6 @@ else
|
|||
MTAG="-m"
|
||||
endif
|
||||
|
||||
# If available, one may build 'garbled' binaries
|
||||
# See https://github.com/burrowers/garble.git
|
||||
ifeq ($(GARBLE),y)
|
||||
GO=garble -literals -tiny -debugdir=garbled
|
||||
else
|
||||
GO=go
|
||||
endif
|
||||
|
||||
ifneq ($(VENDOR),)
|
||||
GOBUILDOPTS :=-v -mod vendor
|
||||
VTAG = "-v"
|
||||
|
|
@ -34,7 +25,7 @@ GIT_COMMIT := $(shell git rev-list -1 HEAD)
|
|||
BUILDOPTS :=$(BUILDOPTS)"$(GOBUILDOPTS) -ldflags \"-X main.version=$(VERSION)$(MTAG)$(VTAG) -X main.gitCommit=$(GIT_COMMIT)\""
|
||||
#endif
|
||||
|
||||
SUBPKGS = logger xsnet
|
||||
SUBPKGS = logger spinsult xsnet
|
||||
TOOLS = xs xsd
|
||||
SUBDIRS = $(LIBS) $(TOOLS)
|
||||
|
||||
|
|
@ -43,10 +34,13 @@ ifeq ($(GOOS),)
|
|||
endif
|
||||
|
||||
ifeq ($(GOOS),windows)
|
||||
INSTPREFIX = /usr
|
||||
else
|
||||
INSTPREFIX = /usr/local
|
||||
ifeq ($(MSYSTEM),MSYS)
|
||||
WIN_MSYS=1
|
||||
endif
|
||||
endif
|
||||
|
||||
|
||||
INSTPREFIX = /usr/local
|
||||
|
||||
all: common client server
|
||||
|
||||
|
|
@ -69,8 +63,8 @@ tools:
|
|||
|
||||
|
||||
common:
|
||||
$(GO) build .
|
||||
go install -a .
|
||||
go build .
|
||||
go install .
|
||||
|
||||
|
||||
client: common
|
||||
|
|
@ -78,15 +72,12 @@ client: common
|
|||
|
||||
|
||||
server: common
|
||||
ifeq ($(GOOS),windows)
|
||||
ifeq ($(MSYSTEM),MSYS)
|
||||
echo "Build of xsd server for Windows not yet supported"
|
||||
else
|
||||
$(MAKE) BUILDOPTS=$(BUILDOPTS) -C xsd
|
||||
endif
|
||||
|
||||
scc:
|
||||
@scc --exclude-dir=bacillus,vendor,garbled --cocomo-project-type=rlabs,3,1.12,1,1
|
||||
|
||||
vis:
|
||||
@which go-callvis >/dev/null 2>&1; \
|
||||
stat=$$?; if [ $$stat -ne "0" ]; then \
|
||||
|
|
@ -103,10 +94,13 @@ lint:
|
|||
reinstall: uninstall install
|
||||
|
||||
install:
|
||||
ifeq ($(GOOS),windows)
|
||||
cp xs/xs $(INSTPREFIX)/bin/xs
|
||||
cp xs/xs $(INSTPREFIX)/bin/xc
|
||||
@echo "Install of xsd server for Windows not yet supported"
|
||||
echo "WIN_MSYS:" $(WIN_MSYS)
|
||||
ifdef WIN_MSYS
|
||||
cp xs/mintty_wrapper.sh $(INSTPREFIX)/bin/xs
|
||||
cp xs/mintty_wrapper.sh $(INSTPREFIX)/bin/xc
|
||||
cp xs/xs $(INSTPREFIX)/bin/_xs
|
||||
cp xs/xs $(INSTPREFIX)/bin/_xc
|
||||
echo "Install of xsd server for Windows not yet supported"
|
||||
else
|
||||
cp xs/xs $(INSTPREFIX)/bin
|
||||
cd $(INSTPREFIX)/bin && ln -s xs xc && cd -
|
||||
|
|
@ -114,7 +108,8 @@ else
|
|||
endif
|
||||
|
||||
uninstall:
|
||||
rm -f $(INSTPREFIX)/bin/xs $(INSTPREFIX)/bin/xc
|
||||
rm -f $(INSTPREFIX)/bin/xs $(INSTPREFIX)/bin/xc \
|
||||
$(INSTPREFIX)/bin/_xs $(INSTPREFIX)/bin/_xc
|
||||
ifndef $(WIN_MSYS)
|
||||
rm -f $(INSTPREFIX)/sbin/xsd
|
||||
endif
|
||||
|
|
|
|||
98
README.md
98
README.md
|
|
@ -1,19 +1,11 @@
|
|||
[](https://godoc.org/blitter.com/go/xs)
|
||||
|
||||
# XS
|
||||
|
||||

|
||||
|
||||
--
|
||||
|
||||
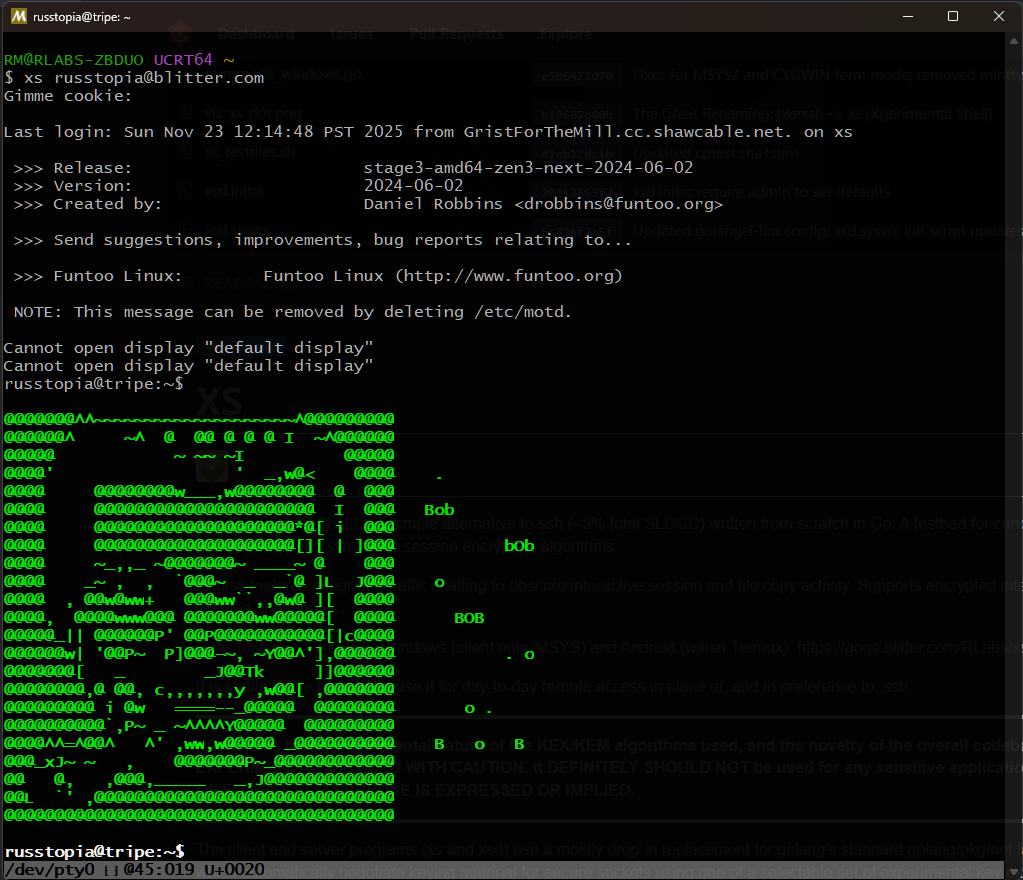
XS (**X**perimental **S**hell) is a simple alternative to ssh (<5% total SLOCC) written from scratch in Go.
|
||||
A testbed for candidate PQC (Post-Quantum Cryptography) KEMs (Key-Encapsulation Mechanisms) and symmetric
|
||||
session encryption algorithms.
|
||||
|
||||
xs also features integrated traffic chaffing to obscure interactive session and file copy activity.
|
||||
Supports encrypted interactive and non-interactive sessions (remote commands), remote file copying and tunnels.
|
||||
|
||||
Runs on Linux, FreeBSD, Windows (client only, MSYS) and Android (within Termux). https://gogs.blitter.com/RLabs/xs
|
||||
XS (**X**perimental **S**hell) is a golang implementation of a simple remote shell client and
|
||||
server, similar in role to ssh, offering encrypted interactive and non-interactive sessions (remote commands),
|
||||
remote file copying and tunnels with optional traffic obfuscation ('chaffing').
|
||||
|
||||
It is stable to the point that I use it for day-to-day remote access in place of, and in preference to, ssh.
|
||||
|
||||
|
|
@ -33,8 +25,8 @@ Currently supported exchanges are:
|
|||
|
||||
* The HerraduraKEx key exchange algorithm first released at
|
||||
[Omar Elejandro Herrera Reyna's HerraduraKEx project](http://github.com/Caume/HerraduraKEx);
|
||||
* The KYBER IND-CCA-2 secure key encapsulation mechanism, [pq-crystals Kyber](https://pq-crystals.org/kyber/) :: [Yawning/kyber golang implementation](https://gitlab.com/yawning/kyber)
|
||||
* The NEWHOPE algorithm [newhopecrypto.org](https://www.newhopecrypto.org/) :: [Yawning/newhope golang implementation](https://gitlab.com/yawning/newhope)
|
||||
* The KYBER IND-CCA-2 secure key encapsulation mechanism, [pq-crystals Kyber](https://pq-crystals.org/kyber/) :: [Yawning/kyber golang implementation](https://git.schwanenlied.me/yawning/kyber)
|
||||
* The NEWHOPE algorithm [newhopecrypto.org](https://www.newhopecrypto.org/) :: [Yawning/go-newhope golang implementation](https://git.schwanenlied.me/yawning/newhope)
|
||||
* The FrodoKEM algorithm [frodokem.org](https://frodokem.org/) :: Go version by [Eduardo E. S. Riccardi](https://github.com/kuking/go-frodokem)
|
||||
|
||||
Currently supported session algorithms:
|
||||
|
|
@ -45,26 +37,10 @@ Currently supported session algorithms:
|
|||
* Blowfish-64
|
||||
* CryptMTv1 (64bit) (https://eprint.iacr.org/2005/165.pdf)
|
||||
* ChaCha20 (https://github.com/aead/chacha20)
|
||||
* HOPSCOTCH (https://gogs.blitter.com/Russtopia/hopscotch)
|
||||
|
||||
[HMAC]
|
||||
* HMAC-SHA256
|
||||
* HMAC-SHA512
|
||||
* WHIRLPOOL
|
||||
|
||||
***
|
||||
**A Note on 'cryptographic agility'**
|
||||
|
||||
It has been suggested recently to me that offering multiple cryptographic primitives is considered bad in 2021.
|
||||
|
||||
An interesting question. See [this write-up for a discussion](https://paragonie.com/blog/2019/10/against-agility-in-cryptography-protocols).
|
||||
|
||||
xs operates via the philosophy that **it is the server admin's prerogitive to configure local policy wrt. allowed cryptographic primitives**. The connection protocol makes no allowance for any sort of 'downgrades' or algo substitution during negotiation; there is no 'fallback' mode or two-way negotiation of what primitives to use, which would open the possibility of downgrade attacks. Unlike `ssh`, the server does not offer to clients a list of supported algorithms; the client can only offer a single configuration to the server, which it simply accepts or rejects without comment to the client.
|
||||
|
||||
In all releases prior to v0.9.3, absent a specific whitelist of algs to allow, the server allows 'all' combinations of the above cryptographic primitives to be proposed by clients (but again, **only one** combination is proposed by the client in a single connect attempt). If the admin wishes to restrict the accepted algorithms now or at any future time, they may use the `-aK`, `-aC` and `-aH` options when launching the server to define a whitelist which excludes certain primitives.
|
||||
|
||||
As of release v0.9.3, the default when supplying no explicit KEX, cipher or HMAC algorithms to `xsd` results in *no* algs being accepted; so the admin must decide on a specific whitelist of algorithms.
|
||||
***
|
||||
|
||||
|
||||
### Conn
|
||||
|
|
@ -95,34 +71,35 @@ KYBER IND-CCA-2 KEM
|
|||
|
||||
As of this time (Oct 2018) Kyber is one of the candidate algorithms submitted to the [NIST post-quantum cryptography project](https://csrc.nist.gov/Projects/Post-Quantum-Cryptography). The authors recommend using it in "... so-called hybrid mode in combination with established "pre-quantum" security; for example in combination with elliptic-curve Diffie-Hellman." THIS PROJECT DOES NOT DO THIS (in case you didn't notice yet, THIS PROJECT IS EXPERIMENTAL.)
|
||||
|
||||
### Dependencies:
|
||||
|
||||
### Installing
|
||||
|
||||
As of Go 1.8, one can directly use `go install` to get the client `xs` and server `xsd` binaries; however it is not recommended, as `xsd` requires root and for general use should be in one of the system directories, akin to other daemons. If one insists, the following will work to place them in $HOME/go/bin:
|
||||
|
||||
```
|
||||
$ go install blitter.com/go/xs/xs@latest
|
||||
$ go install blitter.com/go/xs/xsd@latest
|
||||
```
|
||||
|
||||
(NOTE the `-v` (version) option for binaries obtained in this manner will be blank; another reason to build them yourself locally using the steps below.)
|
||||
|
||||
* Recent version of go (tested, at various times, with go-1.9 to go-1.12.4)
|
||||
* [github.com/mattn/go-isatty](http://github.com/mattn/go-isatty) //terminal tty detection
|
||||
* [github.com/kr/pty](http://github.com/kr/pty) //unix pty control (server pty connections)
|
||||
* [github.com/jameskeane/bcrypt](http://github.com/jameskeane/bcrypt) //password storage/auth
|
||||
* [blitter.com/go/goutmp](https://gogs.blitter.com/RLabs/goutmp) // wtmp/lastlog C bindings for user accounting
|
||||
* [https://git.schwanenlied.me/yawning/kyber](https://git.schwanenlied.me/yawning/kyber) // golang Kyber KEM
|
||||
* [https://git.schwanenlied.me/yawning/newhope](https://git.schwanenlied.me/yawning/newhope) // golang NEWHOPE,NEWHOPE-SIMPLE KEX
|
||||
* [blitter.com/go/mtwist](https://gogs.blitter.com/RLabs/mtwist) // 64-bit Mersenne Twister PRNG
|
||||
* [blitter.com/go/cryptmt](https://gogs.blitter.com/RLabs/cryptmt) // CryptMTv1 stream cipher
|
||||
|
||||
### Get source code
|
||||
|
||||
```
|
||||
$ git clone https://gogs.blitter.com/RLabs/xs
|
||||
$ go get -u blitter.com/go/xs
|
||||
$ cd $GOPATH/src/blitter.com/go/xs
|
||||
$ go build ./... # install all dependent go pkgs
|
||||
```
|
||||
|
||||
|
||||
### To build
|
||||
|
||||
```
|
||||
$ cd xs
|
||||
$ make clean && make
|
||||
$ cd $GOPATH/src/blitter.com/go/xs
|
||||
$ make clean all
|
||||
```
|
||||
|
||||
### To install, uninstall, re-install (xsd server)
|
||||
### To install, uninstall, re-install
|
||||
|
||||
```
|
||||
$ sudo make [install | uninstall | reinstall]
|
||||
|
|
@ -150,10 +127,9 @@ The make system assumes installation in /usr/local/sbin (xsd, xspasswd) and /usr
|
|||
|
||||
```
|
||||
$ sudo rc-config [start | restart | stop] xsd
|
||||
# .. or sudo /etc/init.d/xsd [start | restart stop]
|
||||
```
|
||||
|
||||
### To set accounts & passwords (DEPRECATED: `-s` is now true by default)
|
||||
### To set accounts & passwords:
|
||||
|
||||
```
|
||||
$ sudo touch /etc/xs.passwd
|
||||
|
|
@ -188,18 +164,10 @@ or is interrupted.
|
|||
### Setting up an 'authtoken' for scripted (password-free) logins
|
||||
|
||||
Use the -g option of xs to request a token from the remote server, which will return a
|
||||
hostname:token string. Place this string into $HOME/.config/xs/.xs_id to allow logins without
|
||||
entering a password (obviously, $HOME/.config/xs/.xs_id on both server and client for the user
|
||||
hostname:token string. Place this string into $HOME/.xs_id to allow logins without
|
||||
entering a password (obviously, $HOME/.xs_id on both server and client for the user
|
||||
should *not* be world-readable.)
|
||||
|
||||
```
|
||||
$ xs -g user@host.net >>~/.config/xs/.xs_id
|
||||
```
|
||||
[enter password blindly, authtoken entry will be stored in ~/.config/xs/.xs_id]
|
||||
|
||||
NOTE you may need to remove older entries for the same host if this is not the first time you have added
|
||||
it to your .xs_id file.
|
||||
|
||||
### File Copying using xc
|
||||
|
||||
xc is a symlink to xs, and the binary checks its own filename to determine whether
|
||||
|
|
@ -211,12 +179,6 @@ If no leading / is specified in src-or-dest-path, it is assumed to be relative t
|
|||
remote user. File operations are all performed as the remote user, so account permissions apply
|
||||
as expected.
|
||||
|
||||
When running under MSYS2, one must set the MINGW_ROOT environment variable to assist in
|
||||
determining how to convert Windows paths to UNIX-style paths. This should be the installation path
|
||||
of one's MSYS2 environment (eg., _C:/msys2_). Go's stdlib, under the hood, still uses Windows
|
||||
style paths (drive letters and all) to locate other executables and _xc_ uses _tar_ as part of the copy
|
||||
functionality.
|
||||
|
||||
Local (client) to remote (server) copy:
|
||||
```
|
||||
$ xc fileA /some/where/fileB /some/where/else/dirC joebloggs@host-or-ip:remoteDir
|
||||
|
|
@ -233,19 +195,9 @@ NOTE: Renaming while copying (eg., 'cp /foo/bar/fileA ./fileB') is NOT supported
|
|||
|
||||
If the 'pv' pipeview utility is available (http://www.ivarch.com/programs/pv.shtml) file transfer progress and bandwidth control will be available (suppress the former with the -q option, set the latter with -L <bytes_per_second>).
|
||||
|
||||
Special care should be taken when doing client → server copies: since the tarpipe (should) always succeed at least sending data to the remote side, a destination with no write permission will not return a nonzero status and the client closes its end after sending all data, giving the server no opportunity to send an error code to the client.
|
||||
It is recommended to test beforehand if the server-side destination is writable (and optionally if the destination already exists, if one does not want to clobber an existing path) by:
|
||||
|
||||
```
|
||||
$ xs -x "test -w /dest/path" me@myserver ## If clobbering /dest/path is OK, or
|
||||
$ xs -x "test -w /dest/path -o ! -e /dest/path" me@myserver ## To prevent clobbering
|
||||
```
|
||||
|
||||
Perhaps in future a more complex handshake will be devised to allow the client to half-close the tarpipe, allowing the server to complete its side of the operation and send back its success or failure code, but the current connection protocol does not allow this. If this is a deal-breaking feature, please contact the maintainer.
|
||||
|
||||
### Tunnels
|
||||
|
||||
Simple tunnels (client → server, no reverse tunnels for now) are supported.
|
||||
Simple tunnels (client -> server, no reverse tunnels for now) are supported.
|
||||
|
||||
Syntax: xs -T=<tunspec>{,<tunspec>...}
|
||||
.. where <tunspec> is <localport:remoteport>
|
||||
|
|
|
|||
|
|
@ -2,7 +2,7 @@ package xs
|
|||
|
||||
// Package xs - a secure terminal client/server written from scratch in Go
|
||||
//
|
||||
// Copyright (c) 2017-2025 Russell Magee
|
||||
// Copyright (c) 2017-2020 Russell Magee
|
||||
// Licensed under the terms of the MIT license (see LICENSE.mit in this
|
||||
// distribution)
|
||||
//
|
||||
|
|
@ -23,7 +23,6 @@ import (
|
|||
"runtime"
|
||||
"strings"
|
||||
|
||||
"blitter.com/go/xs/xsnet"
|
||||
"github.com/jameskeane/bcrypt"
|
||||
passlib "gopkg.in/hlandau/passlib.v1"
|
||||
)
|
||||
|
|
@ -53,7 +52,7 @@ func VerifyPass(ctx *AuthCtx, user, password string) (bool, error) {
|
|||
} else if runtime.GOOS == "freebsd" {
|
||||
pwFileName = "/etc/master.passwd"
|
||||
} else {
|
||||
return false, errors.New("Unsupported platform")
|
||||
pwFileName = "unsupported"
|
||||
}
|
||||
pwFileData, e := ctx.reader(pwFileName)
|
||||
if e != nil {
|
||||
|
|
@ -155,7 +154,7 @@ func AuthUserByPasswd(ctx *AuthCtx, username string, auth string, fname string)
|
|||
// ------------- End xs-local passwd auth routine(s) -----------
|
||||
|
||||
// AuthUserByToken checks user login information against an auth token.
|
||||
// Auth tokens are stored in each user's $HOME/.config/xs/.xs_id and are requested
|
||||
// Auth tokens are stored in each user's $HOME/.xs_id and are requested
|
||||
// via the -g option.
|
||||
// The function also check system /etc/passwd to cross-check the user
|
||||
// actually exists.
|
||||
|
|
@ -173,9 +172,9 @@ func AuthUserByToken(ctx *AuthCtx, username string, connhostname string, auth st
|
|||
return false
|
||||
}
|
||||
|
||||
b, e := ctx.reader(fmt.Sprintf("%s/%s", u.HomeDir, xsnet.XS_ID_AUTHTOKFILE))
|
||||
b, e := ctx.reader(fmt.Sprintf("%s/.xs_id", u.HomeDir))
|
||||
if e != nil {
|
||||
log.Printf("INFO: Cannot read %s/%s\n", u.HomeDir, xsnet.XS_ID_AUTHTOKFILE)
|
||||
log.Printf("INFO: Cannot read %s/.xs_id\n", u.HomeDir)
|
||||
return false
|
||||
}
|
||||
|
||||
|
|
@ -183,27 +182,19 @@ func AuthUserByToken(ctx *AuthCtx, username string, connhostname string, auth st
|
|||
|
||||
r.Comma = ':'
|
||||
r.Comment = '#'
|
||||
r.FieldsPerRecord = 3 // connhost:username:authtoken
|
||||
r.FieldsPerRecord = 2 // connhost:authtoken
|
||||
for {
|
||||
record, err := r.Read()
|
||||
if err == io.EOF {
|
||||
return false
|
||||
}
|
||||
if len(record) < 3 ||
|
||||
len(record[0]) < 1 ||
|
||||
len(record[1]) < 1 ||
|
||||
len(record[2]) < 1 {
|
||||
return false
|
||||
}
|
||||
record[0] = strings.TrimSpace(record[0])
|
||||
record[1] = strings.TrimSpace(record[1])
|
||||
record[2] = strings.TrimSpace(record[2])
|
||||
//fmt.Println("auth:", auth, "record:",
|
||||
// strings.Join([]string{record[0], record[1], record[2]}, ":"))
|
||||
// strings.Join([]string{record[0], record[1]}, ":"))
|
||||
|
||||
if (connhostname == record[0]) &&
|
||||
username == record[1] &&
|
||||
(auth == strings.Join([]string{record[0], record[1], record[2]}, ":")) {
|
||||
(auth == strings.Join([]string{record[0], record[1]}, ":")) {
|
||||
valid = true
|
||||
break
|
||||
}
|
||||
|
|
@ -215,42 +206,22 @@ func AuthUserByToken(ctx *AuthCtx, username string, connhostname string, auth st
|
|||
return
|
||||
}
|
||||
|
||||
func GroomFsPath(path string) (ret string) {
|
||||
pathRoot := os.Getenv("MINGW_ROOT")
|
||||
if pathRoot != "" {
|
||||
ret = path[len(pathRoot):]
|
||||
ret = strings.ReplaceAll(ret, "\\", "/")
|
||||
} else {
|
||||
ret = path
|
||||
}
|
||||
//fmt.Printf("groomed fspath:%v\n", ret)
|
||||
return
|
||||
}
|
||||
|
||||
func GetTool(tool string) (ret string) {
|
||||
cmdSuffix := ""
|
||||
pathRoot := os.Getenv("MINGW_ROOT")
|
||||
|
||||
if pathRoot != "" {
|
||||
cmdSuffix = ".exe"
|
||||
}
|
||||
|
||||
//fmt.Printf("pathRoot:%v cmdSuffix:%v\n", pathRoot, cmdSuffix)
|
||||
|
||||
ret = pathRoot + "/bin/" + tool + cmdSuffix
|
||||
ret = "/bin/"+tool
|
||||
_, err := os.Stat(ret)
|
||||
if err == nil {
|
||||
return ret
|
||||
}
|
||||
ret = pathRoot + "/usr/bin/" + tool + cmdSuffix
|
||||
ret = "/usr/bin/"+tool
|
||||
_, err = os.Stat(ret)
|
||||
if err == nil {
|
||||
return ret
|
||||
}
|
||||
ret = pathRoot + "/usr/local/bin/" + tool + cmdSuffix
|
||||
ret = "/usr/local/bin/"+tool
|
||||
_, err = os.Stat(ret)
|
||||
if err == nil {
|
||||
return ret
|
||||
}
|
||||
return ""
|
||||
}
|
||||
|
||||
|
|
|
|||
|
|
@ -19,7 +19,7 @@ var (
|
|||
joebloggs:$6$F.0IXOrb0w0VJHG1$3O4PYyng7F3hlh42mbroEdQZvslybY5etPPiLMQJ1xosjABY.Q4xqAfyIfe03Du61ZjGQIt3nL0j12P9k1fsK/:18310:0:99999:7:::
|
||||
disableduser:!:18310::::::`
|
||||
|
||||
dummyAuthTokenFile = "hostA:johndoe:abcdefg\nhostB:imposter:wxyz\n"
|
||||
dummyAuthTokenFile = "hostA:abcdefg\nhostB:wxyz\n"
|
||||
|
||||
dummyXsPasswdFile = `#username:salt:authCookie
|
||||
bobdobbs:$2a$12$9vqGkFqikspe/2dTARqu1O:$2a$12$9vqGkFqikspe/2dTARqu1OuDKCQ/RYWsnaFjmi.HtmECRkxcZ.kBK
|
||||
|
|
@ -155,7 +155,7 @@ func TestAuthUserByTokenSucceedsWithMatchedUserAndToken(t *testing.T) {
|
|||
ctx := newMockAuthCtx(_mock_ioutil_ReadFile, _mock_user_Lookup)
|
||||
userlookup_arg_u = "johndoe"
|
||||
readfile_arg_f = "/.xs_id"
|
||||
stat := AuthUserByToken(ctx, userlookup_arg_u, "hostA", "hostA:johndoe:abcdefg")
|
||||
stat := AuthUserByToken(ctx, userlookup_arg_u, "hostA", "hostA:abcdefg")
|
||||
if !stat {
|
||||
t.Fatal("failed with valid user and token")
|
||||
}
|
||||
|
|
|
|||
|
|
@ -4,10 +4,9 @@
|
|||
|
||||
export GOPATH="${HOME}/go"
|
||||
export PATH=/usr/local/bin:/usr/bin:/usr/lib/ccache/bin:/bin:$GOPATH/bin
|
||||
unset GO111MODULE
|
||||
#export GOPROXY="direct"
|
||||
#!# GOCACHE will be phased out in v1.12. [github.com/golang/go/issues/26809]
|
||||
#!export GOCACHE="${HOME}/.cache/go-build"
|
||||
export GO111MODULE=on
|
||||
# GOCACHE will be phased out in v1.12. [github.com/golang/go/issues/26809]
|
||||
export GOCACHE="${HOME}/.cache/go-build"
|
||||
|
||||
echo "workdir: ${BACILLUS_WORKDIR}"
|
||||
mkdir -p "${BACILLUS_ARTFDIR}"
|
||||
|
|
@ -25,46 +24,25 @@ echo "Building most recent push on branch $branch"
|
|||
git checkout "$branch"
|
||||
ls
|
||||
|
||||
#!############
|
||||
#!stage "GoMod"
|
||||
#!############
|
||||
#!go clean -modcache
|
||||
#!
|
||||
#!rm -f go.{mod,sum}
|
||||
#!go mod init blitter.com/go/xs
|
||||
#!go mod tidy
|
||||
#!echo "---"
|
||||
|
||||
############
|
||||
stage "Build"
|
||||
############
|
||||
echo "Invoking 'make clean' ..."
|
||||
make clean
|
||||
echo "Invoking 'make all' ..."
|
||||
make all
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "Lint"
|
||||
############
|
||||
make lint
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "UnitTests"
|
||||
############
|
||||
go test -v .
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "Test(Authtoken)"
|
||||
############
|
||||
if [ -f ~/.config/xs/.xs_id ]; then
|
||||
echo "Clearing test user $USER .xs_id file ..."
|
||||
mv ~/.config/xs/.xs_id ~/.config/xs/.xs_id.bak
|
||||
if [ -f ~/.xs_id ]; then
|
||||
echo "Clearing test user $USER ~/.xs_id file ..."
|
||||
mv ~/.xs_id ~/.xs_id.bak
|
||||
fi
|
||||
echo "Setting dummy authtoken in .xs_id ..."
|
||||
echo "localhost:${USER}:asdfasdfasdf" >~/.config/xs/.xs_id
|
||||
echo "Setting dummy authtoken in ~/.xs_id ..."
|
||||
echo "localhost:asdfasdfasdf" >~/.xs_id
|
||||
echo "Performing remote command on @localhost via authtoken login ..."
|
||||
tokentest=$(timeout 10 xs -x "echo -n FOO" @localhost)
|
||||
if [ "${tokentest}" != "FOO" ]; then
|
||||
|
|
@ -74,14 +52,11 @@ else
|
|||
echo "client cmd performed OK."
|
||||
unset tokentest
|
||||
fi
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "Test(xc S->C)"
|
||||
stage "Test(S->C)"
|
||||
############
|
||||
echo "Testing secure copy from server -> client ..."
|
||||
./xc_testfiles.sh
|
||||
|
||||
tmpdir=$$
|
||||
mkdir -p /tmp/$tmpdir
|
||||
cd /tmp/$tmpdir
|
||||
|
|
@ -99,30 +74,32 @@ else
|
|||
echo "FAILED!"
|
||||
exit $stat
|
||||
fi
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "Test(xc C->S)"
|
||||
stage "Test(C->S)"
|
||||
############
|
||||
echo "TODO ..."
|
||||
|
||||
if [ -f ~/.config/xs/.xs_id.bak ]; then
|
||||
echo "Restoring test user $USER .xs_id file ..."
|
||||
mv ~/.config/xs/.xs_id.bak ~/.config/xs/.xs_id
|
||||
if [ -f ~/.xs_id.bak ]; then
|
||||
echo "Restoring test user $USER ~/.xs_id file ..."
|
||||
mv ~/.xs_id.bak ~/.xs_id
|
||||
fi
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "Lint"
|
||||
############
|
||||
make lint
|
||||
|
||||
############
|
||||
stage "Artifacts"
|
||||
############
|
||||
echo -n "Creating tarfile ..."
|
||||
tar -cz --exclude=.git --exclude=cptest -f ${BACILLUS_ARTFDIR}/xs.tgz .
|
||||
echo "---"
|
||||
|
||||
############
|
||||
stage "Cleanup"
|
||||
############
|
||||
rm -rf cptest
|
||||
# nop
|
||||
|
||||
echo
|
||||
echo "--Done--"
|
||||
|
|
|
|||
2295
capabilities.json
2295
capabilities.json
File diff suppressed because it is too large
Load Diff
|
|
@ -1,6 +1,6 @@
|
|||
// Package xs - a secure terminal client/server written from scratch in Go
|
||||
//
|
||||
// Copyright (c) 2017-2025 Russell Magee
|
||||
// Copyright (c) 2017-2020 Russell Magee
|
||||
// Licensed under the terms of the MIT license (see LICENSE.mit in this
|
||||
// distribution)
|
||||
//
|
||||
|
|
|
|||
|
|
@ -1,6 +1,6 @@
|
|||
6010a446cdcf8c1203c2d08998cc69a8c88f77d5 cptest/file16KB
|
||||
f086ea96f3718efd78e6791178f967585acb3701 cptest/file1KB
|
||||
6061e16c3d3840712d0b8e5268c49b5c2f8137ac cptest/file32KB
|
||||
490af32035bbe737480f06439a02d91a171ac407 cptest/file6B
|
||||
e4a8a4ad9678b7265a28c5f0cb5b078e1049ea23 cptest/subdir/file32MB
|
||||
82b50550c7d0e0d6ac18d9d0796b6814c3e038bf cptest/subdir/file64MB
|
||||
306637b5c621892078ebadd9454a78820a000598 cptest/file16KB
|
||||
1a118dfff291352eb4aec02c34f4f957669460fc cptest/file1KB
|
||||
f474d5da45890b7cb5b0ae84c8ade5abcb3b4474 cptest/file32KB
|
||||
03939175ceac92b9c6464d037a0243e22563c423 cptest/file6B
|
||||
da67c7698b25d94c0cc20284ba9d4008cdee201b cptest/subdir/file32MB
|
||||
9da9888265371375b48c224b94a0b3132b7ddc41 cptest/subdir/file64MB
|
||||
|
|
|
|||
43
go.mod
43
go.mod
|
|
@ -1,37 +1,30 @@
|
|||
module blitter.com/go/xs
|
||||
|
||||
go 1.24.0
|
||||
go 1.12
|
||||
|
||||
require (
|
||||
blitter.com/go/cryptmt v1.0.3
|
||||
blitter.com/go/goutmp v1.0.6
|
||||
blitter.com/go/herradurakex v1.0.1
|
||||
blitter.com/go/hopscotch v0.3.0
|
||||
blitter.com/go/kyber v1.0.0
|
||||
blitter.com/go/newhope v1.0.0
|
||||
blitter.com/go/spinsult v0.0.0-20260224023031-2afae6bbe758
|
||||
blitter.com/go/cryptmt v1.0.2
|
||||
blitter.com/go/goutmp v1.0.5
|
||||
blitter.com/go/herradurakex v1.0.0
|
||||
blitter.com/go/kyber v0.0.0-20200130200857-6f2021cb88d9
|
||||
blitter.com/go/mtwist v1.0.1 // indirect
|
||||
blitter.com/go/newhope v0.0.0-20200130200750-192fc08a8aae
|
||||
github.com/aead/chacha20 v0.0.0-20180709150244-8b13a72661da
|
||||
github.com/creack/pty v1.1.24
|
||||
github.com/creack/pty v1.1.11
|
||||
github.com/jameskeane/bcrypt v0.0.0-20120420032655-c3cd44c1e20f
|
||||
github.com/jzelinskie/whirlpool v0.0.0-20201016144138-0675e54bb004
|
||||
github.com/kuking/go-frodokem v1.0.2
|
||||
github.com/mattn/go-isatty v0.0.20
|
||||
github.com/xtaci/kcp-go v4.3.4+incompatible
|
||||
golang.org/x/crypto v0.48.0
|
||||
golang.org/x/sys v0.41.0
|
||||
gopkg.in/hlandau/passlib.v1 v1.0.11
|
||||
)
|
||||
|
||||
require (
|
||||
blitter.com/go/chacha20 v0.0.0-20200130200441-214e4085f54c // indirect
|
||||
blitter.com/go/mtwist v1.0.2 // indirect
|
||||
github.com/klauspost/cpuid/v2 v2.3.0 // indirect
|
||||
github.com/klauspost/reedsolomon v1.13.2 // indirect
|
||||
github.com/klauspost/reedsolomon v1.9.9 // indirect
|
||||
github.com/kuking/go-frodokem v1.0.1
|
||||
github.com/mattn/go-isatty v0.0.12
|
||||
github.com/mmcloughlin/avo v0.0.0-20200523190732-4439b6b2c061 // indirect
|
||||
github.com/pkg/errors v0.9.1 // indirect
|
||||
github.com/templexxx/cpufeat v0.0.0-20180724012125-cef66df7f161 // indirect
|
||||
github.com/templexxx/xor v0.0.0-20191217153810-f85b25db303b // indirect
|
||||
github.com/tjfoc/gmsm v1.4.1 // indirect
|
||||
golang.org/x/net v0.49.0 // indirect
|
||||
github.com/tjfoc/gmsm v1.3.1 // indirect
|
||||
github.com/xtaci/kcp-go v5.4.20+incompatible
|
||||
github.com/xtaci/lossyconn v0.0.0-20200209145036-adba10fffc37 // indirect
|
||||
golang.org/x/crypto v0.0.0-20200510223506-06a226fb4e37
|
||||
golang.org/x/sys v0.0.0-20200523222454-059865788121
|
||||
gopkg.in/hlandau/easymetric.v1 v1.0.0 // indirect
|
||||
gopkg.in/hlandau/measurable.v1 v1.0.1 // indirect
|
||||
gopkg.in/hlandau/passlib.v1 v1.0.10
|
||||
)
|
||||
|
|
|
|||
172
go.sum
172
go.sum
|
|
@ -1,144 +1,94 @@
|
|||
blitter.com/go/chacha20 v0.0.0-20200130200441-214e4085f54c h1:LcnFFg6MCIJHf26P7eOUST45fNLHJI5erq0gWZaDLCo=
|
||||
blitter.com/go/chacha20 v0.0.0-20200130200441-214e4085f54c/go.mod h1:EMJtRcf22WCtHGiXCw+NB/Sb/PYcXtUgUql6LDEwyXo=
|
||||
blitter.com/go/cryptmt v1.0.3 h1:C1j55/TV8301jROxn83Zlm+qNH3/XUSzBoTrbBGD8gw=
|
||||
blitter.com/go/cryptmt v1.0.3/go.mod h1:otZPP0Vps15DRZNo2zD4RLym+IT6XnbtI1HS412BxHM=
|
||||
blitter.com/go/goutmp v1.0.6 h1:jRKRw2WalVBza4T50etAfbvT2xp9G5uykIHTvyB5r0k=
|
||||
blitter.com/go/goutmp v1.0.6/go.mod h1:DnK/uLBu1/1yLFiuVlmwvWErzAWVp+pDv7t6ZaQRLNc=
|
||||
blitter.com/go/herradurakex v1.0.1 h1:7smv+RiG6PQ2hHebT/uSjIKcisp/lx5PSCBn8fISHWA=
|
||||
blitter.com/go/herradurakex v1.0.1/go.mod h1:m3+vYZX+2dDjdo+n/HDnXEYJX9pwmNeQLgAfJM8mtxw=
|
||||
blitter.com/go/hopscotch v0.3.0 h1:IaPdMXyZ1mjU6UHzMiWgu1PF8/5r7ElVTeTLliWqxbw=
|
||||
blitter.com/go/hopscotch v0.3.0/go.mod h1:hCz7oE31KjaO9M6+s2DcyVNlAA8saE/AaVYKFs7hl1I=
|
||||
blitter.com/go/kyber v1.0.0 h1:xniqw15FUrmR1bTqwH57cIZ0Ko2kYcINnSRE3ESzA9M=
|
||||
blitter.com/go/kyber v1.0.0/go.mod h1:xE277hhExsmBIaVT7oFgNfkXC3ioHaZCTreNJHSCwqw=
|
||||
blitter.com/go/mtwist v1.0.2 h1:4zmpKNynrRuFF8JAPdhBN8TaJB+quU5d2i7KBgFtVng=
|
||||
blitter.com/go/mtwist v1.0.2/go.mod h1:Y/0x0EsFMUKK1+tdkoCW7H88eF7CTOycUMsTHcfCoZE=
|
||||
blitter.com/go/newhope v1.0.0 h1:oUn35Ei30AGmLeqjNIG6DA7YNaK7fncBx4ptTnNrzmo=
|
||||
blitter.com/go/newhope v1.0.0/go.mod h1:ywoxfDBqInPsqtnxYsmS4SYMJ5D/kNcrFgpvI+Xcun0=
|
||||
blitter.com/go/spinsult v0.0.0-20260224023031-2afae6bbe758 h1:6CYxkKMXehsanwg0/G4q1K/+M+pYhfcv49ngfsmLtyk=
|
||||
blitter.com/go/spinsult v0.0.0-20260224023031-2afae6bbe758/go.mod h1:/EchWRYRoJvzxpR6Pt6tSpQ9X4bjhF4BOppXYsZa16I=
|
||||
cloud.google.com/go v0.26.0/go.mod h1:aQUYkXzVsufM+DwF1aE+0xfcU+56JwCaLick0ClmMTw=
|
||||
github.com/BurntSushi/toml v0.3.1/go.mod h1:xHWCNGjB5oqiDr8zfno3MHue2Ht5sIBksp03qcyfWMU=
|
||||
blitter.com/go/cryptmt v1.0.2 h1:ZcLhQk7onUssXyQwG3GdXDXctCVnNL+b7aFuvwOdKXc=
|
||||
blitter.com/go/cryptmt v1.0.2/go.mod h1:tdME2J3O4agaDAYIYNQzzuB28yVGnPSMmV3a/ucSU84=
|
||||
blitter.com/go/goutmp v1.0.5 h1:isP6bxSs1O06Oy7wB8u4y5SgLr22txfjg/gjG4qn0Og=
|
||||
blitter.com/go/goutmp v1.0.5/go.mod h1:gtlbjC8xGzMk/Cf0BpnVltSa3awOqJ+B5WAxVptTMxk=
|
||||
blitter.com/go/herradurakex v1.0.0 h1:6XaxY+JLT1HUWPF0gYJnjX3pVjrw4YhYZEzZ1U0wkyc=
|
||||
blitter.com/go/herradurakex v1.0.0/go.mod h1:m3+vYZX+2dDjdo+n/HDnXEYJX9pwmNeQLgAfJM8mtxw=
|
||||
blitter.com/go/kyber v0.0.0-20200130200857-6f2021cb88d9 h1:D45AnrNphtvczBXRp5JQicZRTgaK/Is5bgPDDvRKhTc=
|
||||
blitter.com/go/kyber v0.0.0-20200130200857-6f2021cb88d9/go.mod h1:SK6QfGG72lIfKW1Td0wH7f0wwN5nSIhV3K+wvzGNjrw=
|
||||
blitter.com/go/mtwist v1.0.1 h1:PxmoWexfMpLmc8neHP/PcRc3s17ct7iz4d5W/qJVt04=
|
||||
blitter.com/go/mtwist v1.0.1/go.mod h1:aU82Nx8+b1v8oZRNqImfEDzDTPim81rY0ACKAIclV18=
|
||||
blitter.com/go/newhope v0.0.0-20200130200750-192fc08a8aae h1:YBBaCcdYRrI1btsmcMTv1VMPmaSXXz0RwKOTgMJYSRU=
|
||||
blitter.com/go/newhope v0.0.0-20200130200750-192fc08a8aae/go.mod h1:ywoxfDBqInPsqtnxYsmS4SYMJ5D/kNcrFgpvI+Xcun0=
|
||||
github.com/aead/chacha20 v0.0.0-20180709150244-8b13a72661da h1:KjTM2ks9d14ZYCvmHS9iAKVt9AyzRSqNU1qabPih5BY=
|
||||
github.com/aead/chacha20 v0.0.0-20180709150244-8b13a72661da/go.mod h1:eHEWzANqSiWQsof+nXEI9bUVUyV6F53Fp89EuCh2EAA=
|
||||
github.com/census-instrumentation/opencensus-proto v0.2.1/go.mod h1:f6KPmirojxKA12rnyqOA5BBL4O983OfeGPqjHWSTneU=
|
||||
github.com/client9/misspell v0.3.4/go.mod h1:qj6jICC3Q7zFZvVWo7KLAzC3yx5G7kyvSDkc90ppPyw=
|
||||
github.com/cncf/udpa/go v0.0.0-20191209042840-269d4d468f6f/go.mod h1:M8M6+tZqaGXZJjfX53e64911xZQV5JYwmTeXPW+k8Sc=
|
||||
github.com/creack/pty v1.1.24 h1:bJrF4RRfyJnbTJqzRLHzcGaZK1NeM5kTC9jGgovnR1s=
|
||||
github.com/creack/pty v1.1.24/go.mod h1:08sCNb52WyoAwi2QDyzUCTgcvVFhUzewun7wtTfvcwE=
|
||||
github.com/creack/pty v1.1.11 h1:07n33Z8lZxZ2qwegKbObQohDhXDQxiMMz1NOUGYlesw=
|
||||
github.com/creack/pty v1.1.11/go.mod h1:oKZEueFk5CKHvIhNR5MUki03XCEU+Q6VDXinZuGJ33E=
|
||||
github.com/davecgh/go-spew v1.1.0 h1:ZDRjVQ15GmhC3fiQ8ni8+OwkZQO4DARzQgrnXU1Liz8=
|
||||
github.com/davecgh/go-spew v1.1.0/go.mod h1:J7Y8YcW2NihsgmVo/mv3lAwl/skON4iLHjSsI+c5H38=
|
||||
github.com/davecgh/go-spew v1.1.1 h1:vj9j/u1bqnvCEfJOwUhtlOARqs3+rkHYY13jYWTU97c=
|
||||
github.com/davecgh/go-spew v1.1.1/go.mod h1:J7Y8YcW2NihsgmVo/mv3lAwl/skON4iLHjSsI+c5H38=
|
||||
github.com/envoyproxy/go-control-plane v0.9.0/go.mod h1:YTl/9mNaCwkRvm6d1a2C3ymFceY/DCBVvsKhRF0iEA4=
|
||||
github.com/envoyproxy/go-control-plane v0.9.4/go.mod h1:6rpuAdCZL397s3pYoYcLgu1mIlRU8Am5FuJP05cCM98=
|
||||
github.com/envoyproxy/protoc-gen-validate v0.1.0/go.mod h1:iSmxcyjqTsJpI2R4NaDN7+kN2VEUnK/pcBlmesArF7c=
|
||||
github.com/golang/glog v0.0.0-20160126235308-23def4e6c14b/go.mod h1:SBH7ygxi8pfUlaOkMMuAQtPIUF8ecWP5IEl/CR7VP2Q=
|
||||
github.com/golang/mock v1.1.1/go.mod h1:oTYuIxOrZwtPieC+H1uAHpcLFnEyAGVDL/k47Jfbm0A=
|
||||
github.com/golang/protobuf v1.2.0/go.mod h1:6lQm79b+lXiMfvg/cZm0SGofjICqVBUtrP5yJMmIC1U=
|
||||
github.com/golang/protobuf v1.3.2/go.mod h1:6lQm79b+lXiMfvg/cZm0SGofjICqVBUtrP5yJMmIC1U=
|
||||
github.com/golang/protobuf v1.3.3/go.mod h1:vzj43D7+SQXF/4pzW/hwtAqwc6iTitCiVSaWz5lYuqw=
|
||||
github.com/golang/protobuf v1.4.0-rc.1/go.mod h1:ceaxUfeHdC40wWswd/P6IGgMaK3YpKi5j83Wpe3EHw8=
|
||||
github.com/golang/protobuf v1.4.0-rc.1.0.20200221234624-67d41d38c208/go.mod h1:xKAWHe0F5eneWXFV3EuXVDTCmh+JuBKY0li0aMyXATA=
|
||||
github.com/golang/protobuf v1.4.0-rc.2/go.mod h1:LlEzMj4AhA7rCAGe4KMBDvJI+AwstrUpVNzEA03Pprs=
|
||||
github.com/golang/protobuf v1.4.0-rc.4.0.20200313231945-b860323f09d0/go.mod h1:WU3c8KckQ9AFe+yFwt9sWVRKCVIyN9cPHBJSNnbL67w=
|
||||
github.com/golang/protobuf v1.4.0/go.mod h1:jodUvKwWbYaEsadDk5Fwe5c77LiNKVO9IDvqG2KuDX0=
|
||||
github.com/golang/protobuf v1.4.2/go.mod h1:oDoupMAO8OvCJWAcko0GGGIgR6R6ocIYbsSw735rRwI=
|
||||
github.com/google/go-cmp v0.2.0/go.mod h1:oXzfMopK8JAjlY9xF4vHSVASa0yLyX7SntLO5aqRK0M=
|
||||
github.com/google/go-cmp v0.3.0/go.mod h1:8QqcDgzrUqlUb/G2PQTWiueGozuR1884gddMywk6iLU=
|
||||
github.com/google/go-cmp v0.3.1/go.mod h1:8QqcDgzrUqlUb/G2PQTWiueGozuR1884gddMywk6iLU=
|
||||
github.com/google/go-cmp v0.4.0/go.mod h1:v8dTdLbMG2kIc/vJvl+f65V22dbkXbowE6jgT/gNBxE=
|
||||
github.com/jameskeane/bcrypt v0.0.0-20120420032655-c3cd44c1e20f h1:UWGE8Vi+1Agt0lrvnd7UsmvwqWKRzb9byK9iQmsbY0Y=
|
||||
github.com/jameskeane/bcrypt v0.0.0-20120420032655-c3cd44c1e20f/go.mod h1:u+9Snq0w+ZdYKi8BBoaxnEwWu0fY4Kvu9ByFpM51t1s=
|
||||
github.com/jzelinskie/whirlpool v0.0.0-20201016144138-0675e54bb004 h1:G+9t9cEtnC9jFiTxyptEKuNIAbiN5ZCQzX2a74lj3xg=
|
||||
github.com/jzelinskie/whirlpool v0.0.0-20201016144138-0675e54bb004/go.mod h1:KmHnJWQrgEvbuy0vcvj00gtMqbvNn1L+3YUZLK/B92c=
|
||||
github.com/klauspost/cpuid/v2 v2.3.0 h1:S4CRMLnYUhGeDFDqkGriYKdfoFlDnMtqTiI/sFzhA9Y=
|
||||
github.com/klauspost/cpuid/v2 v2.3.0/go.mod h1:hqwkgyIinND0mEev00jJYCxPNVRVXFQeu1XKlok6oO0=
|
||||
github.com/klauspost/reedsolomon v1.13.2 h1:9qtQy2tKEVpVB8Pfq87ZljHZb60/LbeTQ1OxV8EGzdE=
|
||||
github.com/klauspost/reedsolomon v1.13.2/go.mod h1:ggJT9lc71Vu+cSOPBlxGvBN6TfAS77qB4fp8vJ05NSA=
|
||||
github.com/kuking/go-frodokem v1.0.2 h1:sxdguENCyr6WnLbJ/cjz0AYCW75H1b+E6zXY2ldZnUU=
|
||||
github.com/kuking/go-frodokem v1.0.2/go.mod h1:83ZX1kHOd72ouCsvbffCqJIj7Ih83MQTAjH2QbqzLZk=
|
||||
github.com/mattn/go-isatty v0.0.20 h1:xfD0iDuEKnDkl03q4limB+vH+GxLEtL/jb4xVJSWWEY=
|
||||
github.com/mattn/go-isatty v0.0.20/go.mod h1:W+V8PltTTMOvKvAeJH7IuucS94S2C6jfK/D7dTCTo3Y=
|
||||
github.com/klauspost/cpuid v1.2.4 h1:EBfaK0SWSwk+fgk6efYFWdzl8MwRWoOO1gkmiaTXPW4=
|
||||
github.com/klauspost/cpuid v1.2.4/go.mod h1:Pj4uuM528wm8OyEC2QMXAi2YiTZ96dNQPGgoMS4s3ek=
|
||||
github.com/klauspost/reedsolomon v1.9.9 h1:qCL7LZlv17xMixl55nq2/Oa1Y86nfO8EqDfv2GHND54=
|
||||
github.com/klauspost/reedsolomon v1.9.9/go.mod h1:O7yFFHiQwDR6b2t63KPUpccPtNdp5ADgh1gg4fd12wo=
|
||||
github.com/kuking/go-frodokem v1.0.1 h1:13bks3u4CPpvUtOLttT+A37j9myV4kLnS7Z3qDiTm4o=
|
||||
github.com/kuking/go-frodokem v1.0.1/go.mod h1:TzD0W9QnVOcwigeSySEuNZfJaGxWRtFRb7hXe/w/waI=
|
||||
github.com/mattn/go-isatty v0.0.12 h1:wuysRhFDzyxgEmMf5xjvJ2M9dZoWAXNNr5LSBS7uHXY=
|
||||
github.com/mattn/go-isatty v0.0.12/go.mod h1:cbi8OIDigv2wuxKPP5vlRcQ1OAZbq2CE4Kysco4FUpU=
|
||||
github.com/mmcloughlin/avo v0.0.0-20200523190732-4439b6b2c061 h1:UCU8+cLbbvyxi0sQ9fSeoEhZgvrrD9HKMtX6Gmc1vk8=
|
||||
github.com/mmcloughlin/avo v0.0.0-20200523190732-4439b6b2c061/go.mod h1:wqKykBG2QzQDJEzvRkcS8x6MiSJkF52hXZsXcjaB3ls=
|
||||
github.com/pkg/errors v0.9.1 h1:FEBLx1zS214owpjy7qsBeixbURkuhQAwrK5UwLGTwt4=
|
||||
github.com/pkg/errors v0.9.1/go.mod h1:bwawxfHBFNV+L2hUp1rHADufV3IMtnDRdf1r5NINEl0=
|
||||
github.com/pmezard/go-difflib v1.0.0 h1:4DBwDE0NGyQoBHbLQYPwSUPoCMWR5BEzIk/f1lZbAQM=
|
||||
github.com/pmezard/go-difflib v1.0.0/go.mod h1:iKH77koFhYxTK1pcRnkKkqfTogsbg7gZNVY4sRDYZ/4=
|
||||
github.com/prometheus/client_model v0.0.0-20190812154241-14fe0d1b01d4/go.mod h1:xMI15A0UPsDsEKsMN9yxemIoYk6Tm2C1GtYGdfGttqA=
|
||||
github.com/stretchr/objx v0.1.0/go.mod h1:HFkY916IF+rwdDfMAkV7OtwuqBVzrE8GR6GFx+wExME=
|
||||
github.com/stretchr/testify v1.4.0 h1:2E4SXV/wtOkTonXsotYi4li6zVWxYlZuYNCXe9XRJyk=
|
||||
github.com/stretchr/testify v1.4.0/go.mod h1:j7eGeouHqKxXV5pUuKE4zz7dFj8WfuZ+81PSLYec5m4=
|
||||
github.com/stretchr/testify v1.10.0 h1:Xv5erBjTwe/5IxqUQTdXv5kgmIvbHo3QQyRwhJsOfJA=
|
||||
github.com/stretchr/testify v1.10.0/go.mod h1:r2ic/lqez/lEtzL7wO/rwa5dbSLXVDPFyf8C91i36aY=
|
||||
github.com/templexxx/cpufeat v0.0.0-20180724012125-cef66df7f161 h1:89CEmDvlq/F7SJEOqkIdNDGJXrQIhuIx9D2DBXjavSU=
|
||||
github.com/templexxx/cpufeat v0.0.0-20180724012125-cef66df7f161/go.mod h1:wM7WEvslTq+iOEAMDLSzhVuOt5BRZ05WirO+b09GHQU=
|
||||
github.com/templexxx/xor v0.0.0-20191217153810-f85b25db303b h1:fj5tQ8acgNUr6O8LEplsxDhUIe2573iLkJc+PqnzZTI=
|
||||
github.com/templexxx/xor v0.0.0-20191217153810-f85b25db303b/go.mod h1:5XA7W9S6mni3h5uvOC75dA3m9CCCaS83lltmc0ukdi4=
|
||||
github.com/tjfoc/gmsm v1.4.1 h1:aMe1GlZb+0bLjn+cKTPEvvn9oUEBlJitaZiiBwsbgho=
|
||||
github.com/tjfoc/gmsm v1.4.1/go.mod h1:j4INPkHWMrhJb38G+J6W4Tw0AbuN8Thu3PbdVYhVcTE=
|
||||
github.com/ulikunitz/xz v0.5.8 h1:ERv8V6GKqVi23rgu5cj9pVfVzJbOqAY2Ntl88O6c2nQ=
|
||||
github.com/ulikunitz/xz v0.5.8/go.mod h1:nbz6k7qbPmH4IRqmfOplQw/tblSgqTqBwxkY0oWt/14=
|
||||
github.com/xtaci/kcp-go v4.3.4+incompatible h1:T56s9GLhx+KZUn5T8aO2Didfa4uTYvjeVIRLt6uYdhE=
|
||||
github.com/xtaci/kcp-go v4.3.4+incompatible/go.mod h1:bN6vIwHQbfHaHtFpEssmWsN45a+AZwO7eyRCmEIbtvE=
|
||||
github.com/tjfoc/gmsm v1.3.1 h1:+k3IAlF81c31/TllJmIfuCYnjl8ziMdTWGWJcP9J1uo=
|
||||
github.com/tjfoc/gmsm v1.3.1/go.mod h1:HaUcFuY0auTiaHB9MHFGCPx5IaLhTUd2atbCFBQXn9w=
|
||||
github.com/ulikunitz/xz v0.5.7 h1:YvTNdFzX6+W5m9msiYg/zpkSURPPtOlzbqYjrFn7Yt4=
|
||||
github.com/ulikunitz/xz v0.5.7/go.mod h1:nbz6k7qbPmH4IRqmfOplQw/tblSgqTqBwxkY0oWt/14=
|
||||
github.com/xtaci/kcp-go v5.4.20+incompatible h1:TN1uey3Raw0sTz0Fg8GkfM0uH3YwzhnZWQ1bABv5xAg=
|
||||
github.com/xtaci/kcp-go v5.4.20+incompatible/go.mod h1:bN6vIwHQbfHaHtFpEssmWsN45a+AZwO7eyRCmEIbtvE=
|
||||
github.com/xtaci/lossyconn v0.0.0-20200209145036-adba10fffc37 h1:EWU6Pktpas0n8lLQwDsRyZfmkPeRbdgPtW609es+/9E=
|
||||
github.com/xtaci/lossyconn v0.0.0-20200209145036-adba10fffc37/go.mod h1:HpMP7DB2CyokmAh4lp0EQnnWhmycP/TvwBGzvuie+H0=
|
||||
github.com/yuin/goldmark v1.1.27/go.mod h1:3hX8gzYuyVAZsxl0MRgGTJEmQBFcNTphYh9decYSb74=
|
||||
golang.org/x/arch v0.0.0-20190909030613-46d78d1859ac/go.mod h1:flIaEI6LNU6xOCD5PaJvn9wGP0agmIOqjrtsKGRguv4=
|
||||
golang.org/x/crypto v0.0.0-20190308221718-c2843e01d9a2/go.mod h1:djNgcEr1/C05ACkg1iLfiJU5Ep61QUkGW8qpdssI0+w=
|
||||
golang.org/x/crypto v0.0.0-20190829043050-9756ffdc2472/go.mod h1:yigFU9vqHzYiE8UmvKecakEJjdnWj3jj499lnFckfCI=
|
||||
golang.org/x/crypto v0.0.0-20191011191535-87dc89f01550/go.mod h1:yigFU9vqHzYiE8UmvKecakEJjdnWj3jj499lnFckfCI=
|
||||
golang.org/x/crypto v0.0.0-20191219195013-becbf705a915/go.mod h1:LzIPMQfyMNhhGPhUkYOs5KpL4U8rLKemX1yGLhDgUto=
|
||||
golang.org/x/crypto v0.0.0-20200128174031-69ecbb4d6d5d/go.mod h1:LzIPMQfyMNhhGPhUkYOs5KpL4U8rLKemX1yGLhDgUto=
|
||||
golang.org/x/crypto v0.0.0-20200510223506-06a226fb4e37 h1:cg5LA/zNPRzIXIWSCxQW10Rvpy94aQh3LT/ShoCpkHw=
|
||||
golang.org/x/crypto v0.0.0-20200510223506-06a226fb4e37/go.mod h1:LzIPMQfyMNhhGPhUkYOs5KpL4U8rLKemX1yGLhDgUto=
|
||||
golang.org/x/crypto v0.0.0-20200622213623-75b288015ac9/go.mod h1:LzIPMQfyMNhhGPhUkYOs5KpL4U8rLKemX1yGLhDgUto=
|
||||
golang.org/x/crypto v0.0.0-20201012173705-84dcc777aaee/go.mod h1:LzIPMQfyMNhhGPhUkYOs5KpL4U8rLKemX1yGLhDgUto=
|
||||
golang.org/x/crypto v0.48.0 h1:/VRzVqiRSggnhY7gNRxPauEQ5Drw9haKdM0jqfcCFts=
|
||||
golang.org/x/crypto v0.48.0/go.mod h1:r0kV5h3qnFPlQnBSrULhlsRfryS2pmewsg+XfMgkVos=
|
||||
golang.org/x/exp v0.0.0-20190121172915-509febef88a4/go.mod h1:CJ0aWSM057203Lf6IL+f9T1iT9GByDxfZKAQTCR3kQA=
|
||||
golang.org/x/lint v0.0.0-20181026193005-c67002cb31c3/go.mod h1:UVdnD1Gm6xHRNCYTkRU2/jEulfH38KcIWyp/GAMgvoE=
|
||||
golang.org/x/lint v0.0.0-20190227174305-5b3e6a55c961/go.mod h1:wehouNa3lNwaWXcvxsM5YxQ5yQlVC4a0KAMCusXpPoU=
|
||||
golang.org/x/lint v0.0.0-20190313153728-d0100b6bd8b3/go.mod h1:6SW0HCj/g11FgYtHlgUYUwCkIfeOF89ocIRzGO/8vkc=
|
||||
golang.org/x/net v0.0.0-20180724234803-3673e40ba225/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4=
|
||||
golang.org/x/net v0.0.0-20180826012351-8a410e7b638d/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4=
|
||||
golang.org/x/net v0.0.0-20190213061140-3a22650c66bd/go.mod h1:mL1N/T3taQHkDXs73rZJwtUhF3w3ftmwwsq0BUmARs4=
|
||||
golang.org/x/net v0.0.0-20190311183353-d8887717615a/go.mod h1:t9HGtf8HONx5eT2rtn7q6eTqICYqUVnKs3thJo3Qplg=
|
||||
golang.org/x/mod v0.2.0 h1:KU7oHjnv3XNWfa5COkzUifxZmxp1TyI7ImMXqFxLwvQ=
|
||||
golang.org/x/mod v0.2.0/go.mod h1:s0Qsj1ACt9ePp/hMypM3fl4fZqREWJwdYDEqhRiZZUA=
|
||||
golang.org/x/net v0.0.0-20190404232315-eb5bcb51f2a3 h1:0GoQqolDA55aaLxZyTzK/Y2ePZzZTUrRacwib7cNsYQ=
|
||||
golang.org/x/net v0.0.0-20190404232315-eb5bcb51f2a3/go.mod h1:t9HGtf8HONx5eT2rtn7q6eTqICYqUVnKs3thJo3Qplg=
|
||||
golang.org/x/net v0.0.0-20201010224723-4f7140c49acb/go.mod h1:sp8m0HH+o8qH0wwXwYZr8TS3Oi6o0r6Gce1SSxlDquU=
|
||||
golang.org/x/net v0.49.0 h1:eeHFmOGUTtaaPSGNmjBKpbng9MulQsJURQUAfUwY++o=
|
||||
golang.org/x/net v0.49.0/go.mod h1:/ysNB2EvaqvesRkuLAyjI1ycPZlQHM3q01F02UY/MV8=
|
||||
golang.org/x/oauth2 v0.0.0-20180821212333-d2e6202438be/go.mod h1:N/0e6XlmueqKjAGxoOufVs8QHGRruUQn6yWY3a++T0U=
|
||||
golang.org/x/sync v0.0.0-20180314180146-1d60e4601c6f/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sync v0.0.0-20181108010431-42b317875d0f/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/net v0.0.0-20190620200207-3b0461eec859/go.mod h1:z5CRVTTTmAJ677TzLLGU+0bjPO0LkuOLi4/5GtJWs/s=
|
||||
golang.org/x/net v0.0.0-20200226121028-0de0cce0169b h1:0mm1VjtFUOIlE1SbDlwjYaDxZVDP2S5ou6y0gSgXHu8=
|
||||
golang.org/x/net v0.0.0-20200226121028-0de0cce0169b/go.mod h1:z5CRVTTTmAJ677TzLLGU+0bjPO0LkuOLi4/5GtJWs/s=
|
||||
golang.org/x/sync v0.0.0-20190423024810-112230192c58/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sys v0.0.0-20180830151530-49385e6e1522/go.mod h1:STP8DvDyc/dI5b8T5hshtkjS+E42TnysNCUPdjciGhY=
|
||||
golang.org/x/sync v0.0.0-20190911185100-cd5d95a43a6e/go.mod h1:RxMgew5VJxzue5/jJTE5uejpjVlOe/izrB70Jof72aM=
|
||||
golang.org/x/sys v0.0.0-20190215142949-d0b11bdaac8a/go.mod h1:STP8DvDyc/dI5b8T5hshtkjS+E42TnysNCUPdjciGhY=
|
||||
golang.org/x/sys v0.0.0-20190412213103-97732733099d/go.mod h1:h1NjWce9XRLGQEsW7wpKNCjG9DtNlClVuFLEZdDNbEs=
|
||||
golang.org/x/sys v0.0.0-20190902133755-9109b7679e13/go.mod h1:h1NjWce9XRLGQEsW7wpKNCjG9DtNlClVuFLEZdDNbEs=
|
||||
golang.org/x/sys v0.0.0-20200930185726-fdedc70b468f/go.mod h1:h1NjWce9XRLGQEsW7wpKNCjG9DtNlClVuFLEZdDNbEs=
|
||||
golang.org/x/sys v0.6.0/go.mod h1:oPkhp1MJrh7nUepCBck5+mAzfO9JrbApNNgaTdGDITg=
|
||||
golang.org/x/sys v0.41.0 h1:Ivj+2Cp/ylzLiEU89QhWblYnOE9zerudt9Ftecq2C6k=
|
||||
golang.org/x/sys v0.41.0/go.mod h1:OgkHotnGiDImocRcuBABYBEXf8A9a87e/uXjp9XT3ks=
|
||||
golang.org/x/sys v0.0.0-20200116001909-b77594299b42/go.mod h1:h1NjWce9XRLGQEsW7wpKNCjG9DtNlClVuFLEZdDNbEs=
|
||||
golang.org/x/sys v0.0.0-20200523222454-059865788121 h1:rITEj+UZHYC927n8GT97eC3zrpzXdb/voyeOuVKS46o=
|
||||
golang.org/x/sys v0.0.0-20200523222454-059865788121/go.mod h1:h1NjWce9XRLGQEsW7wpKNCjG9DtNlClVuFLEZdDNbEs=
|
||||
golang.org/x/text v0.3.0/go.mod h1:NqM8EUOU14njkJ3fqMW+pc6Ldnwhi/IjpwHt7yyuwOQ=
|
||||
golang.org/x/text v0.3.3/go.mod h1:5Zoc/QRtKVWzQhOtBMvqHzDpF6irO9z98xDceosuGiQ=
|
||||
golang.org/x/tools v0.0.0-20180917221912-90fa682c2a6e/go.mod h1:n7NCudcB/nEzxVGmLbDWY5pfWTLqBcC2KZ6jyYvM4mQ=
|
||||
golang.org/x/tools v0.0.0-20190114222345-bf090417da8b/go.mod h1:n7NCudcB/nEzxVGmLbDWY5pfWTLqBcC2KZ6jyYvM4mQ=
|
||||
golang.org/x/tools v0.0.0-20190226205152-f727befe758c/go.mod h1:9Yl7xja0Znq3iFh3HoIrodX9oNMXvdceNzlUR8zjMvY=
|
||||
golang.org/x/tools v0.0.0-20190311212946-11955173bddd/go.mod h1:LCzVGOaR6xXOjkQ3onu1FJEFr0SW1gC7cKk1uF8kGRs=
|
||||
golang.org/x/tools v0.0.0-20190524140312-2c0ae7006135/go.mod h1:RgjU9mgBXZiqYHBnxXauZ1Gv1EHHAz9KjViQ78xBX0Q=
|
||||
golang.org/x/tools v0.0.0-20191119224855-298f0cb1881e/go.mod h1:b+2E5dAYhXwXZwtnZ6UAqBI28+e2cm9otk0dWdXHAEo=
|
||||
golang.org/x/tools v0.0.0-20200425043458-8463f397d07c h1:iHhCR0b26amDCiiO+kBguKZom9aMF+NrFxh9zeKR/XU=
|
||||
golang.org/x/tools v0.0.0-20200425043458-8463f397d07c/go.mod h1:EkVYQZoAsY45+roYkvgYkIh4xh/qjgUK9TdY2XT94GE=
|
||||
golang.org/x/xerrors v0.0.0-20190717185122-a985d3407aa7/go.mod h1:I/5z698sn9Ka8TeJc9MKroUUfqBBauWjQqLJ2OPfmY0=
|
||||
golang.org/x/xerrors v0.0.0-20191011141410-1b5146add898/go.mod h1:I/5z698sn9Ka8TeJc9MKroUUfqBBauWjQqLJ2OPfmY0=
|
||||
golang.org/x/xerrors v0.0.0-20191204190536-9bdfabe68543 h1:E7g+9GITq07hpfrRu66IVDexMakfv52eLZ2CXBWiKr4=
|
||||
golang.org/x/xerrors v0.0.0-20191204190536-9bdfabe68543/go.mod h1:I/5z698sn9Ka8TeJc9MKroUUfqBBauWjQqLJ2OPfmY0=
|
||||
google.golang.org/appengine v1.1.0/go.mod h1:EbEs0AVv82hx2wNQdGPgUI5lhzA/G0D9YwlJXL52JkM=
|
||||
google.golang.org/appengine v1.4.0/go.mod h1:xpcJRLb0r/rnEns0DIKYYv+WjYCduHsrkT7/EB5XEv4=
|
||||
google.golang.org/genproto v0.0.0-20180817151627-c66870c02cf8/go.mod h1:JiN7NxoALGmiZfu7CAH4rXhgtRTLTxftemlI0sWmxmc=
|
||||
google.golang.org/genproto v0.0.0-20190819201941-24fa4b261c55/go.mod h1:DMBHOl98Agz4BDEuKkezgsaosCRResVns1a3J2ZsMNc=
|
||||
google.golang.org/grpc v1.19.0/go.mod h1:mqu4LbDTu4XGKhr4mRzUsmM4RtVoemTSY81AxZiDr8c=
|
||||
google.golang.org/grpc v1.23.0/go.mod h1:Y5yQAOtifL1yxbo5wqy6BxZv8vAUGQwXBOALyacEbxg=
|
||||
google.golang.org/grpc v1.25.1/go.mod h1:c3i+UQWmh7LiEpx4sFZnkU36qjEYZ0imhYfXVyQciAY=
|
||||
google.golang.org/grpc v1.31.0/go.mod h1:N36X2cJ7JwdamYAgDz+s+rVMFjt3numwzf/HckM8pak=
|
||||
google.golang.org/protobuf v0.0.0-20200109180630-ec00e32a8dfd/go.mod h1:DFci5gLYBciE7Vtevhsrf46CRTquxDuWsQurQQe4oz8=
|
||||
google.golang.org/protobuf v0.0.0-20200221191635-4d8936d0db64/go.mod h1:kwYJMbMJ01Woi6D6+Kah6886xMZcty6N08ah7+eCXa0=
|
||||
google.golang.org/protobuf v0.0.0-20200228230310-ab0ca4ff8a60/go.mod h1:cfTl7dwQJ+fmap5saPgwCLgHXTUD7jkjRqWcaiX5VyM=
|
||||
google.golang.org/protobuf v1.20.1-0.20200309200217-e05f789c0967/go.mod h1:A+miEFZTKqfCUM6K7xSMQL9OKL/b6hQv+e19PK+JZNE=
|
||||
google.golang.org/protobuf v1.21.0/go.mod h1:47Nbq4nVaFHyn7ilMalzfO3qCViNmqZ2kzikPIcrTAo=
|
||||
google.golang.org/protobuf v1.23.0/go.mod h1:EGpADcykh3NcUnDUJcl1+ZksZNG86OlYog2l/sGQquU=
|
||||
gopkg.in/check.v1 v0.0.0-20161208181325-20d25e280405 h1:yhCVgyC4o1eVCa2tZl7eS0r+SDo693bJlVdllGtEeKM=
|
||||
gopkg.in/check.v1 v0.0.0-20161208181325-20d25e280405/go.mod h1:Co6ibVJAznAaIkqp8huTwlJQCZ016jof/cbN4VW5Yz0=
|
||||
gopkg.in/hlandau/easymetric.v1 v1.0.0 h1:ZbfbH7W3giuVDjWUoFhDOjjv20hiPr5HZ2yMV5f9IeE=
|
||||
gopkg.in/hlandau/easymetric.v1 v1.0.0/go.mod h1:yh75hypuFzAxmvECh3ZKGCvFnIfapYJh2wv7ASaX2RE=
|
||||
gopkg.in/hlandau/measurable.v1 v1.0.1 h1:wH5UZKCRUnRr1iD+xIZfwhtxhmr+bprRJttqA1Rklf4=
|
||||
gopkg.in/hlandau/measurable.v1 v1.0.1/go.mod h1:6N+SYJGMTmetsx7wskULP+juuO+++tsHJkAgzvzsbuM=
|
||||
gopkg.in/hlandau/passlib.v1 v1.0.11 h1:vKeHwGRdWBD9mm4bJ56GAAdBXpFUYvg/BYYkmphjnmA=
|
||||
gopkg.in/hlandau/passlib.v1 v1.0.11/go.mod h1:wxGAv2CtQHlzWY8NJp+p045yl4WHyX7v2T6XbOcmqjM=
|
||||
gopkg.in/hlandau/passlib.v1 v1.0.10 h1:q5xh9ZHp907XTjVw8/EqG03//fnlITnIYQmv4Gn7TpE=
|
||||
gopkg.in/hlandau/passlib.v1 v1.0.10/go.mod h1:wxGAv2CtQHlzWY8NJp+p045yl4WHyX7v2T6XbOcmqjM=
|
||||
gopkg.in/yaml.v2 v2.2.2 h1:ZCJp+EgiOT7lHqUV2J862kp8Qj64Jo6az82+3Td9dZw=
|
||||
gopkg.in/yaml.v2 v2.2.2/go.mod h1:hI93XBmqTisBFMUTm0b8Fm+jr3Dg1NNxqwp+5A1VGuI=
|
||||
gopkg.in/yaml.v3 v3.0.1 h1:fxVm/GzAzEWqLHuvctI91KS9hhNmmWOoWu0XTYJS7CA=
|
||||
gopkg.in/yaml.v3 v3.0.1/go.mod h1:K4uyk7z7BCEPqu6E+C64Yfv1cQ7kz7rIZviUmN+EgEM=
|
||||
honnef.co/go/tools v0.0.0-20190102054323-c2f93a96b099/go.mod h1:rf3lG4BRIbNafJWhAfAdb/ePZxsR/4RtNHQocxwk9r4=
|
||||
honnef.co/go/tools v0.0.0-20190523083050-ea95bdfd59fc/go.mod h1:rf3lG4BRIbNafJWhAfAdb/ePZxsR/4RtNHQocxwk9r4=
|
||||
rsc.io/pdf v0.1.1/go.mod h1:n8OzWcQ6Sp37PL01nO98y4iUCRdTGarVfzxY20ICaU4=
|
||||
|
|
|
|||
|
|
@ -2,14 +2,8 @@
|
|||
|
||||
EXE = $(notdir $(shell pwd))
|
||||
|
||||
ifeq ($(GARBLE),y)
|
||||
GO=garble -literals -tiny -debugdir=garbled
|
||||
else
|
||||
GO = go
|
||||
endif
|
||||
|
||||
all:
|
||||
$(GO) build .
|
||||
go build .
|
||||
|
||||
clean:
|
||||
$(RM) $(EXE) $(EXE).exe
|
||||
|
|
|
|||
|
|
@ -2,7 +2,7 @@ package xs
|
|||
|
||||
// Package xs - a secure terminal client/server written from scratch in Go
|
||||
//
|
||||
// Copyright (c) 2017-2025 Russell Magee
|
||||
// Copyright (c) 2017-2020 Russell Magee
|
||||
// Licensed under the terms of the MIT license (see LICENSE.mit in this
|
||||
// distribution)
|
||||
//
|
||||
|
|
|
|||
|
|
@ -0,0 +1,17 @@
|
|||
.PHONY: info clean lib
|
||||
|
||||
all: lib
|
||||
|
||||
clean:
|
||||
go clean .
|
||||
|
||||
lib: info
|
||||
go install .
|
||||
|
||||
ifneq ($(MSYSTEM),)
|
||||
info:
|
||||
@echo "Building for Windows (MSYS)"
|
||||
else
|
||||
info:
|
||||
@echo "Building for Linux"
|
||||
endif
|
||||
|
|
@ -0,0 +1,55 @@
|
|||
// A golang translation of a 'Shakespeare insult generator'
|
||||
// Originally from http://www.mainstrike.com/mstservices/handy/insult.html
|
||||
package spinsult
|
||||
|
||||
import (
|
||||
"math/rand"
|
||||
"time"
|
||||
)
|
||||
|
||||
var (
|
||||
r *rand.Rand
|
||||
|
||||
phrase1 = [...]string{
|
||||
"artless", "bawdy", "beslubbering", "bootless", "churlish", "clouted",
|
||||
"cockered", "craven", "currish", "dankish", "dissembling", "droning", "errant", "fawning",
|
||||
"fobbing", "frothy", "froward", "gleeking", "goatish", "gorbellied", "impertinent",
|
||||
"infectious", "jarring", "loggerheaded", "lumpish", "mammering", "mangled", "mewling",
|
||||
"paunchy", "pribbling", "puking", "puny", "qualling", "rank", "reeky", "roguish", "ruttish",
|
||||
"saucy", "spleeny", "spongy", "surly", "tottering", "unmuzzled", "vain", "venomed",
|
||||
"villainous", "warped", "wayward", "weedy", "yeasty"}
|
||||
|
||||
phrase2 = [...]string{"base-court", "bat-fowling", "beef-witted", "beetle-headed",
|
||||
"boil-brained", "clapper-clawed", "clay-brained", "common-kissing", "crook-pated",
|
||||
"dismal-dreaming", "dizzy-eyed", "doghearted", "dread-bolted", "earth-vexing",
|
||||
"elf-skinned", "fat-kidneyed", "fen-sucked", "flap-mouthed", "fly-bitten",
|
||||
"folly-fallen", "fool-born", "full-gorged", "guts-griping", "half-faced", "hasty-witted",
|
||||
"hedge-born", "hell-hated", "idle-headed", "ill-breeding", "ill-nurtured", "knotty-pated",
|
||||
"milk-livered", "motley-minded", "onion-eyed", "plume-plucked", "pottle-deep",
|
||||
"pox-marked", "reeling-ripe", "rough-hewn", "rude-growing", "rump-fed", "shard-borne",
|
||||
"sheep-biting", "spur-galled", "swag-bellied", "tardy-gaited", "tickle-brained",
|
||||
"toad-spotted", "urchin-snouted", "weather-bitten"}
|
||||
|
||||
phrase3 = [...]string{"apple-john", "baggage", "barnacle", "bladder", "boar-pig", "bugbear",
|
||||
"bum-bailey", "canker-blossom", "clack-dish", "clotpole", "codpiece", "coxcomb", "death-token",
|
||||
"dewberry", "flap-dragon", "flax-wench", "flirt-gill", "foot-licker", "fustilarian",
|
||||
"giglet", "gudgeon", "haggard", "harpy", "hedge-pig", "horn-beast", "hugger-mugger",
|
||||
"joithead", "lewdster", "lout", "maggot-pie", "malt-worm", "mammet", "measle", "minnow",
|
||||
"miscreant", "moldwarp", "mumble-news", "nut-hook", "pigeon-egg", "pignut", "pumpion",
|
||||
"puttock", "ratsbane", "scut", "skainsmate", "strumpet", "varlet", "vassal", "wagtail",
|
||||
"whey-face"}
|
||||
)
|
||||
|
||||
func GetSentence() (ret string) {
|
||||
return "Thou " + Get()
|
||||
}
|
||||
|
||||
func Get() (ret string) {
|
||||
if r == nil {
|
||||
r = rand.New(rand.NewSource(time.Now().UnixNano()))
|
||||
}
|
||||
ret = phrase1[r.Int()%len(phrase1)] + " " +
|
||||
phrase2[r.Int()%len(phrase2)] + " " +
|
||||
phrase3[r.Int()%len(phrase3)] + "!"
|
||||
return
|
||||
}
|
||||
|
|
@ -0,0 +1,52 @@
|
|||
//To show coverage for tests:
|
||||
//
|
||||
//1. go test -coverprofile=cov.out
|
||||
//2. go tool cover -func=cov.out
|
||||
//3. go tool cover -html=cov.out
|
||||
//4. Profit!!
|
||||
//
|
||||
// For heatmap coverage, change step 1 to:
|
||||
//2. go test -covermode=count -coverprofile=cov.out
|
||||
//
|
||||
// ref: https://blog.golang.org/cover
|
||||
|
||||
package spinsult
|
||||
|
||||
import (
|
||||
"fmt"
|
||||
"math/rand"
|
||||
"testing"
|
||||
)
|
||||
|
||||
func Test1Get(t *testing.T) {
|
||||
//if testing.Short() {
|
||||
// t.Skip("skipping test in short mode.")
|
||||
//}
|
||||
r = rand.New(rand.NewSource(42))
|
||||
out := Get()
|
||||
if out != "mammering doghearted codpiece!" {
|
||||
t.Fail()
|
||||
}
|
||||
}
|
||||
|
||||
func Test2Get(t *testing.T) {
|
||||
//if testing.Short() {
|
||||
// t.Skip("skipping test in short mode.")
|
||||
//}
|
||||
out := Get()
|
||||
if out != "dankish common-kissing coxcomb!" {
|
||||
t.Fail()
|
||||
}
|
||||
out = GetSentence()
|
||||
if out != "Thou wayward crook-pated fustilarian!" {
|
||||
t.Fail()
|
||||
}
|
||||
}
|
||||
|
||||
// Example of calling Get() for a random insult.
|
||||
func ExampleGet() {
|
||||
r = rand.New(rand.NewSource(42))
|
||||
out := GetSentence()
|
||||
fmt.Println(out)
|
||||
//Output: Thou mammering doghearted codpiece!
|
||||
}
|
||||
|
|
@ -5,7 +5,6 @@ package xs
|
|||
import (
|
||||
"errors"
|
||||
"io"
|
||||
"os"
|
||||
|
||||
unix "golang.org/x/sys/unix"
|
||||
)
|
||||
|
|
@ -31,8 +30,7 @@ type State struct {
|
|||
// MakeRaw put the terminal connected to the given file descriptor into raw
|
||||
// mode and returns the previous state of the terminal so that it can be
|
||||
// restored.
|
||||
func MakeRaw(f *os.File) (*State, error) {
|
||||
fd := f.Fd()
|
||||
func MakeRaw(fd uintptr) (*State, error) {
|
||||
termios, err := unix.IoctlGetTermios(int(fd), ioctlReadTermios)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
|
|
@ -58,8 +56,8 @@ func MakeRaw(f *os.File) (*State, error) {
|
|||
|
||||
// GetState returns the current state of a terminal which may be useful to
|
||||
// restore the terminal after a signal.
|
||||
func GetState(f *os.File) (*State, error) {
|
||||
termios, err := unix.IoctlGetTermios(int(f.Fd()), ioctlReadTermios)
|
||||
func GetState(fd uintptr) (*State, error) {
|
||||
termios, err := unix.IoctlGetTermios(int(fd), ioctlReadTermios)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
|
|
@ -69,9 +67,9 @@ func GetState(f *os.File) (*State, error) {
|
|||
|
||||
// Restore restores the terminal connected to the given file descriptor to a
|
||||
// previous state.
|
||||
func Restore(f *os.File, state *State) error {
|
||||
func Restore(fd uintptr, state *State) error {
|
||||
if state != nil {
|
||||
return unix.IoctlSetTermios(int(f.Fd()), ioctlWriteTermios, &state.termios)
|
||||
return unix.IoctlSetTermios(int(fd), ioctlWriteTermios, &state.termios)
|
||||
} else {
|
||||
return errors.New("nil State")
|
||||
}
|
||||
|
|
@ -80,8 +78,7 @@ func Restore(f *os.File, state *State) error {
|
|||
// ReadPassword reads a line of input from a terminal without local echo. This
|
||||
// is commonly used for inputting passwords and other sensitive data. The slice
|
||||
// returned does not include the \n.
|
||||
func ReadPassword(f *os.File) ([]byte, error) {
|
||||
fd := f.Fd()
|
||||
func ReadPassword(fd uintptr) ([]byte, error) {
|
||||
termios, err := unix.IoctlGetTermios(int(fd), ioctlReadTermios)
|
||||
if err != nil {
|
||||
return nil, err
|
||||
|
|
|
|||
|
|
@ -1,4 +1,3 @@
|
|||
//go:build windows
|
||||
// +build windows
|
||||
|
||||
// Note the terminal manipulation functions herein are mostly stubs. They
|
||||
|
|
@ -16,12 +15,10 @@
|
|||
package xs
|
||||
|
||||
import (
|
||||
"bufio"
|
||||
"fmt"
|
||||
"log"
|
||||
"os"
|
||||
"io"
|
||||
"os/exec"
|
||||
"os/signal"
|
||||
|
||||
"golang.org/x/sys/windows"
|
||||
)
|
||||
|
||||
type State struct {
|
||||
|
|
@ -30,84 +27,67 @@ type State struct {
|
|||
// MakeRaw put the terminal connected to the given file descriptor into raw
|
||||
// mode and returns the previous state of the terminal so that it can be
|
||||
// restored.
|
||||
func MakeRaw(f *os.File) (*State, error) {
|
||||
cmd := exec.Command("stty", "-echo", "raw")
|
||||
cmd.Stdin = f
|
||||
err := cmd.Run()
|
||||
if err != nil {
|
||||
log.Fatal(err)
|
||||
return &State{}, err
|
||||
}
|
||||
|
||||
// MSYS2/CYGWIN: wintty needs CTRL-C caught
|
||||
// ----------------------------------------
|
||||
c := make(chan os.Signal, 1)
|
||||
signal.Notify(c, os.Interrupt, os.Kill)
|
||||
go func() {
|
||||
for sig := range c {
|
||||
_ = sig
|
||||
//fmt.Println(sig)
|
||||
}
|
||||
}()
|
||||
// ----------------------------------------
|
||||
|
||||
func MakeRaw(fd uintptr) (*State, error) {
|
||||
// This doesn't really work. The exec.Command() runs a sub-shell
|
||||
// so the stty mods don't affect the client process.
|
||||
cmd := exec.Command("stty", "-echo raw")
|
||||
cmd.Run()
|
||||
return &State{}, nil
|
||||
}
|
||||
|
||||
// GetState returns the current state of a terminal which may be useful to
|
||||
// restore the terminal after a signal.
|
||||
func GetState(f *os.File) (*State, error) {
|
||||
func GetState(fd uintptr) (*State, error) {
|
||||
return &State{}, nil
|
||||
}
|
||||
|
||||
// Restore restores the terminal connected to the given file descriptor to a
|
||||
// previous state.
|
||||
func Restore(f *os.File, state *State) error {
|
||||
cmd := exec.Command("stty", "sane")
|
||||
cmd.Stdin = f
|
||||
err := cmd.Run()
|
||||
if err != nil {
|
||||
log.Fatal(err)
|
||||
return nil
|
||||
}
|
||||
func Restore(fd uintptr, state *State) error {
|
||||
cmd := exec.Command("stty", "echo cooked")
|
||||
cmd.Run()
|
||||
return nil
|
||||
}
|
||||
|
||||
// ReadPassword reads a line of input from a terminal without local echo. This
|
||||
// is commonly used for inputting passwords and other sensitive data. The slice
|
||||
// returned does not include the \n.
|
||||
func ReadPassword(f *os.File) (pw []byte, err error) {
|
||||
sttycmd, err := exec.LookPath("stty")
|
||||
if err != nil {
|
||||
return nil, err
|
||||
} else {
|
||||
//fmt.Printf("stty found at: %v\n", sttycmd)
|
||||
cmdOff := exec.Command(sttycmd, "-echo")
|
||||
cmdOff.Stdin = f //os.Stdin
|
||||
cmdOff.Stdout = nil //os.Stdout
|
||||
cmdOff.Stderr = nil //os.Stderr
|
||||
err = cmdOff.Run()
|
||||
if err != nil {
|
||||
return nil, err
|
||||
}
|
||||
func ReadPassword(fd uintptr) ([]byte, error) {
|
||||
return readPasswordLine(passwordReader(fd))
|
||||
}
|
||||
|
||||
//fmt.Printf("Enter password:")
|
||||
scanner := bufio.NewScanner(os.Stdin)
|
||||
scanner.Scan()
|
||||
err = scanner.Err()
|
||||
if err != nil {
|
||||
return nil, err
|
||||
// passwordReader is an io.Reader that reads from a specific file descriptor.
|
||||
type passwordReader windows.Handle
|
||||
|
||||
func (r passwordReader) Read(buf []byte) (int, error) {
|
||||
return windows.Read(windows.Handle(r), buf)
|
||||
}
|
||||
|
||||
// readPasswordLine reads from reader until it finds \n or io.EOF.
|
||||
// The slice returned does not include the \n.
|
||||
// readPasswordLine also ignores any \r it finds.
|
||||
func readPasswordLine(reader io.Reader) ([]byte, error) {
|
||||
var buf [1]byte
|
||||
var ret []byte
|
||||
|
||||
for {
|
||||
n, err := reader.Read(buf[:])
|
||||
if n > 0 {
|
||||
switch buf[0] {
|
||||
case '\n':
|
||||
return ret, nil
|
||||
case '\r':
|
||||
// remove \r from passwords on Windows
|
||||
default:
|
||||
ret = append(ret, buf[0])
|
||||
}
|
||||
continue
|
||||
}
|
||||
pw = scanner.Bytes()
|
||||
fmt.Println()
|
||||
cmdOn := exec.Command(sttycmd, "echo")
|
||||
cmdOn.Stdin = f //os.Stdin
|
||||
cmdOn.Stdout = nil //os.Stdout
|
||||
cmdOn.Stderr = nil //os.Stderr
|
||||
err = cmdOn.Run()
|
||||
if err != nil {
|
||||
return nil, err
|
||||
if err == io.EOF && len(ret) > 0 {
|
||||
return ret, nil
|
||||
}
|
||||
return ret, err
|
||||
}
|
||||
}
|
||||
return
|
||||
}
|
||||
|
|
|
|||
|
|
@ -1,14 +0,0 @@
|
|||
#!/bin/bash
|
||||
|
||||
## setup.sh - create some files for xc copy testing
|
||||
dir=cptest
|
||||
|
||||
mkdir -p ${dir}/subdir
|
||||
dd bs=1024 count=16 if=/dev/urandom of=${dir}/file16KB
|
||||
dd bs=1024 count=16 if=/dev/urandom of=${dir}/file1KB
|
||||
dd bs=1024 count=16 if=/dev/urandom of=${dir}/file32KB
|
||||
dd bs=1024 count=16 if=/dev/urandom of=${dir}/file6B
|
||||
dd bs=1048576 count=32 if=/dev/urandom of=${dir}/subdir/file32MB
|
||||
dd bs=1048576 count=64 if=/dev/urandom of=${dir}/subdir/file64MB
|
||||
|
||||
sha1sum $(find ${dir} -type f | sort) >${dir}.sha1sum
|
||||
|
|
@ -1,17 +1,11 @@
|
|||
.PHONY: clean all vis lint
|
||||
|
||||
ifeq ($(GARBLE),y)
|
||||
GO = garble -literals -tiny -debugdir=garbled
|
||||
else
|
||||
GO = go
|
||||
endif
|
||||
|
||||
EXTPKGS = bytes,errors,flag,fmt,internal,io,log,net,os,path,runtime,time,strings,sync,syscall,binary,encoding
|
||||
EXE = $(notdir $(shell pwd))
|
||||
|
||||
all:
|
||||
echo "BUILDOPTS:" $(BUILDOPTS)
|
||||
$(GO) build $(BUILDOPTS) .
|
||||
go build $(BUILDOPTS) .
|
||||
|
||||
clean:
|
||||
$(RM) $(EXE) $(EXE).exe
|
||||
|
|
|
|||
|
|
@ -0,0 +1,39 @@
|
|||
#!/bin/bash
|
||||
#
|
||||
## This wrapper may be used within the MSYS/mintty Windows
|
||||
## shell environment to have a functioning hkexsh client with
|
||||
## working 'raw' mode and hidden password entry.
|
||||
##
|
||||
## mintty uses named pipes and ptys to get a more POSIX-like
|
||||
## terminal (incl. VT/ANSI codes) rather than the dumb Windows
|
||||
## console interface; however Go on Windows does not have functioning
|
||||
## MSYS/mintty code to set raw, echo etc. modes.
|
||||
##
|
||||
## Someday it would be preferable to put native Windows term mode
|
||||
## code into the client build, but this is 'good enough' for now
|
||||
## (with the exception of tty rows/cols not being set based on
|
||||
## info from the server).
|
||||
##
|
||||
## INSTALLATION
|
||||
## --
|
||||
## Build the client, put it somewhere in your $PATH with this
|
||||
## wrapper and edit the name of the client binary
|
||||
## eg.,
|
||||
## $ cp hkexsh.exe /usr/bin/.hkexsh.exe
|
||||
## $ cp mintty_wrapper.sh /usr/bin/hkexsh
|
||||
####
|
||||
trap cleanup EXIT ERR
|
||||
|
||||
cleanup() {
|
||||
stty sane
|
||||
}
|
||||
|
||||
me="$(basename "$(test -L "$0" && readlink "$0" || echo "$0")")"
|
||||
|
||||
if [ ${1}x == "-hx" ]; then
|
||||
_${me} -h
|
||||
else
|
||||
stty -echo raw icrnl
|
||||
_${me} $@
|
||||
fi
|
||||
|
||||
|
|
@ -1,4 +1,3 @@
|
|||
//go:build linux || freebsd
|
||||
// +build linux freebsd
|
||||
|
||||
package main
|
||||
|
|
@ -31,7 +30,7 @@ func handleTermResizes(conn *xsnet.Conn) {
|
|||
log.Println(err)
|
||||
}
|
||||
termSzPacket := fmt.Sprintf("%d %d", rows, cols)
|
||||
conn.WritePacket([]byte(termSzPacket), xsnet.CSOTermSize) //nolint:errcheck
|
||||
conn.WritePacket([]byte(termSzPacket), xsnet.CSOTermSize) // nolint: errcheck,gosec
|
||||
}
|
||||
}()
|
||||
ch <- syscall.SIGWINCH // Initial resize.
|
||||
|
|
|
|||
Binary file not shown.
|
Before Width: | Height: | Size: 1.2 MiB After Width: | Height: | Size: 1.1 MiB |
643
xs/xs-vis.gv
643
xs/xs-vis.gv
|
|
@ -10,7 +10,7 @@ digraph gocallvis {
|
|||
pad="0.0";
|
||||
nodesep="0.35";
|
||||
|
||||
node [shape="box" style="filled,rounded" fillcolor="honeydew" fontname="Verdana" penwidth="1.0" margin="0.05,0.0"];
|
||||
node [shape="ellipse" style="filled" fillcolor="honeydew" fontname="Verdana" penwidth="1.0" margin="0.05,0.0"];
|
||||
edge [minlen="2"]
|
||||
|
||||
subgraph "cluster_focus" {
|
||||
|
|
@ -20,135 +20,129 @@ labelloc="t";
|
|||
labeljust="c";
|
||||
fontsize="18";
|
||||
|
||||
"blitter.com/go/xs/xs.restoreTermState" [ fillcolor="lightblue" label="restoreTermState" penwidth="0.5" tooltip="blitter.com/go/xs/xs.restoreTermState | defined in xs.go:1117\nat xs.go:1118: calling [blitter.com/go/xs.Restore]" ]
|
||||
"blitter.com/go/xs/xs.main$2" [ fillcolor="lightblue" label="deferCloseChaff" style="dotted,filled" tooltip="blitter.com/go/xs/xs.main$2 | defined in xs.go:996\nat xs.go:999: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:997: calling [blitter.com/go/xs/xs.restoreTermState]" ]
|
||||
"blitter.com/go/xs/xs.exitWithStatus" [ penwidth="0.5" tooltip="blitter.com/go/xs/xs.exitWithStatus | defined in xs.go:1122" fillcolor="lightblue" label="exitWithStatus" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" [ fillcolor="lightblue" label="doCopyMode" penwidth="0.5" tooltip="blitter.com/go/xs/xs.doCopyMode | defined in xs.go:354\nat xs.go:435: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:438: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:473: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:475: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:430: calling [(*blitter.com/go/xs/xsnet.Conn).SetStatus]\nat xs.go:444: calling [blitter.com/go/xs/xs.buildCmdRemoteToLocal]\nat xs.go:424: calling [(blitter.com/go/xs/xsnet.Conn).Read]\nat xs.go:356: calling [(blitter.com/go/xs.Session).Cmd]\nat xs.go:441: calling [(blitter.com/go/xs.Session).Cmd]\nat xs.go:417: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]\nat xs.go:364: calling [blitter.com/go/xs/xs.buildCmdLocalToRemote]" ]
|
||||
"blitter.com/go/xs/xs.buildCmdLocalToRemote" [ tooltip="blitter.com/go/xs/xs.buildCmdLocalToRemote | defined in xs.go:270\nat xs.go:283: calling [blitter.com/go/xs.GetTool]\nat xs.go:311: calling [blitter.com/go/xs.GetTool]\nat xs.go:312: calling [blitter.com/go/xs.GetTool]\nat xs.go:335: calling [blitter.com/go/xs/xs.getTreeSizeSubCmd]" fillcolor="lightblue" label="buildCmdLocalToRemote" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.getTreeSizeSubCmd" [ fillcolor="lightblue" label="getTreeSizeSubCmd" penwidth="0.5" tooltip="blitter.com/go/xs/xs.getTreeSizeSubCmd | defined in xs.go:342" ]
|
||||
"blitter.com/go/xs/xs.buildCmdRemoteToLocal" [ fillcolor="lightblue" label="buildCmdRemoteToLocal" penwidth="0.5" tooltip="blitter.com/go/xs/xs.buildCmdRemoteToLocal | defined in xs.go:244\nat xs.go:256: calling [blitter.com/go/xs.GetTool]\nat xs.go:263: calling [blitter.com/go/xs.GetTool]" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" [ fillcolor="lightblue" label="copyBuffer" penwidth="0.5" tooltip="blitter.com/go/xs/xs.copyBuffer | defined in xs.go:128\nat xs.go:186: calling [blitter.com/go/xs/xs.copyBuffer$2]\nat xs.go:186: calling [blitter.com/go/xs/xs.copyBuffer$3]\nat xs.go:193: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:186: calling [blitter.com/go/xs/xs.copyBuffer$1]" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer$1" [ fillcolor="lightblue" label="copyBuffer$1" style="dotted,filled" tooltip="blitter.com/go/xs/xs.copyBuffer$1 | defined in xs.go:144" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer$2" [ fillcolor="lightblue" label="copyBuffer$2" style="dotted,filled" tooltip="blitter.com/go/xs/xs.copyBuffer$2 | defined in xs.go:145" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer$3" [ fillcolor="lightblue" label="copyBuffer$3" style="dotted,filled" tooltip="blitter.com/go/xs/xs.copyBuffer$3 | defined in xs.go:146" ]
|
||||
"blitter.com/go/xs/xs.reqTunnel" [ tooltip="blitter.com/go/xs/xs.reqTunnel | defined in xs.go:584\nat xs.go:594: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]\nat xs.go:593: calling [blitter.com/go/xs/logger.LogDebug]" fillcolor="lightblue" label="reqTunnel" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.main" [ fillcolor="lightblue" label="main" penwidth="0.5" tooltip="blitter.com/go/xs/xs.main | defined in xs.go:680\nat xs.go:1056: calling [(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff]\nat xs.go:1027: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:1089: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:1091: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:1101: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:864: calling [blitter.com/go/xs/logger.New]\nat xs.go:978: calling [blitter.com/go/xs.MakeRaw]\nat xs.go:1075: calling [blitter.com/go/xs/xs.main$3]\nat xs.go:1039: calling [(blitter.com/go/xs/xsnet.Conn).Read]\nat xs.go:960: calling [blitter.com/go/xs/xsnet.Dial]\nat xs.go:1081: calling [blitter.com/go/xs/xs.launchTuns]\nat xs.go:977: calling [github.com/mattn/go-isatty.IsTerminal]\nat xs.go:772: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:853: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:963: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:1027: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:1101: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:1082: calling [blitter.com/go/xs/xs.doShellMode]\nat xs.go:1050: calling [(*blitter.com/go/xs/xsnet.Conn).SetupChaff]\nat xs.go:1022: calling [blitter.com/go/xs/xs.sendSessionParams]\nat xs.go:796: calling [blitter.com/go/xs/xs.parseNonSwitchArgs]\nat xs.go:1024: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:1090: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:1096: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:1055: calling [(*blitter.com/go/xs/xsnet.Conn).DisableChaff]\nat xs.go:1025: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:1043: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:1047: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:1086: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:852: calling [blitter.com/go/xs/xs.usageShell]\nat xs.go:984: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:1005: calling [blitter.com/go/xs.ReadPassword]\nat xs.go:1054: calling [(*blitter.com/go/xs/xsnet.Conn).EnableChaff]\nat xs.go:1085: calling [blitter.com/go/xs/xs.doCopyMode]\nat xs.go:972: calling [(*blitter.com/go/xs/xsnet.Conn).Close]\nat xs.go:1046: calling [blitter.com/go/xs/xs.rejectUserMsg]\nat xs.go:852: calling [blitter.com/go/xs/xs.usageCp]\nat xs.go:790: calling [blitter.com/go/xs/xs.main$1]\nat xs.go:803: calling [blitter.com/go/xs/xs.localUserName]\nat xs.go:865: calling [blitter.com/go/xs/xsnet.Init]\nat xs.go:1021: calling [blitter.com/go/xs.NewSession]" ]
|
||||
"blitter.com/go/xs/xs.parseNonSwitchArgs" [ label="parseNonSwitchArgs" penwidth="0.5" tooltip="blitter.com/go/xs/xs.parseNonSwitchArgs | defined in xs.go:599" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.main$1" [ fillcolor="lightblue" label="deferRestore" style="dotted,filled" tooltip="blitter.com/go/xs/xs.main$1 | defined in xs.go:790" ]
|
||||
"blitter.com/go/xs/xs.localUserName" [ fillcolor="lightblue" label="localUserName" penwidth="0.5" tooltip="blitter.com/go/xs/xs.localUserName | defined in xs.go:1106" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" [ fillcolor="lightblue" label="sendSessionParams" penwidth="0.5" tooltip="blitter.com/go/xs/xs.sendSessionParams | defined in xs.go:649\nat xs.go:651: calling [(blitter.com/go/xs.Session).Cmd]\nat xs.go:671: calling [(blitter.com/go/xs.Session).Cmd]\nat xs.go:651: calling [(blitter.com/go/xs.Session).AuthCookie]\nat xs.go:675: calling [(blitter.com/go/xs.Session).AuthCookie]\nat xs.go:651: calling [(blitter.com/go/xs.Session).Who]\nat xs.go:659: calling [(blitter.com/go/xs.Session).Who]\nat xs.go:651: calling [(blitter.com/go/xs.Session).Op]\nat xs.go:655: calling [(blitter.com/go/xs.Session).Op]\nat xs.go:651: calling [(blitter.com/go/xs.Session).TermType]\nat xs.go:667: calling [(blitter.com/go/xs.Session).TermType]\nat xs.go:651: calling [(blitter.com/go/xs.Session).ConnHost]\nat xs.go:663: calling [(blitter.com/go/xs.Session).ConnHost]\nat xs.go:675: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:671: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:667: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:663: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:659: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:655: calling [(blitter.com/go/xs/xsnet.Conn).Write]" ]
|
||||
"blitter.com/go/xs/xs.rejectUserMsg" [ fillcolor="lightblue" label="rejectUserMsg" penwidth="0.5" tooltip="blitter.com/go/xs/xs.rejectUserMsg | defined in xs.go:576\nat xs.go:577: calling [blitter.com/go/xs/spinsult.GetSentence]" ]
|
||||
"blitter.com/go/xs/xs.main$3" [ fillcolor="lightblue" label="main$3" style="dotted,filled" tooltip="blitter.com/go/xs/xs.main$3 | defined in xs.go:1065\nat xs.go:1068: calling [math/rand.Intn]\nat xs.go:1072: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]" ]
|
||||
"blitter.com/go/xs/xs.launchTuns" [ fillcolor="lightblue" label="launchTuns" penwidth="0.5" tooltip="blitter.com/go/xs/xs.launchTuns | defined in xs.go:634\nat xs.go:645: calling [blitter.com/go/xs/xs.reqTunnel]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" [ tooltip="blitter.com/go/xs/xs.doShellMode$1 | defined in xs.go:490\nat xs.go:509: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:519: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:507: calling [(crypto/x509.SystemRootsError).Error]\nat xs.go:513: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:507: calling [(crypto/x509.CertificateInvalidError).Error]\nat xs.go:507: calling [(vendor/golang.org/x/net/idna.labelError).Error]\nat xs.go:507: calling [(crypto/tls.RecordHeaderError).Error]\nat xs.go:507: calling [(crypto/x509.UnknownAuthorityError).Error]\nat xs.go:513: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:507: calling [(crypto/tls.alert).Error]\nat xs.go:507: calling [(context.deadlineExceededError).Error]\nat xs.go:507: calling [(crypto/aes.KeySizeError).Error]\nat xs.go:507: calling [(crypto/x509.UnhandledCriticalExtension).Error]\nat xs.go:507: calling [(compress/flate.CorruptInputError).Error]\nat xs.go:507: calling [(*github.com/pkg/errors.fundamental).Error]\nat xs.go:491: calling [blitter.com/go/xs/xs.doShellMode$1$1]\nat xs.go:507: calling [(crypto/x509.HostnameError).Error]\nat xs.go:507: calling [(*crypto/tls.permanentError).Error]\nat xs.go:507: calling [(vendor/golang.org/x/net/idna.runeError).Error]\nat xs.go:514: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:519: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:503: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:518: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:507: calling [(compress/flate.InternalError).Error]" fillcolor="lightblue" label="shellRemoteToStdin" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1$1" [ fillcolor="lightblue" label="doShellMode$1$1" style="dotted,filled" tooltip="blitter.com/go/xs/xs.doShellMode$1$1 | defined in xs.go:491" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" [ fillcolor="lightblue" label="doShellMode" penwidth="0.5" tooltip="blitter.com/go/xs/xs.doShellMode | defined in xs.go:483\nat xs.go:522: calling [blitter.com/go/xs/xs.doShellMode$1]\nat xs.go:551: calling [blitter.com/go/xs/xs.doShellMode$2]\nat xs.go:527: calling [blitter.com/go/xs/xs.handleTermResizes]" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes$1" [ tooltip="blitter.com/go/xs/xs.handleTermResizes$1 | defined in termsize_unix.go:21\nat termsize_unix.go:33: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]\nat termsize_unix.go:27: calling [blitter.com/go/xs/xs.GetSize]" fillcolor="lightblue" label="handleTermResizes$1" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.GetSize" [ penwidth="1.5" tooltip="blitter.com/go/xs/xs.GetSize | defined in xs.go:221" fillcolor="lightblue" label="GetSize" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes" [ fillcolor="lightblue" label="handleTermResizes" penwidth="0.5" tooltip="blitter.com/go/xs/xs.handleTermResizes | defined in termsize_unix.go:16\nat termsize_unix.go:21: calling [blitter.com/go/xs/xs.handleTermResizes$1]" ]
|
||||
"blitter.com/go/xs/xs.Copy" [ tooltip="blitter.com/go/xs/xs.Copy | defined in xs.go:115\nat xs.go:116: calling [blitter.com/go/xs/xs.copyBuffer]" fillcolor="lightblue" label="Copy" penwidth="1.5" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2$1" [ fillcolor="lightblue" label="doShellMode$2$1" style="dotted,filled" tooltip="blitter.com/go/xs/xs.doShellMode$2$1 | defined in xs.go:536\nat xs.go:539: calling [blitter.com/go/xs/xs.Copy]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" [ style="dotted,filled" tooltip="blitter.com/go/xs/xs.doShellMode$2 | defined in xs.go:534\nat xs.go:546: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:548: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:541: calling [blitter.com/go/xs/xs.doShellMode$2$1]" fillcolor="lightblue" label="shellStdinToRemote" ]
|
||||
"blitter.com/go/xs/xs.usageShell" [ fillcolor="lightblue" label="usageShell" penwidth="0.5" tooltip="blitter.com/go/xs/xs.usageShell | defined in xs.go:559" ]
|
||||
"blitter.com/go/xs/xs.usageCp" [ label="usageCp" penwidth="0.5" tooltip="blitter.com/go/xs/xs.usageCp | defined in xs.go:565" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.reqTunnel" [ fillcolor="lightblue" label="reqTunnel" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.launchTuns" [ label="launchTuns" penwidth="0.5" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.main$3" [ fillcolor="lightblue" label="main$3" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" [ fillcolor="lightblue" label="doCopyMode" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" [ fillcolor="lightblue" label="copyBuffer" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer$1" [ label="copyBuffer$1" style="dotted,filled" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer$2" [ label="copyBuffer$2" style="dotted,filled" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer$3" [ fillcolor="lightblue" label="copyBuffer$3" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.Copy" [ label="Copy" penwidth="1.5" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" [ fillcolor="lightblue" label="shellRemoteToStdin" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1$1" [ fillcolor="lightblue" label="doShellMode$1$1" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.exitWithStatus" [ fillcolor="lightblue" label="exitWithStatus" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" [ label="doShellMode" penwidth="0.5" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes$1" [ fillcolor="lightblue" label="handleTermResizes$1" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.GetSize" [ fillcolor="lightblue" label="GetSize" penwidth="1.5" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes" [ label="handleTermResizes" penwidth="0.5" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2$1" [ fillcolor="lightblue" label="doShellMode$2$1" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" [ fillcolor="lightblue" label="shellStdinToRemote" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" [ fillcolor="lightblue" label="sendSessionParams" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.main" [ label="main" penwidth="0.5" fillcolor="lightblue" ]
|
||||
"blitter.com/go/xs/xs.parseNonSwitchArgs" [ fillcolor="lightblue" label="parseNonSwitchArgs" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.main$1" [ fillcolor="lightblue" label="deferRestore" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.main$2" [ fillcolor="lightblue" label="deferCloseChaff" style="dotted,filled" ]
|
||||
"blitter.com/go/xs/xs.rejectUserMsg" [ fillcolor="lightblue" label="rejectUserMsg" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.usageShell" [ fillcolor="lightblue" label="usageShell" penwidth="0.5" ]
|
||||
"blitter.com/go/xs/xs.usageCp" [ label="usageCp" penwidth="0.5" fillcolor="lightblue" ]
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs" {
|
||||
style="filled";
|
||||
penwidth="0.8";
|
||||
style="filled";
|
||||
rank="sink";
|
||||
tooltip="package: blitter.com/go/xs";
|
||||
label="xs";
|
||||
URL="/?f=blitter.com/go/xs";
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
fillcolor="lightyellow";
|
||||
fontname="Tahoma bold";
|
||||
fontname="bold";
|
||||
label="[xs]";
|
||||
URL="/?f=blitter.com/go/xs";
|
||||
|
||||
"blitter.com/go/xs.Restore" [ tooltip="blitter.com/go/xs.Restore | defined in termmode_linux.go:70" fillcolor="moccasin" label="Restore" penwidth="1.5" ]
|
||||
"blitter.com/go/xs.GetTool" [ fillcolor="moccasin" label="GetTool" penwidth="1.5" tooltip="blitter.com/go/xs.GetTool | defined in auth.go:217" ]
|
||||
"blitter.com/go/xs.MakeRaw" [ fillcolor="moccasin" label="MakeRaw" penwidth="1.5" tooltip="blitter.com/go/xs.MakeRaw | defined in termmode_linux.go:33" ]
|
||||
"blitter.com/go/xs.ReadPassword" [ tooltip="blitter.com/go/xs.ReadPassword | defined in termmode_linux.go:81" fillcolor="moccasin" label="ReadPassword" penwidth="1.5" ]
|
||||
"blitter.com/go/xs.NewSession" [ fillcolor="moccasin" label="NewSession" penwidth="1.5" tooltip="blitter.com/go/xs.NewSession | defined in session.go:130" ]
|
||||
"blitter.com/go/xs.Restore" [ fillcolor="moccasin" label="Restore" penwidth="1.5" ]
|
||||
"blitter.com/go/xs.MakeRaw" [ penwidth="1.5" fillcolor="moccasin" label="MakeRaw" ]
|
||||
"blitter.com/go/xs.ReadPassword" [ fillcolor="moccasin" label="ReadPassword" penwidth="1.5" ]
|
||||
"blitter.com/go/xs.NewSession" [ fillcolor="moccasin" label="NewSession" penwidth="1.5" ]
|
||||
|
||||
subgraph "cluster_*blitter.com/go/xs.Session" {
|
||||
fillcolor="wheat2";
|
||||
label="(*Session)";
|
||||
tooltip="type: *blitter.com/go/xs.Session";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
|
||||
"(*blitter.com/go/xs.Session).SetStatus" [ fillcolor="moccasin" label="SetStatus" penwidth="1.5" tooltip="(*blitter.com/go/xs.Session).SetStatus | defined in session.go:125" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs.Session" {
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(*Session)";
|
||||
tooltip="type: *blitter.com/go/xs.Session";
|
||||
penwidth="0.5";
|
||||
|
||||
"(*blitter.com/go/xs.Session).SetStatus" [ fillcolor="moccasin" label="SetStatus" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs.Session" {
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(Session)";
|
||||
tooltip="type: blitter.com/go/xs.Session";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
|
||||
"(blitter.com/go/xs.Session).Cmd" [ fillcolor="moccasin" label="Cmd" penwidth="1.5" tooltip="(blitter.com/go/xs.Session).Cmd | defined in session.go:79" ]
|
||||
"(blitter.com/go/xs.Session).Op" [ fillcolor="moccasin" label="Op" penwidth="1.5" tooltip="(blitter.com/go/xs.Session).Op | defined in session.go:36" ]
|
||||
"(blitter.com/go/xs.Session).Who" [ fillcolor="moccasin" label="Who" penwidth="1.5" tooltip="(blitter.com/go/xs.Session).Who | defined in session.go:46" ]
|
||||
"(blitter.com/go/xs.Session).ConnHost" [ label="ConnHost" penwidth="1.5" tooltip="(blitter.com/go/xs.Session).ConnHost | defined in session.go:56" fillcolor="moccasin" ]
|
||||
"(blitter.com/go/xs.Session).TermType" [ fillcolor="moccasin" label="TermType" penwidth="1.5" tooltip="(blitter.com/go/xs.Session).TermType | defined in session.go:67" ]
|
||||
"(blitter.com/go/xs.Session).AuthCookie" [ fillcolor="moccasin" label="AuthCookie" penwidth="1.5" tooltip="(blitter.com/go/xs.Session).AuthCookie | defined in session.go:92" ]
|
||||
"(blitter.com/go/xs.Session).Status" [ penwidth="1.5" tooltip="(blitter.com/go/xs.Session).Status | defined in session.go:120" fillcolor="moccasin" label="Status" ]
|
||||
"(blitter.com/go/xs.Session).Cmd" [ fillcolor="moccasin" label="Cmd" penwidth="1.5" ]
|
||||
"(blitter.com/go/xs.Session).Status" [ penwidth="1.5" fillcolor="moccasin" label="Status" ]
|
||||
"(blitter.com/go/xs.Session).Op" [ fillcolor="moccasin" label="Op" penwidth="1.5" ]
|
||||
"(blitter.com/go/xs.Session).Who" [ fillcolor="moccasin" label="Who" penwidth="1.5" ]
|
||||
"(blitter.com/go/xs.Session).ConnHost" [ fillcolor="moccasin" label="ConnHost" penwidth="1.5" ]
|
||||
"(blitter.com/go/xs.Session).TermType" [ fillcolor="moccasin" label="TermType" penwidth="1.5" ]
|
||||
"(blitter.com/go/xs.Session).AuthCookie" [ label="AuthCookie" penwidth="1.5" fillcolor="moccasin" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs/logger" {
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
fontname="Tahoma bold";
|
||||
fontsize="16";
|
||||
URL="/?f=blitter.com/go/xs/logger";
|
||||
tooltip="package: blitter.com/go/xs/logger";
|
||||
penwidth="0.8";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
fontname="bold";
|
||||
rank="sink";
|
||||
label="logger";
|
||||
label="[logger]";
|
||||
tooltip="package: blitter.com/go/xs/logger";
|
||||
|
||||
"blitter.com/go/xs/logger.LogDebug" [ fillcolor="moccasin" label="LogDebug" penwidth="1.5" tooltip="blitter.com/go/xs/logger.LogDebug | defined in logger_linux.go:103" ]
|
||||
"blitter.com/go/xs/logger.New" [ fillcolor="moccasin" label="New" penwidth="1.5" tooltip="blitter.com/go/xs/logger.New | defined in logger_linux.go:71" ]
|
||||
"blitter.com/go/xs/logger.LogDebug" [ fillcolor="moccasin" label="LogDebug" penwidth="1.5" ]
|
||||
"blitter.com/go/xs/logger.New" [ fillcolor="moccasin" label="New" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs/spinsult" {
|
||||
penwidth="0.8";
|
||||
style="filled";
|
||||
fontname="Tahoma bold";
|
||||
rank="sink";
|
||||
fontsize="16";
|
||||
fillcolor="lightyellow";
|
||||
label="spinsult";
|
||||
fillcolor="lightyellow";
|
||||
fontname="bold";
|
||||
label="[spinsult]";
|
||||
URL="/?f=blitter.com/go/xs/spinsult";
|
||||
tooltip="package: blitter.com/go/xs/spinsult";
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
rank="sink";
|
||||
|
||||
"blitter.com/go/xs/spinsult.GetSentence" [ label="GetSentence" penwidth="1.5" tooltip="blitter.com/go/xs/spinsult.GetSentence | defined in spinsult.go:43" fillcolor="moccasin" ]
|
||||
"blitter.com/go/xs/spinsult.GetSentence" [ fillcolor="moccasin" label="GetSentence" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs/xsnet" {
|
||||
fontname="Tahoma bold";
|
||||
penwidth="0.8";
|
||||
fillcolor="lightyellow";
|
||||
fontname="bold";
|
||||
rank="sink";
|
||||
label="xsnet";
|
||||
tooltip="package: blitter.com/go/xs/xsnet";
|
||||
penwidth="0.8";
|
||||
URL="/?f=blitter.com/go/xs/xsnet";
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
URL="/?f=blitter.com/go/xs/xsnet";
|
||||
label="[xsnet]";
|
||||
tooltip="package: blitter.com/go/xs/xsnet";
|
||||
|
||||
"blitter.com/go/xs/xsnet.Init" [ fillcolor="moccasin" label="Init" penwidth="1.5" tooltip="blitter.com/go/xs/xsnet.Init | defined in net.go:198" ]
|
||||
"blitter.com/go/xs/xsnet.Dial" [ fillcolor="moccasin" label="Dial" penwidth="1.5" tooltip="blitter.com/go/xs/xsnet.Dial | defined in net.go:899" ]
|
||||
"blitter.com/go/xs/xsnet.Init" [ fillcolor="moccasin" label="Init" penwidth="1.5" ]
|
||||
"blitter.com/go/xs/xsnet.Dial" [ label="Dial" penwidth="1.5" fillcolor="moccasin" ]
|
||||
|
||||
subgraph "cluster_*blitter.com/go/xs/xsnet.Conn" {
|
||||
fontcolor="#222222";
|
||||
|
|
@ -160,29 +154,29 @@ tooltip="type: *blitter.com/go/xs/xsnet.Conn";
|
|||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
|
||||
"(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ fillcolor="moccasin" label="WritePacket" penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).WritePacket | defined in net.go:1437" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).SetStatus" [ label="SetStatus" penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).SetStatus | defined in net.go:218" fillcolor="moccasin" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).GetStatus" [ fillcolor="moccasin" label="GetStatus" penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).GetStatus | defined in net.go:214" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).Close" [ fillcolor="moccasin" label="Close" penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).Close | defined in net.go:979" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).SetupChaff" [ penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).SetupChaff | defined in net.go:1563" fillcolor="moccasin" label="SetupChaff" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).EnableChaff" [ fillcolor="moccasin" label="EnableChaff" penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).EnableChaff | defined in net.go:1546" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).DisableChaff" [ fillcolor="moccasin" label="DisableChaff" penwidth="1.5" tooltip="(*blitter.com/go/xs/xsnet.Conn).DisableChaff | defined in net.go:1553" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff" [ tooltip="(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff | defined in net.go:1558" fillcolor="moccasin" label="ShutdownChaff" penwidth="1.5" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ penwidth="1.5" fillcolor="moccasin" label="WritePacket" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).SetStatus" [ fillcolor="moccasin" label="SetStatus" penwidth="1.5" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).Close" [ penwidth="1.5" fillcolor="moccasin" label="Close" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).SetupChaff" [ penwidth="1.5" fillcolor="moccasin" label="SetupChaff" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).EnableChaff" [ fillcolor="moccasin" label="EnableChaff" penwidth="1.5" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).DisableChaff" [ fillcolor="moccasin" label="DisableChaff" penwidth="1.5" ]
|
||||
"(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff" [ fillcolor="moccasin" label="ShutdownChaff" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_blitter.com/go/xs/xsnet.Conn" {
|
||||
label="(Conn)";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(Conn)";
|
||||
tooltip="type: blitter.com/go/xs/xsnet.Conn";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
|
||||
"(blitter.com/go/xs/xsnet.Conn).Read" [ penwidth="1.5" tooltip="(blitter.com/go/xs/xsnet.Conn).Read | defined in net.go:1192" fillcolor="moccasin" label="Read" ]
|
||||
"(blitter.com/go/xs/xsnet.Conn).Write" [ fillcolor="moccasin" label="Write" penwidth="1.5" tooltip="(blitter.com/go/xs/xsnet.Conn).Write | defined in net.go:1431" ]
|
||||
"(blitter.com/go/xs/xsnet.Conn).Read" [ label="Read" penwidth="1.5" fillcolor="moccasin" ]
|
||||
"(blitter.com/go/xs/xsnet.Conn).GetStatus" [ fillcolor="moccasin" label="GetStatus" penwidth="1.5" ]
|
||||
"(blitter.com/go/xs/xsnet.Conn).Write" [ label="Write" penwidth="1.5" fillcolor="moccasin" ]
|
||||
|
||||
}
|
||||
|
||||
|
|
@ -190,41 +184,41 @@ fillcolor="wheat2";
|
|||
|
||||
subgraph "cluster_compress/flate" {
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
label="flate";
|
||||
fillcolor="#E0FFE1";
|
||||
label="[compress/flate]";
|
||||
URL="/?f=compress/flate";
|
||||
penwidth="0.8";
|
||||
fontname="Tahoma bold";
|
||||
style="filled";
|
||||
fontname="bold";
|
||||
rank="sink";
|
||||
tooltip="package: compress/flate";
|
||||
|
||||
|
||||
subgraph "cluster_compress/flate.CorruptInputError" {
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(CorruptInputError)";
|
||||
tooltip="type: compress/flate.CorruptInputError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
|
||||
"(compress/flate.CorruptInputError).Error" [ penwidth="1.5" tooltip="(compress/flate.CorruptInputError).Error | defined in inflate.go:35" fillcolor="moccasin" label="Error" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_compress/flate.InternalError" {
|
||||
tooltip="type: compress/flate.InternalError";
|
||||
tooltip="type: compress/flate.CorruptInputError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(InternalError)";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(CorruptInputError)";
|
||||
|
||||
"(compress/flate.InternalError).Error" [ tooltip="(compress/flate.InternalError).Error | defined in inflate.go:42" fillcolor="moccasin" label="Error" penwidth="1.5" ]
|
||||
"(compress/flate.CorruptInputError).Error" [ penwidth="1.5" fillcolor="#adedad" label="Error" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_compress/flate.InternalError" {
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(InternalError)";
|
||||
tooltip="type: compress/flate.InternalError";
|
||||
penwidth="0.5";
|
||||
|
||||
"(compress/flate.InternalError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
|
|
@ -233,224 +227,210 @@ label="(InternalError)";
|
|||
subgraph "cluster_context" {
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
label="context";
|
||||
penwidth="0.8";
|
||||
fillcolor="lightyellow";
|
||||
fontname="Tahoma bold";
|
||||
fontname="bold";
|
||||
rank="sink";
|
||||
label="[context]";
|
||||
URL="/?f=context";
|
||||
tooltip="package: context";
|
||||
fillcolor="#E0FFE1";
|
||||
|
||||
|
||||
subgraph "cluster_context.deadlineExceededError" {
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(deadlineExceededError)";
|
||||
tooltip="type: context.deadlineExceededError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
|
||||
"(context.deadlineExceededError).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(context.deadlineExceededError).Error | defined in context.go:165" ]
|
||||
"(context.deadlineExceededError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/aes" {
|
||||
penwidth="0.8";
|
||||
style="filled";
|
||||
fontname="Tahoma bold";
|
||||
style="filled";
|
||||
fillcolor="#E0FFE1";
|
||||
rank="sink";
|
||||
label="aes";
|
||||
label="[crypto/aes]";
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
fontname="bold";
|
||||
URL="/?f=crypto/aes";
|
||||
tooltip="package: crypto/aes";
|
||||
fontsize="16";
|
||||
fillcolor="lightyellow";
|
||||
|
||||
|
||||
subgraph "cluster_crypto/aes.KeySizeError" {
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(KeySizeError)";
|
||||
tooltip="type: crypto/aes.KeySizeError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
|
||||
"(crypto/aes.KeySizeError).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(crypto/aes.KeySizeError).Error | defined in cipher.go:24" ]
|
||||
"(crypto/aes.KeySizeError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/tls" {
|
||||
penwidth="0.8";
|
||||
tooltip="package: crypto/tls";
|
||||
fontsize="16";
|
||||
fontname="Tahoma bold";
|
||||
URL="/?f=crypto/tls";
|
||||
tooltip="package: crypto/tls";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
fontname="bold";
|
||||
rank="sink";
|
||||
label="tls";
|
||||
label="[crypto/tls]";
|
||||
URL="/?f=crypto/tls";
|
||||
penwidth="0.8";
|
||||
fillcolor="#E0FFE1";
|
||||
|
||||
|
||||
subgraph "cluster_*crypto/tls.permanentError" {
|
||||
label="(*permanentError)";
|
||||
tooltip="type: *crypto/tls.permanentError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
subgraph "cluster_crypto/tls.RecordHeaderError" {
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
|
||||
"(*crypto/tls.permanentError).Error" [ tooltip="(*crypto/tls.permanentError).Error | defined in conn.go:184" fillcolor="moccasin" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/tls.RecordHeaderError" {
|
||||
fillcolor="wheat2";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(RecordHeaderError)";
|
||||
tooltip="type: crypto/tls.RecordHeaderError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
|
||||
"(crypto/tls.RecordHeaderError).Error" [ tooltip="(crypto/tls.RecordHeaderError).Error | defined in conn.go:571" fillcolor="moccasin" label="Error" penwidth="1.5" ]
|
||||
"(crypto/tls.RecordHeaderError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/tls.alert" {
|
||||
fontcolor="#222222";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(alert)";
|
||||
tooltip="type: crypto/tls.alert";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
|
||||
"(crypto/tls.alert).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(crypto/tls.alert).Error | defined in alert.go:97" ]
|
||||
"(crypto/tls.alert).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/x509" {
|
||||
URL="/?f=crypto/x509";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
fontname="Tahoma bold";
|
||||
rank="sink";
|
||||
label="x509";
|
||||
penwidth="0.8";
|
||||
tooltip="package: crypto/x509";
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
fillcolor="#E0FFE1";
|
||||
fontname="bold";
|
||||
rank="sink";
|
||||
label="[crypto/x509]";
|
||||
URL="/?f=crypto/x509";
|
||||
|
||||
|
||||
subgraph "cluster_crypto/x509.CertificateInvalidError" {
|
||||
label="(CertificateInvalidError)";
|
||||
tooltip="type: crypto/x509.CertificateInvalidError";
|
||||
penwidth="0.5";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(CertificateInvalidError)";
|
||||
tooltip="type: crypto/x509.CertificateInvalidError";
|
||||
|
||||
"(crypto/x509.CertificateInvalidError).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(crypto/x509.CertificateInvalidError).Error | defined in verify.go:67" ]
|
||||
"(crypto/x509.CertificateInvalidError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/x509.HostnameError" {
|
||||
tooltip="type: crypto/x509.HostnameError";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(HostnameError)";
|
||||
tooltip="type: crypto/x509.HostnameError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(HostnameError)";
|
||||
|
||||
"(crypto/x509.HostnameError).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(crypto/x509.HostnameError).Error | defined in verify.go:98" ]
|
||||
"(crypto/x509.HostnameError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/x509.SystemRootsError" {
|
||||
tooltip="type: crypto/x509.SystemRootsError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(SystemRootsError)";
|
||||
tooltip="type: crypto/x509.SystemRootsError";
|
||||
penwidth="0.5";
|
||||
|
||||
"(crypto/x509.SystemRootsError).Error" [ label="Error" penwidth="1.5" tooltip="(crypto/x509.SystemRootsError).Error | defined in verify.go:159" fillcolor="moccasin" ]
|
||||
"(crypto/x509.SystemRootsError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/x509.UnhandledCriticalExtension" {
|
||||
label="(UnhandledCriticalExtension)";
|
||||
style="rounded,filled";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(UnhandledCriticalExtension)";
|
||||
tooltip="type: crypto/x509.UnhandledCriticalExtension";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
|
||||
"(crypto/x509.UnhandledCriticalExtension).Error" [ label="Error" penwidth="1.5" tooltip="(crypto/x509.UnhandledCriticalExtension).Error | defined in x509.go:893" fillcolor="moccasin" ]
|
||||
"(crypto/x509.UnhandledCriticalExtension).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_crypto/x509.UnknownAuthorityError" {
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
style="rounded,filled";
|
||||
fillcolor="#c2e3c2";
|
||||
label="(UnknownAuthorityError)";
|
||||
tooltip="type: crypto/x509.UnknownAuthorityError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
|
||||
"(crypto/x509.UnknownAuthorityError).Error" [ tooltip="(crypto/x509.UnknownAuthorityError).Error | defined in verify.go:138" fillcolor="moccasin" label="Error" penwidth="1.5" ]
|
||||
"(crypto/x509.UnknownAuthorityError).Error" [ fillcolor="#adedad" label="Error" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_github.com/mattn/go-isatty" {
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
fontname="Tahoma bold";
|
||||
rank="sink";
|
||||
style="filled";
|
||||
fontname="bold";
|
||||
penwidth="0.8";
|
||||
fillcolor="lightyellow";
|
||||
label="isatty";
|
||||
rank="sink";
|
||||
label="[isatty]";
|
||||
URL="/?f=github.com/mattn/go-isatty";
|
||||
tooltip="package: github.com/mattn/go-isatty";
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
|
||||
"github.com/mattn/go-isatty.IsTerminal" [ penwidth="1.5" tooltip="github.com/mattn/go-isatty.IsTerminal | defined in isatty_tcgets.go:10" fillcolor="moccasin" label="IsTerminal" ]
|
||||
"github.com/mattn/go-isatty.IsTerminal" [ label="IsTerminal" penwidth="1.5" fillcolor="moccasin" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_github.com/pkg/errors" {
|
||||
fontname="Tahoma bold";
|
||||
label="errors";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
URL="/?f=github.com/pkg/errors";
|
||||
tooltip="package: github.com/pkg/errors";
|
||||
rank="sink";
|
||||
label="[errors]";
|
||||
tooltip="package: github.com/pkg/errors";
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
fontname="bold";
|
||||
|
||||
|
||||
subgraph "cluster_*github.com/pkg/errors.fundamental" {
|
||||
|
|
@ -463,160 +443,107 @@ labelloc="b";
|
|||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
|
||||
"(*github.com/pkg/errors.fundamental).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(*github.com/pkg/errors.fundamental).Error | defined in errors.go:125" ]
|
||||
"(*github.com/pkg/errors.fundamental).Error" [ penwidth="1.5" fillcolor="moccasin" label="Error" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_math/rand" {
|
||||
style="filled";
|
||||
fillcolor="lightyellow";
|
||||
penwidth="0.8";
|
||||
fillcolor="#E0FFE1";
|
||||
rank="sink";
|
||||
URL="/?f=math/rand";
|
||||
tooltip="package: math/rand";
|
||||
penwidth="0.8";
|
||||
fontsize="16";
|
||||
fontname="Tahoma bold";
|
||||
label="rand";
|
||||
|
||||
"math/rand.Intn" [ fillcolor="moccasin" label="Intn" penwidth="1.5" tooltip="math/rand.Intn | defined in rand.go:337" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_vendor/golang.org/x/net/idna" {
|
||||
URL="/?f=vendor/golang.org/x/net/idna";
|
||||
penwidth="0.8";
|
||||
fontname="Tahoma bold";
|
||||
fillcolor="lightyellow";
|
||||
rank="sink";
|
||||
label="idna";
|
||||
tooltip="package: vendor/golang.org/x/net/idna";
|
||||
fontsize="16";
|
||||
style="filled";
|
||||
fontname="bold";
|
||||
label="[math/rand]";
|
||||
tooltip="package: math/rand";
|
||||
|
||||
|
||||
subgraph "cluster_vendor/golang.org/x/net/idna.labelError" {
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(labelError)";
|
||||
tooltip="type: vendor/golang.org/x/net/idna.labelError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
|
||||
"(vendor/golang.org/x/net/idna.labelError).Error" [ fillcolor="moccasin" label="Error" penwidth="1.5" tooltip="(vendor/golang.org/x/net/idna.labelError).Error | defined in idna10.0.0.go:324" ]
|
||||
|
||||
}
|
||||
|
||||
subgraph "cluster_vendor/golang.org/x/net/idna.runeError" {
|
||||
style="rounded,filled";
|
||||
fillcolor="wheat2";
|
||||
label="(runeError)";
|
||||
tooltip="type: vendor/golang.org/x/net/idna.runeError";
|
||||
penwidth="0.5";
|
||||
fontsize="15";
|
||||
fontcolor="#222222";
|
||||
labelloc="b";
|
||||
|
||||
"(vendor/golang.org/x/net/idna.runeError).Error" [ tooltip="(vendor/golang.org/x/net/idna.runeError).Error | defined in idna10.0.0.go:331" fillcolor="moccasin" label="Error" penwidth="1.5" ]
|
||||
"math/rand.Intn" [ fillcolor="#adedad" label="Intn" penwidth="1.5" ]
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
}
|
||||
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "blitter.com/go/xs/xs.exitWithStatus" [ tooltip="at xs.go:509: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:519: calling [blitter.com/go/xs/xs.exitWithStatus]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.SystemRootsError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/x509.SystemRootsError).Error]" ]
|
||||
"blitter.com/go/xs/xs.main$2" -> "blitter.com/go/xs/xs.exitWithStatus" [ tooltip="at xs.go:999: calling [blitter.com/go/xs/xs.exitWithStatus]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(*blitter.com/go/xs/xsnet.Conn).GetStatus" [ color="saddlebrown" tooltip="at xs.go:435: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:438: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:473: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]\nat xs.go:475: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff" [ arrowhead="normalnoneodiamond" color="saddlebrown" tooltip="at xs.go:1056: calling [(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(*blitter.com/go/xs.Session).SetStatus" [ color="saddlebrown" tooltip="at xs.go:513: calling [(*blitter.com/go/xs.Session).SetStatus]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" -> "blitter.com/go/xs/xs.doShellMode$1" [ arrowhead="normalnoneodot" tooltip="at xs.go:522: calling [blitter.com/go/xs/xs.doShellMode$1]" ]
|
||||
"blitter.com/go/xs/xs.main$2" -> "blitter.com/go/xs/xs.restoreTermState" [ tooltip="at xs.go:997: calling [blitter.com/go/xs/xs.restoreTermState]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(*blitter.com/go/xs/xsnet.Conn).SetStatus" [ color="saddlebrown" tooltip="at xs.go:430: calling [(*blitter.com/go/xs/xsnet.Conn).SetStatus]" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).Cmd" [ tooltip="at xs.go:651: calling [(blitter.com/go/xs.Session).Cmd]\nat xs.go:671: calling [(blitter.com/go/xs.Session).Cmd]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(blitter.com/go/xs.Session).Status" [ color="saddlebrown" tooltip="at xs.go:1027: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:1089: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:1091: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:1101: calling [(blitter.com/go/xs.Session).Status]" ]
|
||||
"blitter.com/go/xs/xs.main$3" -> "math/rand.Intn" [ tooltip="at xs.go:1068: calling [math/rand.Intn]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.CertificateInvalidError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/x509.CertificateInvalidError).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" -> "blitter.com/go/xs/xs.restoreTermState" [ tooltip="at xs.go:546: calling [blitter.com/go/xs/xs.restoreTermState]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" -> "blitter.com/go/xs/xs.exitWithStatus" [ tooltip="at xs.go:548: calling [blitter.com/go/xs/xs.exitWithStatus]" ]
|
||||
"blitter.com/go/xs/xs.restoreTermState" -> "blitter.com/go/xs.Restore" [ color="saddlebrown" tooltip="at xs.go:1118: calling [blitter.com/go/xs.Restore]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/logger.New" [ color="saddlebrown" tooltip="at xs.go:864: calling [blitter.com/go/xs/logger.New]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.MakeRaw" [ color="saddlebrown" tooltip="at xs.go:978: calling [blitter.com/go/xs.MakeRaw]" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).AuthCookie" [ color="saddlebrown" tooltip="at xs.go:651: calling [(blitter.com/go/xs.Session).AuthCookie]\nat xs.go:675: calling [(blitter.com/go/xs.Session).AuthCookie]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.main$3" [ arrowhead="normalnoneodot" tooltip="at xs.go:1075: calling [blitter.com/go/xs/xs.main$3]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "blitter.com/go/xs/xs.buildCmdRemoteToLocal" [ tooltip="at xs.go:444: calling [blitter.com/go/xs/xs.buildCmdRemoteToLocal]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(blitter.com/go/xs/xsnet.Conn).Read" [ color="saddlebrown" tooltip="at xs.go:424: calling [(blitter.com/go/xs/xsnet.Conn).Read]" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).Who" [ tooltip="at xs.go:651: calling [(blitter.com/go/xs.Session).Who]\nat xs.go:659: calling [(blitter.com/go/xs.Session).Who]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(blitter.com/go/xs/xsnet.Conn).Read" [ color="saddlebrown" tooltip="at xs.go:1039: calling [(blitter.com/go/xs/xsnet.Conn).Read]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xsnet.Dial" [ color="saddlebrown" tooltip="at xs.go:960: calling [blitter.com/go/xs/xsnet.Dial]" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).Op" [ color="saddlebrown" tooltip="at xs.go:651: calling [(blitter.com/go/xs.Session).Op]\nat xs.go:655: calling [(blitter.com/go/xs.Session).Op]" ]
|
||||
"blitter.com/go/xs/xs.rejectUserMsg" -> "blitter.com/go/xs/spinsult.GetSentence" [ color="saddlebrown" tooltip="at xs.go:577: calling [blitter.com/go/xs/spinsult.GetSentence]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.launchTuns" [ tooltip="at xs.go:1081: calling [blitter.com/go/xs/xs.launchTuns]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(vendor/golang.org/x/net/idna.labelError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(vendor/golang.org/x/net/idna.labelError).Error]" ]
|
||||
"blitter.com/go/xs/xs.Copy" -> "blitter.com/go/xs/xs.copyBuffer" [ tooltip="at xs.go:116: calling [blitter.com/go/xs/xs.copyBuffer]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "github.com/mattn/go-isatty.IsTerminal" [ color="saddlebrown" tooltip="at xs.go:977: calling [github.com/mattn/go-isatty.IsTerminal]" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).TermType" [ color="saddlebrown" tooltip="at xs.go:651: calling [(blitter.com/go/xs.Session).TermType]\nat xs.go:667: calling [(blitter.com/go/xs.Session).TermType]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/tls.RecordHeaderError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/tls.RecordHeaderError).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.UnknownAuthorityError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/x509.UnknownAuthorityError).Error]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.exitWithStatus" [ tooltip="at xs.go:772: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:853: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:963: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:1027: calling [blitter.com/go/xs/xs.exitWithStatus]\nat xs.go:1101: calling [blitter.com/go/xs/xs.exitWithStatus]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" -> "blitter.com/go/xs/xs.doShellMode$2$1" [ tooltip="at xs.go:541: calling [blitter.com/go/xs/xs.doShellMode$2$1]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.doShellMode" [ tooltip="at xs.go:1082: calling [blitter.com/go/xs/xs.doShellMode]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" -> "blitter.com/go/xs/xs.doShellMode$2" [ arrowhead="normalnoneodot" tooltip="at xs.go:551: calling [blitter.com/go/xs/xs.doShellMode$2]" ]
|
||||
"blitter.com/go/xs/xs.buildCmdLocalToRemote" -> "blitter.com/go/xs.GetTool" [ color="saddlebrown" tooltip="at xs.go:283: calling [blitter.com/go/xs.GetTool]\nat xs.go:311: calling [blitter.com/go/xs.GetTool]\nat xs.go:312: calling [blitter.com/go/xs.GetTool]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(*blitter.com/go/xs/xsnet.Conn).GetStatus" [ color="saddlebrown" tooltip="at xs.go:513: calling [(*blitter.com/go/xs/xsnet.Conn).GetStatus]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/tls.alert).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/tls.alert).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" -> "blitter.com/go/xs/xs.handleTermResizes" [ tooltip="at xs.go:527: calling [blitter.com/go/xs/xs.handleTermResizes]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).SetupChaff" [ color="saddlebrown" tooltip="at xs.go:1050: calling [(*blitter.com/go/xs/xsnet.Conn).SetupChaff]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(context.deadlineExceededError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(context.deadlineExceededError).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/aes.KeySizeError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/aes.KeySizeError).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2$1" -> "blitter.com/go/xs/xs.Copy" [ tooltip="at xs.go:539: calling [blitter.com/go/xs/xs.Copy]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(blitter.com/go/xs.Session).Cmd" [ color="saddlebrown" tooltip="at xs.go:356: calling [(blitter.com/go/xs.Session).Cmd]\nat xs.go:441: calling [(blitter.com/go/xs.Session).Cmd]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ tooltip="at xs.go:417: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).ConnHost" [ color="saddlebrown" tooltip="at xs.go:651: calling [(blitter.com/go/xs.Session).ConnHost]\nat xs.go:663: calling [(blitter.com/go/xs.Session).ConnHost]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.sendSessionParams" [ tooltip="at xs.go:1022: calling [blitter.com/go/xs/xs.sendSessionParams]" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "blitter.com/go/xs/xs.buildCmdLocalToRemote" [ tooltip="at xs.go:364: calling [blitter.com/go/xs/xs.buildCmdLocalToRemote]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.parseNonSwitchArgs" [ tooltip="at xs.go:796: calling [blitter.com/go/xs/xs.parseNonSwitchArgs]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.restoreTermState" [ tooltip="at xs.go:1024: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:1090: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:1096: calling [blitter.com/go/xs/xs.restoreTermState]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).DisableChaff" [ color="saddlebrown" tooltip="at xs.go:1055: calling [(*blitter.com/go/xs/xsnet.Conn).DisableChaff]" arrowhead="normalnoneodiamond" ]
|
||||
"blitter.com/go/xs/xs.launchTuns" -> "blitter.com/go/xs/xs.reqTunnel" [ tooltip="at xs.go:645: calling [blitter.com/go/xs/xs.reqTunnel]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.UnhandledCriticalExtension).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/x509.UnhandledCriticalExtension).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(compress/flate.CorruptInputError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(compress/flate.CorruptInputError).Error]" ]
|
||||
"blitter.com/go/xs/xs.buildCmdLocalToRemote" -> "blitter.com/go/xs/xs.getTreeSizeSubCmd" [ tooltip="at xs.go:335: calling [blitter.com/go/xs/xs.getTreeSizeSubCmd]" ]
|
||||
"blitter.com/go/xs/xs.buildCmdRemoteToLocal" -> "blitter.com/go/xs.GetTool" [ color="saddlebrown" tooltip="at xs.go:256: calling [blitter.com/go/xs.GetTool]\nat xs.go:263: calling [blitter.com/go/xs.GetTool]" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs/xsnet.Conn).Write" [ style="dashed" color="saddlebrown" tooltip="at xs.go:675: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:671: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:667: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:663: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:659: calling [(blitter.com/go/xs/xsnet.Conn).Write]\nat xs.go:655: calling [(blitter.com/go/xs/xsnet.Conn).Write]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs.Session).SetStatus" [ color="saddlebrown" tooltip="at xs.go:1025: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:1043: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:1047: calling [(*blitter.com/go/xs.Session).SetStatus]\nat xs.go:1086: calling [(*blitter.com/go/xs.Session).SetStatus]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(*github.com/pkg/errors.fundamental).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(*github.com/pkg/errors.fundamental).Error]" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes" -> "blitter.com/go/xs/xs.handleTermResizes$1" [ arrowhead="normalnoneodot" tooltip="at termsize_unix.go:21: calling [blitter.com/go/xs/xs.handleTermResizes$1]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.usageShell" [ style="dashed" tooltip="at xs.go:852: calling [blitter.com/go/xs/xs.usageShell]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.restoreTermState" [ arrowhead="normalnoneodiamond" tooltip="at xs.go:984: calling [blitter.com/go/xs/xs.restoreTermState]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.ReadPassword" [ color="saddlebrown" tooltip="at xs.go:1005: calling [blitter.com/go/xs.ReadPassword]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "blitter.com/go/xs/xs.doShellMode$1$1" [ arrowhead="normalnoneodiamond" tooltip="at xs.go:491: calling [blitter.com/go/xs/xs.doShellMode$1$1]" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes$1" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ color="saddlebrown" tooltip="at termsize_unix.go:33: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).EnableChaff" [ color="saddlebrown" tooltip="at xs.go:1054: calling [(*blitter.com/go/xs/xsnet.Conn).EnableChaff]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.HostnameError).Error" [ style="dashed" color="saddlebrown" tooltip="at xs.go:507: calling [(crypto/x509.HostnameError).Error]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(*crypto/tls.permanentError).Error" [ color="saddlebrown" tooltip="at xs.go:507: calling [(*crypto/tls.permanentError).Error]" style="dashed" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.doCopyMode" [ tooltip="at xs.go:1085: calling [blitter.com/go/xs/xs.doCopyMode]" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "blitter.com/go/xs/xs.copyBuffer$2" [ style="dashed" tooltip="at xs.go:186: calling [blitter.com/go/xs/xs.copyBuffer$2]" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "blitter.com/go/xs/xs.copyBuffer$3" [ style="dashed" tooltip="at xs.go:186: calling [blitter.com/go/xs/xs.copyBuffer$3]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).Close" [ arrowhead="normalnoneodiamond" color="saddlebrown" tooltip="at xs.go:972: calling [(*blitter.com/go/xs/xsnet.Conn).Close]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.rejectUserMsg" [ tooltip="at xs.go:1046: calling [blitter.com/go/xs/xs.rejectUserMsg]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.usageCp" [ tooltip="at xs.go:852: calling [blitter.com/go/xs/xs.usageCp]" style="dashed" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(vendor/golang.org/x/net/idna.runeError).Error" [ color="saddlebrown" tooltip="at xs.go:507: calling [(vendor/golang.org/x/net/idna.runeError).Error]" style="dashed" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "(blitter.com/go/xs/xsnet.Conn).Write" [ tooltip="at xs.go:193: calling [(blitter.com/go/xs/xsnet.Conn).Write]" style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "blitter.com/go/xs/xs.copyBuffer$1" [ style="dashed" tooltip="at xs.go:186: calling [blitter.com/go/xs/xs.copyBuffer$1]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.main$1" [ tooltip="at xs.go:790: calling [blitter.com/go/xs/xs.main$1]" arrowhead="normalnoneodot" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.localUserName" [ tooltip="at xs.go:803: calling [blitter.com/go/xs/xs.localUserName]" ]
|
||||
"blitter.com/go/xs/xs.reqTunnel" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ color="saddlebrown" tooltip="at xs.go:594: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xsnet.Init" [ color="saddlebrown" tooltip="at xs.go:865: calling [blitter.com/go/xs/xsnet.Init]" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.NewSession" [ tooltip="at xs.go:1021: calling [blitter.com/go/xs.NewSession]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(blitter.com/go/xs.Session).Status" [ tooltip="at xs.go:514: calling [(blitter.com/go/xs.Session).Status]\nat xs.go:519: calling [(blitter.com/go/xs.Session).Status]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes$1" -> "blitter.com/go/xs/xs.GetSize" [ tooltip="at termsize_unix.go:27: calling [blitter.com/go/xs/xs.GetSize]" ]
|
||||
"blitter.com/go/xs/xs.reqTunnel" -> "blitter.com/go/xs/logger.LogDebug" [ color="saddlebrown" tooltip="at xs.go:593: calling [blitter.com/go/xs/logger.LogDebug]" ]
|
||||
"blitter.com/go/xs/xs.main$3" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ tooltip="at xs.go:1072: calling [(*blitter.com/go/xs/xsnet.Conn).WritePacket]" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "blitter.com/go/xs/xs.restoreTermState" [ tooltip="at xs.go:503: calling [blitter.com/go/xs/xs.restoreTermState]\nat xs.go:518: calling [blitter.com/go/xs/xs.restoreTermState]" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(compress/flate.InternalError).Error" [ tooltip="at xs.go:507: calling [(compress/flate.InternalError).Error]" style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.reqTunnel" -> "blitter.com/go/xs/logger.LogDebug" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.reqTunnel" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.launchTuns" -> "blitter.com/go/xs/xs.reqTunnel" [ ]
|
||||
"blitter.com/go/xs/xs.main$3" -> "math/rand.Intn" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main$3" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(blitter.com/go/xs.Session).Cmd" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(blitter.com/go/xs/xsnet.Conn).Read" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(*blitter.com/go/xs/xsnet.Conn).SetStatus" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doCopyMode" -> "(blitter.com/go/xs/xsnet.Conn).GetStatus" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "(blitter.com/go/xs/xsnet.Conn).Write" [ color="saddlebrown" style="dashed" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "blitter.com/go/xs/xs.copyBuffer$1" [ style="dashed" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "blitter.com/go/xs/xs.copyBuffer$2" [ style="dashed" ]
|
||||
"blitter.com/go/xs/xs.copyBuffer" -> "blitter.com/go/xs/xs.copyBuffer$3" [ style="dashed" ]
|
||||
"blitter.com/go/xs/xs.Copy" -> "blitter.com/go/xs/xs.copyBuffer" [ ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "blitter.com/go/xs/xs.doShellMode$1$1" [ arrowhead="normalnoneodiamond" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "blitter.com/go/xs.Restore" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(blitter.com/go/xs/xsnet.Conn).GetStatus" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(*blitter.com/go/xs.Session).SetStatus" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(blitter.com/go/xs.Session).Status" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "blitter.com/go/xs/xs.exitWithStatus" [ ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.CertificateInvalidError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/aes.KeySizeError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.HostnameError).Error" [ color="saddlebrown" style="dashed" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.UnhandledCriticalExtension).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(context.deadlineExceededError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(compress/flate.CorruptInputError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/tls.RecordHeaderError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.UnknownAuthorityError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/x509.SystemRootsError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(compress/flate.InternalError).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(crypto/tls.alert).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$1" -> "(*github.com/pkg/errors.fundamental).Error" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" -> "blitter.com/go/xs/xs.doShellMode$1" [ arrowhead="normalnoneodot" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes$1" -> "blitter.com/go/xs/xs.GetSize" [ ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes$1" -> "(*blitter.com/go/xs/xsnet.Conn).WritePacket" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.handleTermResizes" -> "blitter.com/go/xs/xs.handleTermResizes$1" [ arrowhead="normalnoneodot" ]
|
||||
"blitter.com/go/xs/xs.doShellMode" -> "blitter.com/go/xs/xs.handleTermResizes" [ ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2$1" -> "blitter.com/go/xs/xs.Copy" [ ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" -> "blitter.com/go/xs/xs.doShellMode$2$1" [ ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" -> "blitter.com/go/xs.Restore" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.doShellMode$2" -> "blitter.com/go/xs/xs.exitWithStatus" [ ]
|
||||
"blitter.com/go/xs/xs.doShellMode" -> "blitter.com/go/xs/xs.doShellMode$2" [ arrowhead="normalnoneodot" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).Op" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).Who" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).ConnHost" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).TermType" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).Cmd" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs.Session).AuthCookie" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.sendSessionParams" -> "(blitter.com/go/xs/xsnet.Conn).Write" [ style="dashed" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.parseNonSwitchArgs" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.main$1" [ arrowhead="normalnoneodot" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.exitWithStatus" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/logger.New" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xsnet.Init" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xsnet.Dial" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).Close" [ arrowhead="normalnoneodiamond" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "github.com/mattn/go-isatty.IsTerminal" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.MakeRaw" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main$2" -> "blitter.com/go/xs.Restore" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.main$2" [ arrowhead="normalnoneodiamond" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.ReadPassword" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.NewSession" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.sendSessionParams" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "(blitter.com/go/xs/xsnet.Conn).Read" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs.Session).SetStatus" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.rejectUserMsg" -> "blitter.com/go/xs/spinsult.GetSentence" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.rejectUserMsg" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).SetupChaff" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).EnableChaff" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).DisableChaff" [ arrowhead="normalnoneodiamond" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "(*blitter.com/go/xs/xsnet.Conn).ShutdownChaff" [ arrowhead="normalnoneodiamond" color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.main$3" [ arrowhead="normalnoneodot" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.launchTuns" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.doShellMode" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "(blitter.com/go/xs.Session).Status" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.doCopyMode" [ ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs.Restore" [ color="saddlebrown" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.usageShell" [ style="dashed" ]
|
||||
"blitter.com/go/xs/xs.main" -> "blitter.com/go/xs/xs.usageCp" [ style="dashed" ]
|
||||
}
|
||||
|
|
|
|||
446
xs/xs.go
446
xs/xs.go
|
|
@ -1,6 +1,7 @@
|
|||
// xs client
|
||||
|
||||
//
|
||||
// Copyright (c) 2017-2025 Russell Magee
|
||||
// Copyright (c) 2017-2020 Russell Magee
|
||||
// Licensed under the terms of the MIT license (see LICENSE.mit in this
|
||||
// distribution)
|
||||
//
|
||||
|
|
@ -14,8 +15,10 @@ import (
|
|||
"flag"
|
||||
"fmt"
|
||||
"io"
|
||||
"io/ioutil"
|
||||
"log"
|
||||
"math/rand"
|
||||
"net"
|
||||
"os"
|
||||
"os/exec"
|
||||
"os/user"
|
||||
|
|
@ -29,14 +32,13 @@ import (
|
|||
"time"
|
||||
|
||||
"net/http"
|
||||
_ "net/http/pprof" //nolint:gosec
|
||||
_ "net/http/pprof"
|
||||
|
||||
xs "blitter.com/go/xs"
|
||||
"blitter.com/go/xs/logger"
|
||||
"blitter.com/go/spinsult"
|
||||
"blitter.com/go/xs/spinsult"
|
||||
"blitter.com/go/xs/xsnet"
|
||||
"github.com/mattn/go-isatty"
|
||||
//isatty "github.com/mattn/go-isatty"
|
||||
isatty "github.com/mattn/go-isatty"
|
||||
)
|
||||
|
||||
var (
|
||||
|
|
@ -57,18 +59,6 @@ var (
|
|||
|
||||
////////////////////////////////////////////////////
|
||||
|
||||
const (
|
||||
CmdExitedEarly = 2
|
||||
XSNetDialFailed = 3
|
||||
ErrReadingAuthReply = 253
|
||||
ServerRejectedSecureProposal = 254
|
||||
GeneralProtocolErr = 255
|
||||
)
|
||||
|
||||
const (
|
||||
DeadCharPrefix = 0x1d
|
||||
)
|
||||
|
||||
// Praise Bob. Do not remove, lest ye lose Slack.
|
||||
const bob = string("\r\n\r\n" +
|
||||
"@@@@@@@^^~~~~~~~~~~~~~~~~~~~~^@@@@@@@@@\r\n" +
|
||||
|
|
@ -103,14 +93,6 @@ type (
|
|||
escSeqs map[byte]escHandler
|
||||
)
|
||||
|
||||
var (
|
||||
escs = escSeqs{
|
||||
'i': func(io.Writer) { os.Stdout.Write([]byte("\x1b[s\x1b[2;1H\x1b[1;31m[HKEXSH]\x1b[39;49m\x1b[u")) },
|
||||
't': func(io.Writer) { os.Stdout.Write([]byte("\x1b[1;32m[HKEXSH]\x1b[39;49m")) },
|
||||
'B': func(io.Writer) { os.Stdout.Write([]byte("\x1b[1;32m" + bob + "\x1b[39;49m")) },
|
||||
}
|
||||
)
|
||||
|
||||
// Copy copies from src to dst until either EOF is reached
|
||||
// on src or an error occurs. It returns the number of bytes
|
||||
// copied and the first error encountered while copying, if any.
|
||||
|
|
@ -158,6 +140,11 @@ func copyBuffer(dst io.Writer, src io.Reader, buf []byte) (written int64, err er
|
|||
// or tunnel traffic indicator - note we cannot just spawn a goroutine
|
||||
// here, as copyBuffer() returns after each burst of data. Scope must
|
||||
// outlive individual copyBuffer calls).
|
||||
escs := escSeqs{
|
||||
'i': func(io.Writer) { os.Stdout.Write([]byte("\x1b[s\x1b[2;1H\x1b[1;31m[HKEXSH]\x1b[39;49m\x1b[u")) },
|
||||
't': func(io.Writer) { os.Stdout.Write([]byte("\x1b[1;32m[HKEXSH]\x1b[39;49m")) },
|
||||
'B': func(io.Writer) { os.Stdout.Write([]byte("\x1b[1;32m" + bob + "\x1b[39;49m")) },
|
||||
}
|
||||
|
||||
/*
|
||||
// If the reader has a WriteTo method, use it to do the copy.
|
||||
|
|
@ -169,7 +156,7 @@ func copyBuffer(dst io.Writer, src io.Reader, buf []byte) (written int64, err er
|
|||
if rt, ok := dst.(io.ReaderFrom); ok {
|
||||
return rt.ReadFrom(src)
|
||||
}
|
||||
*/ //nolint:gocritic,nolintlint
|
||||
*/
|
||||
if buf == nil {
|
||||
size := 32 * 1024
|
||||
if l, ok := src.(*io.LimitedReader); ok && int64(size) > l.N {
|
||||
|
|
@ -190,8 +177,8 @@ func copyBuffer(dst io.Writer, src io.Reader, buf []byte) (written int64, err er
|
|||
// A repeat of 4 keys (conveniently 'dead' chars for most
|
||||
// interactive shells; here CTRL-]) shall introduce
|
||||
// some special responses or actions on the client side.
|
||||
if seqPos < 4 { //nolint:gomnd
|
||||
if buf[0] == DeadCharPrefix {
|
||||
if seqPos < 4 {
|
||||
if buf[0] == 0x1d {
|
||||
seqPos++
|
||||
}
|
||||
} else {
|
||||
|
|
@ -238,7 +225,7 @@ func GetSize() (cols, rows int, err error) {
|
|||
|
||||
if err != nil {
|
||||
log.Println(err)
|
||||
cols, rows = 80, 24 // failsafe
|
||||
cols, rows = 80, 24 //failsafe
|
||||
} else {
|
||||
n, err := fmt.Sscanf(string(out), "%d %d\n", &rows, &cols)
|
||||
if n < 2 ||
|
||||
|
|
@ -254,7 +241,7 @@ func GetSize() (cols, rows int, err error) {
|
|||
return
|
||||
}
|
||||
|
||||
func buildCmdRemoteToLocal(copyQuiet bool, copyLimitBPS uint, destPath string) (captureStderr bool, cmd string, args []string) {
|
||||
func buildCmdRemoteToLocal(copyQuiet bool, copyLimitBPS uint, destPath, files string) (captureStderr bool, cmd string, args []string) {
|
||||
// Detect if we have 'pv'
|
||||
// pipeview http://www.ivarch.com/programs/pv.shtml
|
||||
// and use it for nice client progress display.
|
||||
|
|
@ -272,7 +259,7 @@ func buildCmdRemoteToLocal(copyQuiet bool, copyLimitBPS uint, destPath string) (
|
|||
} else {
|
||||
// TODO: Query remote side for total file/dir size
|
||||
bandwidthInBytesPerSec := " -L " + fmt.Sprintf("%d ", copyLimitBPS)
|
||||
displayOpts := " -pre " //nolint:goconst
|
||||
displayOpts := " -pre "
|
||||
cmd = xs.GetTool("bash")
|
||||
args = []string{"-c", "pv " + displayOpts + bandwidthInBytesPerSec + "| tar -xz -C " + destPath}
|
||||
}
|
||||
|
|
@ -294,14 +281,7 @@ func buildCmdLocalToRemote(copyQuiet bool, copyLimitBPS uint, files string) (cap
|
|||
|
||||
captureStderr = true
|
||||
cmd = xs.GetTool("tar")
|
||||
//fmt.Printf("GetTool found cmd:%v\n", cmd)
|
||||
/* Explicit -f /dev/stdout doesn't work in MINGW/MSYS64
|
||||
* as '/dev/stdout' doesn't actually appear in the /dev/ filesystem...?
|
||||
* And it appears not to actually be required as without -f stdout is
|
||||
* implied. -rlm 2025-12-07
|
||||
*/
|
||||
//args = []string{"-cz", "-f", "/dev/stdout"}
|
||||
args = []string{"-cz"}
|
||||
args = []string{"-cz", "-f", "/dev/stdout"}
|
||||
files = strings.TrimSpace(files)
|
||||
// Awesome fact: tar actually can take multiple -C args, and
|
||||
// changes to the dest dir *as it sees each one*. This enables
|
||||
|
|
@ -317,7 +297,6 @@ func buildCmdLocalToRemote(copyQuiet bool, copyLimitBPS uint, files string) (cap
|
|||
// remote destDir.
|
||||
for _, v := range strings.Split(files, " ") {
|
||||
v, _ = filepath.Abs(v) // #nosec
|
||||
v = xs.GroomFsPath(v)
|
||||
dirTmp, fileTmp := path.Split(v)
|
||||
if dirTmp == "" {
|
||||
args = append(args, fileTmp)
|
||||
|
|
@ -328,10 +307,9 @@ func buildCmdLocalToRemote(copyQuiet bool, copyLimitBPS uint, files string) (cap
|
|||
} else {
|
||||
captureStderr = copyQuiet
|
||||
bandwidthInBytesPerSec := " -L " + fmt.Sprintf("%d", copyLimitBPS)
|
||||
displayOpts := " -pre " //nolint:goconst,nolintlint
|
||||
displayOpts := " -pre "
|
||||
cmd = xs.GetTool("bash")
|
||||
//args = []string{"-c", xs.GetTool("tar") + " -cz -f /dev/stdout "}
|
||||
args = []string{"-c", xs.GetTool("tar") + " -cz "}
|
||||
args = []string{"-c", xs.GetTool("tar") + " -cz -f /dev/stdout "}
|
||||
files = strings.TrimSpace(files)
|
||||
// Awesome fact: tar actually can take multiple -C args, and
|
||||
// changes to the dest dir *as it sees each one*. This enables
|
||||
|
|
@ -347,7 +325,6 @@ func buildCmdLocalToRemote(copyQuiet bool, copyLimitBPS uint, files string) (cap
|
|||
// remote destDir.
|
||||
for _, v := range strings.Split(files, " ") {
|
||||
v, _ = filepath.Abs(v) // #nosec
|
||||
v = xs.GroomFsPath(v)
|
||||
dirTmp, fileTmp := path.Split(v)
|
||||
if dirTmp == "" {
|
||||
args[1] = args[1] + fileTmp + " "
|
||||
|
|
@ -380,9 +357,9 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
|
||||
var c *exec.Cmd
|
||||
|
||||
// os.Clearenv()
|
||||
// os.Setenv("HOME", u.HomeDir)
|
||||
// os.Setenv("TERM", "vt102") // TODO: server or client option?
|
||||
//os.Clearenv()
|
||||
//os.Setenv("HOME", u.HomeDir)
|
||||
//os.Setenv("TERM", "vt102") // TODO: server or client option?
|
||||
|
||||
captureStderr, cmdName, cmdArgs := buildCmdLocalToRemote(copyQuiet, copyLimitBPS, strings.TrimSpace(files))
|
||||
c = exec.Command(cmdName, cmdArgs...) // #nosec
|
||||
|
|
@ -396,8 +373,6 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
c.Stderr = os.Stderr
|
||||
}
|
||||
|
||||
//fmt.Printf("cmd:%v args:%v\n", cmdName, cmdArgs)
|
||||
|
||||
// Start the command (no pty)
|
||||
err = c.Start() // returns immediately
|
||||
/////////////
|
||||
|
|
@ -417,7 +392,7 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
if err != nil {
|
||||
fmt.Println("cmd exited immediately. Cannot get cmd.Wait().ExitStatus()")
|
||||
err = errors.New("cmd exited prematurely")
|
||||
exitStatus = uint32(CmdExitedEarly)
|
||||
exitStatus = uint32(2)
|
||||
} else {
|
||||
if err = c.Wait(); err != nil {
|
||||
if exiterr, ok := err.(*exec.ExitError); ok {
|
||||
|
|
@ -437,7 +412,7 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
}
|
||||
// send CSOExitStatus to inform remote (server) end cp is done
|
||||
log.Println("Sending local exitStatus:", exitStatus)
|
||||
r := make([]byte, 4) //nolint:gomnd
|
||||
r := make([]byte, 4)
|
||||
binary.BigEndian.PutUint32(r, exitStatus)
|
||||
_, we := conn.WritePacket(r, xsnet.CSOExitStatus)
|
||||
if we != nil {
|
||||
|
|
@ -445,7 +420,7 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
}
|
||||
|
||||
// Do a final read for remote's exit status
|
||||
s := make([]byte, 4) //nolint:gomnd
|
||||
s := make([]byte, 4)
|
||||
_, remErr := conn.Read(s)
|
||||
if remErr != io.EOF &&
|
||||
!strings.Contains(remErr.Error(), "use of closed network") &&
|
||||
|
|
@ -466,9 +441,10 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
log.Println("remote filepath:", string(rec.Cmd()), "local files:", files)
|
||||
destPath := files
|
||||
|
||||
_, cmdName, cmdArgs := buildCmdRemoteToLocal(copyQuiet, copyLimitBPS, destPath)
|
||||
_, cmdName, cmdArgs := buildCmdRemoteToLocal(copyQuiet, copyLimitBPS, destPath, strings.TrimSpace(files))
|
||||
|
||||
c := exec.Command(cmdName, cmdArgs...) // #nosec
|
||||
var c *exec.Cmd
|
||||
c = exec.Command(cmdName, cmdArgs...) // #nosec
|
||||
c.Stdin = conn
|
||||
c.Stdout = os.Stdout
|
||||
c.Stderr = os.Stderr
|
||||
|
|
@ -505,8 +481,8 @@ func doCopyMode(conn *xsnet.Conn, remoteDest bool, files string, copyQuiet bool,
|
|||
// doShellMode begins an xs shell session (one-shot command or
|
||||
// interactive).
|
||||
func doShellMode(isInteractive bool, conn *xsnet.Conn, oldState *xs.State, rec *xs.Session) {
|
||||
// Client reader (from server) goroutine
|
||||
// Read remote end's stdout
|
||||
//client reader (from server) goroutine
|
||||
//Read remote end's stdout
|
||||
|
||||
wg.Add(1)
|
||||
// #gv:s/label=\"doShellMode\$1\"/label=\"shellRemoteToStdin\"/
|
||||
|
|
@ -560,8 +536,6 @@ func doShellMode(isInteractive bool, conn *xsnet.Conn, oldState *xs.State, rec *
|
|||
_, outerr := func(conn *xsnet.Conn, r io.Reader) (w int64, e error) {
|
||||
// Copy() expects EOF so this will
|
||||
// exit with outerr == nil
|
||||
// NOTE we use a local implementation of Copy() to allow
|
||||
// for custom key sequences to trigger local actions
|
||||
w, e = Copy(conn, r)
|
||||
return w, e
|
||||
}(conn, os.Stdin)
|
||||
|
|
@ -583,15 +557,15 @@ func doShellMode(isInteractive bool, conn *xsnet.Conn, oldState *xs.State, rec *
|
|||
}
|
||||
|
||||
func usageShell() {
|
||||
fmt.Fprintf(os.Stderr, "Usage of %s:\n", os.Args[0])
|
||||
fmt.Fprintf(os.Stderr, "%s [opts] [user]@server\n", os.Args[0])
|
||||
fmt.Fprintf(os.Stderr, "Usage of %s:\n", os.Args[0]) // nolint: errcheck
|
||||
fmt.Fprintf(os.Stderr, "%s [opts] [user]@server\n", os.Args[0]) // nolint: errcheck
|
||||
flag.PrintDefaults()
|
||||
}
|
||||
|
||||
func usageCp() {
|
||||
fmt.Fprintf(os.Stderr, "Usage of %s:\n", os.Args[0])
|
||||
fmt.Fprintf(os.Stderr, "%s [opts] srcFileOrDir [...] [user]@server[:dstpath]\n", os.Args[0])
|
||||
fmt.Fprintf(os.Stderr, "%s [opts] [user]@server[:srcFileOrDir] dstPath\n", os.Args[0])
|
||||
fmt.Fprintf(os.Stderr, "Usage of %s:\n", os.Args[0]) // nolint: errcheck
|
||||
fmt.Fprintf(os.Stderr, "%s [opts] srcFileOrDir [...] [user]@server[:dstpath]\n", os.Args[0]) // nolint: errcheck
|
||||
fmt.Fprintf(os.Stderr, "%s [opts] [user]@server[:srcFileOrDir] dstPath\n", os.Args[0]) // nolint: errcheck
|
||||
flag.PrintDefaults()
|
||||
}
|
||||
|
||||
|
|
@ -600,25 +574,25 @@ func usageCp() {
|
|||
//
|
||||
// TODO: do this from the server side and have client just emit that
|
||||
func rejectUserMsg() string {
|
||||
return "Begone, thou " + spinsult.Get() + "!\r\n"
|
||||
return "Begone, " + spinsult.GetSentence() + "\r\n"
|
||||
}
|
||||
|
||||
// Transmit request to server for it to set up the remote end of a tunnel
|
||||
//
|
||||
// Server responds with [CSOTunAck:rport] or [CSOTunRefused:rport]
|
||||
// (handled in xsnet.Read())
|
||||
func reqTunnel(hc *xsnet.Conn, lp uint16 /*, p string*/ /*net.Addr*/, rp uint16) {
|
||||
func reqTunnel(hc *xsnet.Conn, lp uint16, p string /*net.Addr*/, rp uint16) {
|
||||
// Write request to server so it can attempt to set up its end
|
||||
var bTmp bytes.Buffer
|
||||
if e := binary.Write(&bTmp, binary.BigEndian, lp); e != nil {
|
||||
fmt.Fprintln(os.Stderr, "reqTunnel:", e)
|
||||
fmt.Fprintln(os.Stderr, "reqTunnel:", e) // nolint: errcheck
|
||||
}
|
||||
if e := binary.Write(&bTmp, binary.BigEndian, rp); e != nil {
|
||||
fmt.Fprintln(os.Stderr, "reqTunnel:", e)
|
||||
fmt.Fprintln(os.Stderr, "reqTunnel:", e) // nolint: errcheck
|
||||
}
|
||||
_ = logger.LogDebug(fmt.Sprintln("[Client sending CSOTunSetup]"))
|
||||
_ = logger.LogDebug(fmt.Sprintln("[Client sending CSOTunSetup]")) // nolint: gosec
|
||||
if n, e := hc.WritePacket(bTmp.Bytes(), xsnet.CSOTunSetup); e != nil || n != len(bTmp.Bytes()) {
|
||||
fmt.Fprintln(os.Stderr, "reqTunnel:", e)
|
||||
fmt.Fprintln(os.Stderr, "reqTunnel:", e) // nolint: errcheck
|
||||
}
|
||||
}
|
||||
|
||||
|
|
@ -626,18 +600,12 @@ func parseNonSwitchArgs(a []string) (user, host, path string, isDest bool, other
|
|||
// Whether fancyArg is src or dst file depends on flag.Args() index;
|
||||
// fancyArg as last flag.Args() element denotes dstFile
|
||||
// fancyArg as not-last flag.Args() element denotes srcFile
|
||||
|
||||
/* rlm:2025-12-10 This breaks if srcPath is outside of MSYS2 tree, as srcPath
|
||||
appears to silently be converted to an absolute winpath eg.,
|
||||
/c/users/RM/... -> C:/users/RM/...
|
||||
and the colon (:) in this breaks the logic below.
|
||||
*/
|
||||
var fancyUser, fancyHost, fancyPath string
|
||||
for i, arg := range a {
|
||||
if strings.Contains(arg, ":") || strings.Contains(arg, "@") {
|
||||
fancyArg := strings.Split(flag.Arg(i), "@")
|
||||
var fancyHostPath []string
|
||||
if len(fancyArg) < 2 { //nolint:gomnd
|
||||
if len(fancyArg) < 2 {
|
||||
//TODO: no user specified, use current
|
||||
fancyUser = "[default:getUser]"
|
||||
fancyHostPath = strings.Split(fancyArg[0], ":")
|
||||
|
|
@ -663,8 +631,8 @@ func parseNonSwitchArgs(a []string) (user, host, path string, isDest bool, other
|
|||
return fancyUser, fancyHost, fancyPath, isDest, otherArgs
|
||||
}
|
||||
|
||||
func launchTuns(conn *xsnet.Conn /*remoteHost string,*/, tuns string) {
|
||||
/*remAddrs, _ := net.LookupHost(remoteHost)*/ //nolint:gocritic,nolintlint
|
||||
func launchTuns(conn *xsnet.Conn, remoteHost string, tuns string) {
|
||||
remAddrs, _ := net.LookupHost(remoteHost) // nolint: gosec
|
||||
|
||||
if tuns == "" {
|
||||
return
|
||||
|
|
@ -673,8 +641,8 @@ func launchTuns(conn *xsnet.Conn /*remoteHost string,*/, tuns string) {
|
|||
tunSpecs := strings.Split(tuns, ",")
|
||||
for _, tunItem := range tunSpecs {
|
||||
var lPort, rPort uint16
|
||||
_, _ = fmt.Sscanf(tunItem, "%d:%d", &lPort, &rPort)
|
||||
reqTunnel(conn, lPort /*remAddrs[0],*/, rPort)
|
||||
_, _ = fmt.Sscanf(tunItem, "%d:%d", &lPort, &rPort) // nolint: gosec
|
||||
reqTunnel(conn, lPort, remAddrs[0], rPort)
|
||||
}
|
||||
}
|
||||
|
||||
|
|
@ -709,26 +677,25 @@ func sendSessionParams(conn io.Writer /* *xsnet.Conn*/, rec *xs.Session) (e erro
|
|||
}
|
||||
|
||||
// TODO: reduce gocyclo
|
||||
func main() { //nolint: funlen, gocyclo
|
||||
func main() {
|
||||
var (
|
||||
isInteractive bool
|
||||
vopt bool
|
||||
gopt bool // true: login via password, asking server to generate authToken
|
||||
dbg bool
|
||||
shellMode bool // true: act as shell, false: file copier
|
||||
cipherAlg string
|
||||
hmacAlg string
|
||||
kexAlg string
|
||||
server string
|
||||
port uint
|
||||
cmdStr string
|
||||
tunSpecStr string // lport1:rport1[,lport2:rport2,...]
|
||||
rekeySecs uint
|
||||
remodRequested bool // true: when rekeying, switch to random cipher/hmac alg
|
||||
copySrc []byte
|
||||
copyDst string
|
||||
copyQuiet bool
|
||||
copyLimitBPS uint
|
||||
isInteractive bool
|
||||
vopt bool
|
||||
gopt bool //login via password, asking server to generate authToken
|
||||
dbg bool
|
||||
shellMode bool // if true act as shell, else file copier
|
||||
cipherAlg string //cipher alg
|
||||
hmacAlg string //hmac alg
|
||||
kexAlg string //KEX/KEM alg
|
||||
server string
|
||||
port uint
|
||||
cmdStr string
|
||||
tunSpecStr string // lport1:rport1[,lport2:rport2,...]
|
||||
|
||||
copySrc []byte
|
||||
copyDst string
|
||||
copyQuiet bool
|
||||
copyLimitBPS uint
|
||||
|
||||
authCookie string
|
||||
chaffEnabled bool
|
||||
|
|
@ -739,49 +706,25 @@ func main() { //nolint: funlen, gocyclo
|
|||
op []byte
|
||||
)
|
||||
|
||||
// === Common (xs and xc) option parsing
|
||||
//=== Common (xs and xc) option parsing
|
||||
|
||||
flag.BoolVar(&vopt, "v", false, "show version")
|
||||
flag.BoolVar(&dbg, "d", false, "debug logging")
|
||||
flag.StringVar(&cipherAlg, "c", "C_AES_256", "session `cipher`"+`
|
||||
C_AES_256
|
||||
C_TWOFISH_128
|
||||
C_BLOWFISH_64
|
||||
C_CRYPTMT1
|
||||
C_HOPSCOTCH
|
||||
C_CHACHA20_12`)
|
||||
flag.StringVar(&hmacAlg, "m", "H_SHA256", "session `HMAC`"+`
|
||||
H_SHA256
|
||||
H_SHA512
|
||||
H_WHIRLPOOL`)
|
||||
flag.StringVar(&kexAlg, "k", "KEX_HERRADURA512", "KEx `alg`"+`
|
||||
KEX_HERRADURA256
|
||||
KEX_HERRADURA512
|
||||
KEX_HERRADURA1024
|
||||
KEX_HERRADURA2048
|
||||
KEX_KYBER512
|
||||
KEX_KYBER768
|
||||
KEX_KYBER1024
|
||||
KEX_NEWHOPE
|
||||
KEX_NEWHOPE_SIMPLE
|
||||
KEX_FRODOKEM_1344AES
|
||||
KEX_FRODOKEM_1344SHAKE
|
||||
KEX_FRODOKEM_976AES
|
||||
KEX_FRODOKEM_976SHAKE`)
|
||||
flag.StringVar(&kcpMode, "K", "unused", "KCP `alg`, one of [KCP_NONE | KCP_AES | KCP_BLOWFISH | KCP_CAST5 | KCP_SM4 | KCP_SALSA20 | KCP_SIMPLEXOR | KCP_TEA | KCP_3DES | KCP_TWOFISH | KCP_XTEA] to use KCP (github.com/xtaci/kcp-go) reliable UDP instead of TCP") //nolint:lll
|
||||
flag.UintVar(&port, "p", 2000, "``port") //nolint:gomnd,lll
|
||||
flag.UintVar(&rekeySecs, "r", 300, "rekey interval in `secs`")
|
||||
flag.BoolVar(&remodRequested, "R", false, "Borg Countermeasures (remodulate cipher/hmac alg on each rekey)")
|
||||
//nolint:gocritic,nolintlint // flag.StringVar(&authCookie, "a", "", "auth cookie")
|
||||
flag.StringVar(&cipherAlg, "c", "C_AES_256", "session `cipher` [C_AES_256 | C_TWOFISH_128 | C_BLOWFISH_64 | C_CRYPTMT1 | C_CHACHA20_12]")
|
||||
flag.StringVar(&hmacAlg, "m", "H_SHA256", "session `HMAC` [H_SHA256 | H_SHA512]")
|
||||
flag.StringVar(&kexAlg, "k", "KEX_HERRADURA512", "KEx `alg` [KEX_HERRADURA{256/512/1024/2048} | KEX_KYBER{512/768/1024} | KEX_NEWHOPE | KEX_NEWHOPE_SIMPLE | KEX_FRODOKEM_{1344|976}{AES|SHAKE}]")
|
||||
flag.StringVar(&kcpMode, "K", "unused", "KCP `alg`, one of [KCP_NONE | KCP_AES | KCP_BLOWFISH | KCP_CAST5 | KCP_SM4 | KCP_SALSA20 | KCP_SIMPLEXOR | KCP_TEA | KCP_3DES | KCP_TWOFISH | KCP_XTEA] to use KCP (github.com/xtaci/kcp-go) reliable UDP instead of TCP")
|
||||
flag.UintVar(&port, "p", 2000, "``port")
|
||||
//flag.StringVar(&authCookie, "a", "", "auth cookie")
|
||||
flag.BoolVar(&chaffEnabled, "e", true, "enable chaff pkts")
|
||||
flag.UintVar(&chaffFreqMin, "f", 100, "chaff pkt freq min `msecs`") //nolint:gomnd
|
||||
flag.UintVar(&chaffFreqMax, "F", 5000, "chaff pkt freq max `msecs`") //nolint:gomnd
|
||||
flag.UintVar(&chaffBytesMax, "B", 64, "chaff pkt size max `bytes`") //nolint:gomnd
|
||||
flag.UintVar(&chaffFreqMin, "f", 100, "chaff pkt freq min `msecs`")
|
||||
flag.UintVar(&chaffFreqMax, "F", 5000, "chaff pkt freq max `msecs`")
|
||||
flag.UintVar(&chaffBytesMax, "B", 64, "chaff pkt size max `bytes`")
|
||||
|
||||
flag.StringVar(&cpuprofile, "cpuprofile", "", "write cpu profile to <`file`>")
|
||||
flag.StringVar(&memprofile, "memprofile", "", "write memory profile to <`file`>")
|
||||
|
||||
// === xc vs. xs option parsing
|
||||
//=== xc vs. xs option parsing
|
||||
|
||||
// Find out what program we are (shell or copier)
|
||||
myPath := strings.Split(os.Args[0], string(os.PathSeparator))
|
||||
|
|
@ -798,7 +741,7 @@ func main() { //nolint: funlen, gocyclo
|
|||
flag.Usage = usageShell
|
||||
} else {
|
||||
flag.BoolVar(©Quiet, "q", false, "do not output progress bar during copy")
|
||||
flag.UintVar(©LimitBPS, "L", 8589934592, "copy max rate in bytes per sec") //nolint:gomnd
|
||||
flag.UintVar(©LimitBPS, "L", 8589934592, "copy max rate in bytes per sec")
|
||||
flag.Usage = usageCp
|
||||
}
|
||||
flag.Parse()
|
||||
|
|
@ -808,7 +751,7 @@ func main() { //nolint: funlen, gocyclo
|
|||
exitWithStatus(0)
|
||||
}
|
||||
|
||||
// === Profiling instrumentation
|
||||
//=== Profiling instrumentation
|
||||
|
||||
if cpuprofile != "" {
|
||||
f, err := os.Create(cpuprofile)
|
||||
|
|
@ -818,24 +761,24 @@ func main() { //nolint: funlen, gocyclo
|
|||
defer f.Close()
|
||||
fmt.Println("StartCPUProfile()")
|
||||
if err := pprof.StartCPUProfile(f); err != nil {
|
||||
log.Fatal("could not start CPU profile: ", err) //nolint:gocritic
|
||||
log.Fatal("could not start CPU profile: ", err)
|
||||
} else {
|
||||
defer pprof.StopCPUProfile()
|
||||
}
|
||||
|
||||
go func() { http.ListenAndServe("localhost:6060", nil) }() //nolint:errcheck,gosec
|
||||
go func() { http.ListenAndServe("localhost:6060", nil) }()
|
||||
}
|
||||
|
||||
// === User, host, port and path args for file operations, if applicable
|
||||
//=== User, host, port and path args for file operations, if applicable
|
||||
|
||||
remoteUser, remoteHost, tmpPath, pathIsDest, otherArgs :=
|
||||
parseNonSwitchArgs(flag.Args())
|
||||
//nolint:gocritic,nolintlint // fmt.Println("otherArgs:", otherArgs)
|
||||
//fmt.Println("otherArgs:", otherArgs)
|
||||
|
||||
// Set defaults if user doesn't specify user, path or port
|
||||
var uname string
|
||||
if remoteUser == "" {
|
||||
u, _ := user.Current()
|
||||
u, _ := user.Current() // nolint: gosec
|
||||
uname = localUserName(u)
|
||||
} else {
|
||||
uname = remoteUser
|
||||
|
|
@ -848,7 +791,7 @@ func main() { //nolint: funlen, gocyclo
|
|||
tmpPath = "."
|
||||
}
|
||||
|
||||
// === Copy mode arg and copy src/dest setup
|
||||
//=== Copy mode arg and copy src/dest setup
|
||||
|
||||
var fileArgs string
|
||||
if !shellMode /*&& tmpPath != ""*/ {
|
||||
|
|
@ -881,15 +824,15 @@ func main() { //nolint: funlen, gocyclo
|
|||
}
|
||||
}
|
||||
|
||||
// === Do some final option consistency checks
|
||||
//=== Do some final option consistency checks
|
||||
|
||||
//nolint:gocritic,nolintlint // fmt.Println("server finally is:", server)
|
||||
//fmt.Println("server finally is:", server)
|
||||
if flag.NFlag() == 0 && server == "" {
|
||||
flag.Usage()
|
||||
exitWithStatus(0)
|
||||
}
|
||||
|
||||
if cmdStr != "" && (len(copySrc) != 0 || copyDst != "") {
|
||||
if len(cmdStr) != 0 && (len(copySrc) != 0 || len(copyDst) != 0) {
|
||||
log.Fatal("incompatible options -- either cmd (-x) or copy ops but not both")
|
||||
}
|
||||
|
||||
|
|
@ -897,44 +840,39 @@ func main() { //nolint: funlen, gocyclo
|
|||
// either the shell session or copy operation.
|
||||
_ = shellMode
|
||||
|
||||
Log, _ = logger.New(logger.LOG_USER|logger.LOG_DEBUG|logger.LOG_NOTICE|logger.LOG_ERR, "xs")
|
||||
Log, _ = logger.New(logger.LOG_USER|logger.LOG_DEBUG|logger.LOG_NOTICE|logger.LOG_ERR, "xs") // nolint: errcheck,gosec
|
||||
xsnet.Init(dbg, "xs", logger.LOG_USER|logger.LOG_DEBUG|logger.LOG_NOTICE|logger.LOG_ERR)
|
||||
if dbg {
|
||||
log.SetOutput(Log)
|
||||
} else {
|
||||
log.SetOutput(io.Discard)
|
||||
log.SetOutput(ioutil.Discard)
|
||||
}
|
||||
|
||||
// === Auth token fetch for login
|
||||
//=== Auth token fetch for login
|
||||
|
||||
if !gopt {
|
||||
// See if we can log in via an auth token
|
||||
u, _ := user.Current()
|
||||
ab, aerr := os.ReadFile(fmt.Sprintf("%s/%s", u.HomeDir, xsnet.XS_ID_AUTHTOKFILE))
|
||||
u, _ := user.Current() // nolint: gosec
|
||||
ab, aerr := ioutil.ReadFile(fmt.Sprintf("%s/.xs_id", u.HomeDir))
|
||||
if aerr == nil {
|
||||
for _, line := range strings.Split(string(ab), "\n") {
|
||||
line += "\n"
|
||||
idx := strings.Index(line, remoteHost+":"+uname)
|
||||
if idx >= 0 {
|
||||
line = line[idx:]
|
||||
entries := strings.SplitN(line, "\n", -1)
|
||||
authCookie = strings.TrimSpace(entries[0])
|
||||
// Security scrub
|
||||
line = ""
|
||||
break
|
||||
}
|
||||
}
|
||||
if authCookie == "" {
|
||||
idx := strings.Index(string(ab), remoteHost)
|
||||
if idx >= 0 {
|
||||
ab = ab[idx:]
|
||||
entries := strings.SplitN(string(ab), "\n", -1)
|
||||
authCookie = strings.TrimSpace(entries[0])
|
||||
// Security scrub
|
||||
ab = nil
|
||||
runtime.GC()
|
||||
} else {
|
||||
_, _ = fmt.Fprintln(os.Stderr, "[no authtoken, use -g to request one from server]")
|
||||
}
|
||||
} else {
|
||||
log.Printf("[cannot read %s/%s]\n", u.HomeDir, xsnet.XS_ID_AUTHTOKFILE)
|
||||
log.Printf("[cannot read %s/.xs_id]\n", u.HomeDir)
|
||||
}
|
||||
}
|
||||
runtime.GC()
|
||||
|
||||
// === Enforce some sane min/max vals on chaff flags
|
||||
if chaffFreqMin < 2 { //nolint:gomnd
|
||||
//=== Enforce some sane min/max vals on chaff flags
|
||||
if chaffFreqMin < 2 {
|
||||
chaffFreqMin = 2
|
||||
}
|
||||
if chaffFreqMax == 0 {
|
||||
|
|
@ -944,17 +882,17 @@ func main() { //nolint: funlen, gocyclo
|
|||
chaffBytesMax = 64
|
||||
}
|
||||
|
||||
// === Shell vs. Copy mode chaff and cmd setup
|
||||
//=== Shell vs. Copy mode chaff and cmd setup
|
||||
|
||||
if shellMode {
|
||||
// We must make the decision about interactivity before Dial()
|
||||
// as it affects chaffing behaviour. 20180805
|
||||
if gopt {
|
||||
fmt.Fprintln(os.Stderr, "[requesting authtoken from server]")
|
||||
fmt.Fprintln(os.Stderr, "[requesting authtoken from server]") // nolint: errcheck
|
||||
op = []byte{'A'}
|
||||
chaffFreqMin = 2
|
||||
chaffFreqMax = 10
|
||||
} else if cmdStr == "" {
|
||||
} else if len(cmdStr) == 0 {
|
||||
op = []byte{'s'}
|
||||
isInteractive = true
|
||||
} else {
|
||||
|
|
@ -975,86 +913,42 @@ func main() { //nolint: funlen, gocyclo
|
|||
// client->server file copy
|
||||
// src file list is in copySrc
|
||||
op = []byte{'D'}
|
||||
//nolint:gocritic,nolintlint // fmt.Println("client->server copy:", string(copySrc), "->", copyDst)
|
||||
//fmt.Println("client->server copy:", string(copySrc), "->", copyDst)
|
||||
cmdStr = copyDst
|
||||
} else {
|
||||
// server->client file copy
|
||||
// remote src file(s) in copyDsr
|
||||
op = []byte{'S'}
|
||||
//nolint:gocritic,nolintlint // fmt.Println("server->client copy:", string(copySrc), "->", copyDst)
|
||||
//fmt.Println("server->client copy:", string(copySrc), "->", copyDst)
|
||||
cmdStr = string(copySrc)
|
||||
}
|
||||
}
|
||||
|
||||
// === TCP / KCP Dial setup
|
||||
//=== TCP / KCP Dial setup
|
||||
|
||||
proto := "tcp"
|
||||
if kcpMode != "unused" {
|
||||
proto = "kcp"
|
||||
}
|
||||
|
||||
remodExtArg := ""
|
||||
if remodRequested {
|
||||
remodExtArg = "OPT_REMOD"
|
||||
}
|
||||
// Pass opt to Dial() via extensions arg
|
||||
conn, err := xsnet.Dial(proto, server, cipherAlg, hmacAlg, kexAlg, kcpMode, remodExtArg)
|
||||
conn, err := xsnet.Dial(proto, server, cipherAlg, hmacAlg, kexAlg, kcpMode)
|
||||
if err != nil {
|
||||
fmt.Println(err)
|
||||
exitWithStatus(XSNetDialFailed)
|
||||
exitWithStatus(3)
|
||||
}
|
||||
|
||||
conn.RekeyHelper(rekeySecs)
|
||||
defer conn.ShutdownRekey()
|
||||
|
||||
// === Shell terminal mode (Shell vs. Copy) setup
|
||||
|
||||
defer conn.Close()
|
||||
|
||||
// === From this point on, conn is a secure encrypted channel
|
||||
|
||||
// === BEGIN Login phase
|
||||
//=== Shell terminal mode (Shell vs. Copy) setup
|
||||
|
||||
// Set stdin in raw mode if it's an interactive session
|
||||
// TODO: send flag to server side indicating this
|
||||
// affects shell command used
|
||||
var oldState *xs.State
|
||||
defer conn.Close() // nolint: errcheck
|
||||
|
||||
// Start login timeout here and disconnect if user/pass phase stalls
|
||||
// iloginImpatience := time.AfterFunc(20*time.Second, func() {
|
||||
// i fmt.Printf(" .. [you still there? Waiting for a password.]")
|
||||
// i})
|
||||
loginTimeout := time.AfterFunc(30*time.Second, func() { //nolint:gomnd
|
||||
restoreTermState(oldState)
|
||||
fmt.Printf(" .. [login timeout]\n")
|
||||
exitWithStatus(xsnet.CSELoginTimeout)
|
||||
})
|
||||
|
||||
if authCookie == "" {
|
||||
if !gopt {
|
||||
// No auth token, prompt for password
|
||||
fmt.Printf("Gimme cookie:")
|
||||
}
|
||||
ab, e := xs.ReadPassword(os.Stdin)
|
||||
if !gopt {
|
||||
fmt.Printf("\r\n")
|
||||
}
|
||||
if e != nil {
|
||||
panic(e)
|
||||
}
|
||||
authCookie = string(ab)
|
||||
}
|
||||
|
||||
//nolint:gocritic,nolintlint // i_ = loginImpatience.Stop()
|
||||
_ = loginTimeout.Stop()
|
||||
// Security scrub
|
||||
runtime.GC()
|
||||
|
||||
// === END Login phase
|
||||
|
||||
// === Terminal mode adjustment for session
|
||||
//=== From this point on, conn is a secure encrypted channel
|
||||
|
||||
if shellMode {
|
||||
if isatty.IsTerminal(os.Stdin.Fd()) ||
|
||||
isatty.IsCygwinTerminal(os.Stdin.Fd()) {
|
||||
oldState, err = xs.MakeRaw(os.Stdin)
|
||||
if isatty.IsTerminal(os.Stdin.Fd()) {
|
||||
oldState, err = xs.MakeRaw(os.Stdin.Fd())
|
||||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
|
@ -1066,83 +960,108 @@ func main() { //nolint: funlen, gocyclo
|
|||
}
|
||||
}
|
||||
|
||||
// === Session param and TERM setup
|
||||
//=== Login phase
|
||||
|
||||
// Start login timeout here and disconnect if user/pass phase stalls
|
||||
//iloginImpatience := time.AfterFunc(20*time.Second, func() {
|
||||
//i fmt.Printf(" .. [you still there? Waiting for a password.]")
|
||||
//i})
|
||||
loginTimeout := time.AfterFunc(30*time.Second, func() {
|
||||
restoreTermState(oldState)
|
||||
fmt.Printf(" .. [login timeout]\n")
|
||||
exitWithStatus(xsnet.CSOLoginTimeout)
|
||||
})
|
||||
|
||||
if len(authCookie) == 0 {
|
||||
//No auth token, prompt for password
|
||||
fmt.Printf("Gimme cookie:")
|
||||
ab, e := xs.ReadPassword(os.Stdin.Fd())
|
||||
fmt.Printf("\r\n")
|
||||
if e != nil {
|
||||
panic(e)
|
||||
}
|
||||
authCookie = string(ab)
|
||||
}
|
||||
|
||||
//i_ = loginImpatience.Stop()
|
||||
_ = loginTimeout.Stop()
|
||||
// Security scrub
|
||||
runtime.GC()
|
||||
|
||||
//=== Session param and TERM setup
|
||||
|
||||
// Set up session params and send over to server
|
||||
rec := xs.NewSession(op, []byte(uname), []byte(remoteHost), []byte(os.Getenv("TERM")), []byte(cmdStr), []byte(authCookie), 0)
|
||||
sendErr := sendSessionParams(&conn, rec)
|
||||
if sendErr != nil {
|
||||
restoreTermState(oldState)
|
||||
rec.SetStatus(ServerRejectedSecureProposal)
|
||||
fmt.Fprintln(os.Stderr, "Error: server rejected secure proposal params or login timed out")
|
||||
rec.SetStatus(254)
|
||||
fmt.Fprintln(os.Stderr, "Error: server rejected secure proposal params or login timed out") // nolint: errcheck
|
||||
exitWithStatus(int(rec.Status()))
|
||||
//nolint:gocritic,nolintlint // log.Fatal(sendErr)
|
||||
//log.Fatal(sendErr)
|
||||
}
|
||||
|
||||
// Security scrub
|
||||
authCookie = "" //nolint: ineffassign
|
||||
//Security scrub
|
||||
authCookie = "" // nolint: ineffassign
|
||||
runtime.GC()
|
||||
|
||||
// === Login Auth
|
||||
//=== Login Auth
|
||||
|
||||
// === Read auth reply from server
|
||||
//=== Read auth reply from server
|
||||
authReply := make([]byte, 1) // bool: 0 = fail, 1 = pass
|
||||
_, err = conn.Read(authReply)
|
||||
if err != nil {
|
||||
// === Exit if auth reply not received
|
||||
fmt.Fprintln(os.Stderr, "Error reading auth reply")
|
||||
rec.SetStatus(ErrReadingAuthReply)
|
||||
//=== Exit if auth reply not received
|
||||
fmt.Fprintln(os.Stderr, "Error reading auth reply") // nolint: errcheck
|
||||
rec.SetStatus(255)
|
||||
} else if authReply[0] == 0 {
|
||||
// === .. or if auth failed
|
||||
fmt.Fprintln(os.Stderr, rejectUserMsg())
|
||||
rec.SetStatus(GeneralProtocolErr)
|
||||
//=== .. or if auth failed
|
||||
fmt.Fprintln(os.Stderr, rejectUserMsg()) // nolint: errcheck
|
||||
rec.SetStatus(255)
|
||||
} else {
|
||||
// === Set up chaffing to server
|
||||
//=== Set up chaffing to server
|
||||
conn.SetupChaff(chaffFreqMin, chaffFreqMax, chaffBytesMax) // enable client->server chaffing
|
||||
if chaffEnabled {
|
||||
// #gv:s/label=\"main\$2\"/label=\"deferCloseChaff\"/
|
||||
// TODO:.gv:main:2:deferCloseChaff
|
||||
conn.StartupChaff() // goroutine, returns immediately
|
||||
conn.EnableChaff() // goroutine, returns immediately
|
||||
defer conn.DisableChaff()
|
||||
defer conn.ShutdownChaff()
|
||||
}
|
||||
|
||||
// === (goroutine) Start keepAliveWorker for tunnels
|
||||
//=== (goroutine) Start keepAliveWorker for tunnels
|
||||
// #gv:s/label=\"main\$1\"/label=\"tunKeepAlive\"/
|
||||
// TODO:.gv:main:1:tunKeepAlive
|
||||
// [1]: better to always send tunnel keepAlives even if client didn't specify
|
||||
// any, to prevent listeners from knowing this.
|
||||
// [1] if tunSpecStr != "" {
|
||||
//[1]: better to always send tunnel keepAlives even if client didn't specify
|
||||
// any, to prevent listeners from knowing this.
|
||||
//[1] if tunSpecStr != "" {
|
||||
keepAliveWorker := func() {
|
||||
for {
|
||||
// Add a bit of jitter to keepAlive so it doesn't stand out quite as much
|
||||
time.Sleep(time.Duration(2000-rand.Intn(200)) * time.Millisecond) //nolint:gosec,gomnd
|
||||
time.Sleep(time.Duration(2000-rand.Intn(200)) * time.Millisecond)
|
||||
// FIXME: keepAlives should probably have small random packet len/data as well
|
||||
// to further obscure them vs. interactive or tunnel data
|
||||
// keepAlives must be >=2 bytes, due to processing elsewhere
|
||||
conn.WritePacket([]byte{0, 0}, xsnet.CSOTunKeepAlive) //nolint: errcheck
|
||||
conn.WritePacket([]byte{0, 0}, xsnet.CSOTunKeepAlive) // nolint: errcheck,gosec
|
||||
}
|
||||
}
|
||||
go keepAliveWorker()
|
||||
// [1]}
|
||||
//[1]}
|
||||
|
||||
// === Session entry (shellMode or copyMode)
|
||||
//=== Session entry (shellMode or copyMode)
|
||||
if shellMode {
|
||||
// === Set up connection keepalive to server
|
||||
conn.StartupKeepAlive() // goroutine, returns immediately
|
||||
defer conn.ShutdownKeepAlive()
|
||||
|
||||
// === (shell) launch tunnels
|
||||
launchTuns(&conn /*remoteHost,*/, tunSpecStr)
|
||||
//=== (shell) launch tunnels
|
||||
launchTuns(&conn, remoteHost, tunSpecStr)
|
||||
doShellMode(isInteractive, &conn, oldState, rec)
|
||||
} else {
|
||||
// === (.. or file copy)
|
||||
s, _ := doCopyMode(&conn, pathIsDest, fileArgs, copyQuiet, copyLimitBPS, rec)
|
||||
//=== (.. or file copy)
|
||||
s, _ := doCopyMode(&conn, pathIsDest, fileArgs, copyQuiet, copyLimitBPS, rec) // nolint: errcheck,gosec
|
||||
rec.SetStatus(s)
|
||||
}
|
||||
|
||||
if rec.Status() != 0 {
|
||||
restoreTermState(oldState)
|
||||
fmt.Fprintln(os.Stderr, "Session exited with status:", rec.Status())
|
||||
fmt.Fprintln(os.Stderr, "Session exited with status:", rec.Status()) // nolint: errcheck
|
||||
}
|
||||
}
|
||||
|
||||
|
|
@ -1151,7 +1070,7 @@ func main() { //nolint: funlen, gocyclo
|
|||
oldState = nil
|
||||
}
|
||||
|
||||
// === Exit
|
||||
//=== Exit
|
||||
exitWithStatus(int(rec.Status()))
|
||||
}
|
||||
|
||||
|
|
@ -1169,7 +1088,7 @@ func localUserName(u *user.User) string {
|
|||
}
|
||||
|
||||
func restoreTermState(oldState *xs.State) {
|
||||
_ = xs.Restore(os.Stdin, oldState)
|
||||
_ = xs.Restore(os.Stdin.Fd(), oldState) // nolint: errcheck,gosec
|
||||
}
|
||||
|
||||
// exitWithStatus wraps os.Exit() plus does any required pprof housekeeping
|
||||
|
|
@ -1186,8 +1105,9 @@ func exitWithStatus(status int) {
|
|||
defer f.Close()
|
||||
runtime.GC() // get up-to-date statistics
|
||||
if err := pprof.WriteHeapProfile(f); err != nil {
|
||||
log.Fatal("could not write memory profile: ", err) //nolint:gocritic
|
||||
log.Fatal("could not write memory profile: ", err)
|
||||
}
|
||||
}
|
||||
|
||||
os.Exit(status)
|
||||
}
|
||||
|
|
|
|||
|
|
@ -6,9 +6,7 @@ XSD_USER=root
|
|||
XSD_HOME=/var/run
|
||||
INST_PREFIX=/usr/local
|
||||
COMMAND=$INST_PREFIX/sbin/xsd
|
||||
#ARGS="-L -aK KEX_all -aC C_all -aH H_all"
|
||||
echo "SET ARGS in this script to define allow KEX, cipher and hmac algs"
|
||||
exit 1
|
||||
ARGS="-L"
|
||||
|
||||
depend() {
|
||||
need net
|
||||
|
|
@ -30,7 +28,7 @@ start() {
|
|||
-d ${XSD_HOME} \
|
||||
--make-pidfile --pidfile ${XSD_PIDFILE} \
|
||||
--start --quiet --background \
|
||||
--exec "${COMMAND}" -- ${ARGS}
|
||||
--exec "${COMMAND}" -- "${ARGS}"
|
||||
eend $?
|
||||
}
|
||||
|
||||
|
|
|
|||
|
|
@ -11,10 +11,6 @@
|
|||
|
||||
set -e
|
||||
|
||||
echo "SET XSD_OPTS in this script to define allow KEX, cipher and hmac algs"
|
||||
#XSD_OPTS="-L -aK KEX_all -aC C_all -aH H_all"
|
||||
exit 1
|
||||
|
||||
# /etc/init.d/xsd: start and stop the eXperimental "secure" Shell Daemon
|
||||
|
||||
test -x /usr/local/sbin/xsd || exit 0
|
||||
|
|
|
|||
|
|
@ -1,16 +1,10 @@
|
|||
.PHONY: clean all vis lint
|
||||
|
||||
ifeq ($(GARBLE),y)
|
||||
GO = garble -literals -tiny -debugdir=garbled
|
||||
else
|
||||
GO = go
|
||||
endif
|
||||
|
||||
EXTPKGS = binary,bytes,crypto,encoding,errors,flag,fmt,internal,io,log,net,os,path,runtime,time,strings,sync,syscall
|
||||
EXE = $(notdir $(shell pwd))
|
||||
|
||||
all:
|
||||
$(GO) build $(BUILDOPTS) .
|
||||
go build $(BUILDOPTS) .
|
||||
|
||||
clean:
|
||||
$(RM) $(EXE) $(EXE).exe
|
||||
|
|
|
|||
Binary file not shown.
|
Before Width: | Height: | Size: 1.1 MiB After Width: | Height: | Size: 782 KiB |
583
xsd/xsd-vis.gv
583
xsd/xsd-vis.gv
File diff suppressed because one or more lines are too long
775
xsd/xsd.go
775
xsd/xsd.go
File diff suppressed because it is too large
Load Diff
|
|
@ -1,18 +1,12 @@
|
|||
.PHONY: info clean lib
|
||||
|
||||
ifeq ($(GARBLE),y)
|
||||
GO = garble -tiny -literals -debugdir=garbled
|
||||
else
|
||||
GO = go
|
||||
endif
|
||||
|
||||
all: lib
|
||||
|
||||
clean:
|
||||
go clean .
|
||||
|
||||
lib: info
|
||||
$(GO) install .
|
||||
go install .
|
||||
|
||||
ifneq ($(MSYSTEM),)
|
||||
info:
|
||||
|
|
|
|||
|
|
@ -21,9 +21,7 @@ import (
|
|||
"log"
|
||||
|
||||
"blitter.com/go/cryptmt"
|
||||
"blitter.com/go/hopscotch"
|
||||
"github.com/aead/chacha20/chacha"
|
||||
whirlpool "github.com/jzelinskie/whirlpool"
|
||||
"golang.org/x/crypto/blowfish"
|
||||
"golang.org/x/crypto/twofish"
|
||||
|
||||
|
|
@ -58,18 +56,9 @@ func expandKeyMat(keymat []byte, blocksize int) []byte {
|
|||
return keymat
|
||||
}
|
||||
|
||||
// Choose a cipher and hmac alg from supported sets, given two uint8 values
|
||||
func getNewStreamAlgs(cb uint8, hb uint8) (config uint32) {
|
||||
// Get new cipher and hash algs (clamped to valid values) based on
|
||||
// the input rekeying data
|
||||
c := (cb % CAlgNoneDisallowed)
|
||||
h := (hb % HmacNoneDisallowed)
|
||||
config = uint32(h)<<8 | uint32(c)
|
||||
return
|
||||
}
|
||||
|
||||
// (Re-)initialize the keystream and hmac state for an xsnet.Conn, returning
|
||||
// a cipherStream and hash
|
||||
/* Support functionality to set up encryption after a channel has
|
||||
been negotiated via xsnet.go
|
||||
*/
|
||||
func (hc *Conn) getStream(keymat []byte) (rc cipher.Stream, mc hash.Hash, err error) {
|
||||
var key []byte
|
||||
var block cipher.Block
|
||||
|
|
@ -115,12 +104,7 @@ func (hc *Conn) getStream(keymat []byte) (rc cipher.Stream, mc hash.Hash, err er
|
|||
log.Printf("[cipher BLOWFISH_64 (%d)]\n", copts)
|
||||
case CAlgCryptMT1:
|
||||
rc = cryptmt.New(nil, nil, keymat)
|
||||
//NOTE: this alg is not based on block cipher, no IV
|
||||
log.Printf("[cipher CRYPTMT1 (%d)]\n", copts)
|
||||
case CAlgHopscotch:
|
||||
rc = hopscotch.New(nil, nil, 4, keymat)
|
||||
//NOTE: this alg is not based on block cipher, no IV
|
||||
log.Printf("[cipher HOPSCOTCH (%d)]\n", copts)
|
||||
case CAlgChaCha20_12:
|
||||
keymat = expandKeyMat(keymat, chacha.KeySize)
|
||||
key = keymat[0:chacha.KeySize]
|
||||
|
|
@ -156,9 +140,6 @@ func (hc *Conn) getStream(keymat []byte) (rc cipher.Stream, mc hash.Hash, err er
|
|||
if !halg.Available() {
|
||||
log.Fatal("hash not available!")
|
||||
}
|
||||
case HmacWHIRLPOOL:
|
||||
log.Printf("[hash HmacWHIRLPOOL (%d)]\n", hopts)
|
||||
mc = whirlpool.New()
|
||||
default:
|
||||
log.Printf("[invalid hmac (%d)]\n", hopts)
|
||||
fmt.Printf("DOOFUS SET A VALID HMAC ALG (%d)\n", hopts)
|
||||
|
|
@ -167,7 +148,7 @@ func (hc *Conn) getStream(keymat []byte) (rc cipher.Stream, mc hash.Hash, err er
|
|||
//os.Exit(1)
|
||||
}
|
||||
|
||||
if err == nil && ivlen > 0 {
|
||||
if err != nil {
|
||||
// Feed the IV into the hmac: all traffic in the connection must
|
||||
// feed its data into the hmac afterwards, so both ends can xor
|
||||
// that with the stream to detect corruption.
|
||||
|
|
|
|||
|
|
@ -52,8 +52,6 @@ const (
|
|||
CSEKEXAlgDenied // server rejected proposed KEX alg
|
||||
CSECipherAlgDenied // server rejected proposed Cipher alg
|
||||
CSEHMACAlgDenied // server rejected proposed HMAC alg
|
||||
CSEConnDead // connection keepalives expired
|
||||
CSELoginTimeout
|
||||
)
|
||||
|
||||
// Extended (>255 UNIX exit status) codes
|
||||
|
|
@ -69,6 +67,9 @@ const (
|
|||
CSOExitStatus // Remote cmd exit status
|
||||
CSOChaff // Dummy packet, do not pass beyond decryption
|
||||
|
||||
// Client side errors
|
||||
CSOLoginTimeout
|
||||
|
||||
// Tunnel setup/control/status
|
||||
CSOTunSetup // client -> server tunnel setup request (dstport)
|
||||
CSOTunSetupAck // server -> client tunnel setup ack
|
||||
|
|
@ -77,8 +78,6 @@ const (
|
|||
CSOTunKeepAlive // client tunnel heartbeat
|
||||
CSOTunDisconn // server -> client: tunnel rport disconnected
|
||||
CSOTunHangup // client -> server: tunnel lport hung up
|
||||
CSOKeepAlive // bidir keepalive packet to monitor main connection
|
||||
CSORekey // TODO: rekey/re-select session cipher/hash algs
|
||||
)
|
||||
|
||||
// TunEndpoint.tunCtl control values - used to control workers for client
|
||||
|
|
@ -98,7 +97,7 @@ const (
|
|||
// Channel status Op byte type (see CSONone, ... and CSENone, ...)
|
||||
type CSOType uint32
|
||||
|
||||
// TODO: this should be small (max unfragmented packet size?)
|
||||
//TODO: this should be small (max unfragmented packet size?)
|
||||
const MAX_PAYLOAD_LEN = 2*1024*1024*1024 - 1
|
||||
|
||||
// Session symmetric crypto algs
|
||||
|
|
@ -108,7 +107,6 @@ const (
|
|||
CAlgBlowfish64 // golang.org/x/crypto/blowfish
|
||||
CAlgCryptMT1 //cryptmt using mtwist64
|
||||
CAlgChaCha20_12
|
||||
CAlgHopscotch
|
||||
CAlgNoneDisallowed
|
||||
)
|
||||
|
||||
|
|
@ -119,27 +117,8 @@ type CSCipherAlg uint32
|
|||
const (
|
||||
HmacSHA256 = iota
|
||||
HmacSHA512
|
||||
HmacWHIRLPOOL
|
||||
HmacNoneDisallowed
|
||||
)
|
||||
|
||||
// Conn opts outside of basic kex/cipher/hmac connect config
|
||||
const (
|
||||
CONone = iota
|
||||
CORemodulateShields // if set, rekeying also reselects random cipher/hmac alg
|
||||
)
|
||||
|
||||
type COValue uint32
|
||||
|
||||
// Available HMACs for hkex.Conn
|
||||
type CSHmacAlg uint32
|
||||
|
||||
// Some bounds-checking consts
|
||||
const (
|
||||
REKEY_SECS_MIN = 1
|
||||
REKEY_SECS_MAX = 28800 // 8 hours
|
||||
CHAFF_FREQ_MSECS_MIN = 1
|
||||
CHAFF_FREQ_MSECS_MAX = 300000 // 5 minutes
|
||||
)
|
||||
|
||||
const XS_ID_AUTHTOKFILE = ".config/xs/.xs_id"
|
||||
|
|
|
|||
|
|
@ -9,7 +9,7 @@
|
|||
|
||||
package xsnet
|
||||
|
||||
// Implementation of key-exchange-wrapped versions of the golang standard
|
||||
// Implementation of HKEx-wrapped versions of the golang standard
|
||||
// net package interfaces, allowing clients and servers to simply replace
|
||||
// 'net.Dial' and 'net.Listen' with 'hkex.Dial' and 'hkex.Listen'
|
||||
// (though some extra methods are implemented and must be used
|
||||
|
|
@ -25,7 +25,6 @@ package xsnet
|
|||
import (
|
||||
"bytes"
|
||||
"crypto/cipher"
|
||||
crand "crypto/rand"
|
||||
"encoding/binary"
|
||||
"encoding/hex"
|
||||
"errors"
|
||||
|
|
@ -64,6 +63,7 @@ type (
|
|||
// see: https://en.wikipedia.org/wiki/chaff_(countermeasure)
|
||||
ChaffConfig struct {
|
||||
shutdown bool //set to inform chaffHelper to shut down
|
||||
enabled bool
|
||||
msecsMin uint //msecs min interval
|
||||
msecsMax uint //msecs max interval
|
||||
szMax uint // max size in bytes
|
||||
|
|
@ -86,11 +86,8 @@ type (
|
|||
Rows uint16
|
||||
Cols uint16
|
||||
|
||||
keepalive uint // if this reaches zero, conn is considered dead
|
||||
rekey uint // if nonzero, rekeying interval in seconds
|
||||
Pproc int // proc ID of command run on this conn
|
||||
chaff ChaffConfig
|
||||
tuns *map[uint16](*TunEndpoint)
|
||||
chaff ChaffConfig
|
||||
tuns *map[uint16](*TunEndpoint)
|
||||
|
||||
closeStat *CSOType // close status (CSOExitStatus)
|
||||
r cipher.Stream //read cipherStream
|
||||
|
|
@ -157,8 +154,6 @@ func (c *CSCipherAlg) String() string {
|
|||
return "C_BLOWFISH_64"
|
||||
case CAlgCryptMT1:
|
||||
return "C_CRYPTMT1"
|
||||
case CAlgHopscotch:
|
||||
return "C_HOPSCOTCH"
|
||||
case CAlgChaCha20_12:
|
||||
return "C_CHACHA20_12"
|
||||
default:
|
||||
|
|
@ -171,13 +166,11 @@ func (hc *Conn) HAlg() CSHmacAlg {
|
|||
}
|
||||
|
||||
func (h *CSHmacAlg) String() string {
|
||||
switch *h & 0x0FF {
|
||||
switch (*h >> 8) & 0x0FF {
|
||||
case HmacSHA256:
|
||||
return "H_SHA256"
|
||||
case HmacSHA512:
|
||||
return "H_SHA512"
|
||||
case HmacWHIRLPOOL:
|
||||
return "H_WHIRLPOOL"
|
||||
return "C_SHA512"
|
||||
default:
|
||||
return "H_ERR_UNK"
|
||||
}
|
||||
|
|
@ -242,7 +235,7 @@ func (hc *Conn) SetConnOpts(copts uint32) {
|
|||
//
|
||||
// Consumers of this lib may use this for protocol-level options not part
|
||||
// of the KEx or encryption info used by the connection.
|
||||
func (hc *Conn) Opts() uint32 {
|
||||
func (hc Conn) Opts() uint32 {
|
||||
return hc.opts
|
||||
}
|
||||
|
||||
|
|
@ -271,6 +264,8 @@ func _new(kexAlg KEXAlg, conn *net.Conn) (hc *Conn, e error) {
|
|||
tempMap := make(map[uint16]*TunEndpoint)
|
||||
hc.tuns = &tempMap
|
||||
|
||||
*hc.closeStat = CSEStillOpen // open or prematurely-closed status
|
||||
|
||||
// Set up KEx/KEM-specifics
|
||||
switch kexAlg {
|
||||
case KEX_HERRADURA256:
|
||||
|
|
@ -298,7 +293,7 @@ func _new(kexAlg KEXAlg, conn *net.Conn) (hc *Conn, e error) {
|
|||
case KEX_FRODOKEM_976AES:
|
||||
fallthrough
|
||||
case KEX_FRODOKEM_976SHAKE:
|
||||
//log.Printf("[KEx alg %d is valid]\n", kexAlg)
|
||||
log.Printf("[KEx alg %d accepted]\n", kexAlg)
|
||||
default:
|
||||
// UNREACHABLE: _getkexalgnum() guarantees a valid KEX value
|
||||
hc.kex = KEX_HERRADURA512
|
||||
|
|
@ -312,9 +307,9 @@ func _new(kexAlg KEXAlg, conn *net.Conn) (hc *Conn, e error) {
|
|||
// applyConnExtensions processes optional Dial() negotiation
|
||||
// parameters. See also getkexalgnum().
|
||||
//
|
||||
// # Currently defined extension values
|
||||
// Currently defined extension values
|
||||
//
|
||||
// # KEx algs
|
||||
// KEx algs
|
||||
//
|
||||
// KEX_HERRADURA256 KEX_HERRADURA512 KEX_HERRADURA1024 KEX_HERRADURA2048
|
||||
//
|
||||
|
|
@ -322,11 +317,11 @@ func _new(kexAlg KEXAlg, conn *net.Conn) (hc *Conn, e error) {
|
|||
//
|
||||
// KEX_NEWHOPE KEX_NEWHOPE_SIMPLE
|
||||
//
|
||||
// # Session (symmetric) crypto
|
||||
// Session (symmetric) crypto
|
||||
//
|
||||
// C_AES_256 C_TWOFISH_128 C_BLOWFISH_128 C_CRYPTMT1 C_CHACHA20_12 C_HOPSCOTCH
|
||||
// C_AES_256 C_TWOFISH_128 C_BLOWFISH_128 C_CRYPTMT1 C_CHACHA20_12
|
||||
//
|
||||
// # Session HMACs
|
||||
// Session HMACs
|
||||
//
|
||||
// H_SHA256 H_SHA512
|
||||
func (hc *Conn) applyConnExtensions(extensions ...string) {
|
||||
|
|
@ -348,10 +343,6 @@ func (hc *Conn) applyConnExtensions(extensions ...string) {
|
|||
log.Println("[extension arg = C_CRYPTMT1]")
|
||||
hc.cipheropts &= (0xFFFFFF00)
|
||||
hc.cipheropts |= CAlgCryptMT1
|
||||
case "C_HOPSCOTCH":
|
||||
log.Println("[extension arg = C_HOPSCOTCH]")
|
||||
hc.cipheropts &= (0xFFFFFF00)
|
||||
hc.cipheropts |= CAlgHopscotch
|
||||
case "C_CHACHA20_12":
|
||||
log.Println("[extension arg = C_CHACHA20_12]")
|
||||
hc.cipheropts &= (0xFFFFFF00)
|
||||
|
|
@ -364,13 +355,6 @@ func (hc *Conn) applyConnExtensions(extensions ...string) {
|
|||
log.Println("[extension arg = H_SHA512]")
|
||||
hc.cipheropts &= (0xFFFF00FF)
|
||||
hc.cipheropts |= (HmacSHA512 << 8)
|
||||
case "H_WHIRLPOOL":
|
||||
log.Println("[extension arg = H_WHIRLPOOL]")
|
||||
hc.cipheropts &= (0xFFFF00FF)
|
||||
hc.cipheropts |= (HmacWHIRLPOOL << 8)
|
||||
case "OPT_REMOD":
|
||||
log.Println("[extension arg = OPT_REMOD]")
|
||||
hc.opts |= CORemodulateShields
|
||||
//default:
|
||||
// log.Printf("[Dial ext \"%s\" ignored]\n", s)
|
||||
}
|
||||
|
|
@ -490,11 +474,24 @@ func FrodoKEMDialSetup(c io.ReadWriter, hc *Conn) (err error) {
|
|||
return
|
||||
}
|
||||
|
||||
// randReader wraps rand.Read() in a struct that implements io.Reader
|
||||
// for use by the Kyber and NEWHOPE/NEWHOPE_SIMPLE KEM methods.
|
||||
type randReader struct {
|
||||
}
|
||||
|
||||
func (r randReader) Read(b []byte) (n int, e error) {
|
||||
n, e = rand.Read(b)
|
||||
return
|
||||
}
|
||||
|
||||
func NewHopeDialSetup(c io.ReadWriter, hc *Conn) (err error) {
|
||||
// Send xsnet.Conn parameters to remote side
|
||||
|
||||
// Alice, step 1: Generate a key pair.
|
||||
privKeyAlice, pubKeyAlice, err := newhope.GenerateKeyPairAlice(crand.Reader)
|
||||
r := new(randReader)
|
||||
rand.Seed(time.Now().UnixNano())
|
||||
|
||||
privKeyAlice, pubKeyAlice, err := newhope.GenerateKeyPairAlice(r)
|
||||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
|
@ -526,7 +523,7 @@ func NewHopeDialSetup(c io.ReadWriter, hc *Conn) (err error) {
|
|||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
||||
|
||||
hc.r, hc.rm, err = hc.getStream(aliceSharedSecret)
|
||||
hc.w, hc.wm, err = hc.getStream(aliceSharedSecret)
|
||||
return
|
||||
|
|
@ -536,7 +533,9 @@ func NewHopeSimpleDialSetup(c io.ReadWriter, hc *Conn) (err error) {
|
|||
// Send xsnet.Conn parameters to remote side
|
||||
|
||||
// Alice, step 1: Generate a key pair.
|
||||
privKeyAlice, pubKeyAlice, err := newhope.GenerateKeyPairSimpleAlice(crand.Reader)
|
||||
r := new(randReader)
|
||||
rand.Seed(time.Now().UnixNano())
|
||||
privKeyAlice, pubKeyAlice, err := newhope.GenerateKeyPairSimpleAlice(r)
|
||||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
|
@ -568,7 +567,7 @@ func NewHopeSimpleDialSetup(c io.ReadWriter, hc *Conn) (err error) {
|
|||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
||||
|
||||
hc.r, hc.rm, err = hc.getStream(aliceSharedSecret)
|
||||
hc.w, hc.wm, err = hc.getStream(aliceSharedSecret)
|
||||
return
|
||||
|
|
@ -578,17 +577,19 @@ func KyberDialSetup(c io.ReadWriter /*net.Conn*/, hc *Conn) (err error) {
|
|||
// Send xsnet.Conn parameters to remote side
|
||||
|
||||
// Alice, step 1: Generate a key pair.
|
||||
r := new(randReader)
|
||||
rand.Seed(time.Now().UnixNano())
|
||||
var alicePublicKey *kyber.PublicKey
|
||||
var alicePrivateKey *kyber.PrivateKey
|
||||
switch hc.kex {
|
||||
case KEX_KYBER512:
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber512.GenerateKeyPair(crand.Reader)
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber512.GenerateKeyPair(r)
|
||||
case KEX_KYBER768:
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber768.GenerateKeyPair(crand.Reader)
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber768.GenerateKeyPair(r)
|
||||
case KEX_KYBER1024:
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber1024.GenerateKeyPair(crand.Reader)
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber1024.GenerateKeyPair(r)
|
||||
default:
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber768.GenerateKeyPair(crand.Reader)
|
||||
alicePublicKey, alicePrivateKey, err = kyber.Kyber768.GenerateKeyPair(r)
|
||||
}
|
||||
|
||||
if err != nil {
|
||||
|
|
@ -681,6 +682,7 @@ func FrodoKEMAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
}
|
||||
pubB, secB := kem.Keygen()
|
||||
|
||||
|
||||
// [Alice sends use a public key (na, ea)
|
||||
pubA_bigint := big.NewInt(0)
|
||||
_, err = fmt.Fscanf(*c, "0x%x\n", pubA_bigint)
|
||||
|
|
@ -704,7 +706,7 @@ func FrodoKEMAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
|
||||
// (... and send cipher, connection opts)
|
||||
fmt.Fprintf(*c, "0x%x:0x%x\n", hc.cipheropts, hc.opts)
|
||||
|
||||
|
||||
// Bob, step 3: Create ctBtoA, shareB
|
||||
ctBtoA, shareB, err := kem.Encapsulate(pubA)
|
||||
if err != nil {
|
||||
|
|
@ -729,6 +731,8 @@ func FrodoKEMAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
}
|
||||
|
||||
func NewHopeAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
||||
r := new(randReader)
|
||||
rand.Seed(time.Now().UnixNano())
|
||||
// Bob, step 1: Deserialize Alice's public key from the binary encoding.
|
||||
alicePublicKey := big.NewInt(0)
|
||||
_, err = fmt.Fscanln(*c, alicePublicKey)
|
||||
|
|
@ -750,7 +754,7 @@ func NewHopeAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
}
|
||||
|
||||
// Bob, step 2: Generate the KEM cipher text and shared secret.
|
||||
pubKeyBob, bobSharedSecret, err := newhope.KeyExchangeBob(crand.Reader, &pubKeyAlice)
|
||||
pubKeyBob, bobSharedSecret, err := newhope.KeyExchangeBob(r, &pubKeyAlice)
|
||||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
|
@ -765,6 +769,8 @@ func NewHopeAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
}
|
||||
|
||||
func NewHopeSimpleAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
||||
r := new(randReader)
|
||||
rand.Seed(time.Now().UnixNano())
|
||||
// Bob, step 1: Deserialize Alice's public key from the binary encoding.
|
||||
alicePublicKey := big.NewInt(0)
|
||||
_, err = fmt.Fscanln(*c, alicePublicKey)
|
||||
|
|
@ -786,7 +792,7 @@ func NewHopeSimpleAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
}
|
||||
|
||||
// Bob, step 2: Generate the KEM cipher text and shared secret.
|
||||
pubKeyBob, bobSharedSecret, err := newhope.KeyExchangeSimpleBob(crand.Reader, &pubKeyAlice)
|
||||
pubKeyBob, bobSharedSecret, err := newhope.KeyExchangeSimpleBob(r, &pubKeyAlice)
|
||||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
|
@ -832,7 +838,9 @@ func KyberAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
}
|
||||
|
||||
// Bob, step 2: Generate the KEM cipher text and shared secret.
|
||||
cipherText, bobSharedSecret, err := peerPublicKey.KEMEncrypt(crand.Reader)
|
||||
r := new(randReader)
|
||||
rand.Seed(time.Now().UnixNano())
|
||||
cipherText, bobSharedSecret, err := peerPublicKey.KEMEncrypt(r)
|
||||
if err != nil {
|
||||
panic(err)
|
||||
}
|
||||
|
|
@ -893,12 +901,12 @@ func HKExAcceptSetup(c *net.Conn, hc *Conn) (err error) {
|
|||
// Dial as net.Dial(), but with implicit key exchange to set up secure
|
||||
// channel on connect
|
||||
//
|
||||
// Can be called like net.Dial(), defaulting to C_AES_256/H_SHA256,
|
||||
// or additional extensions can be passed amongst the following:
|
||||
// Can be called like net.Dial(), defaulting to C_AES_256/H_SHA256,
|
||||
// or additional extensions can be passed amongst the following:
|
||||
//
|
||||
// "C_AES_256" | "C_TWOFISH_128" | ...
|
||||
// "C_AES_256" | "C_TWOFISH_128" | ...
|
||||
//
|
||||
// "H_SHA256" | "H_SHA512" | ...
|
||||
// "H_SHA256" | "H_SHA512" | ...
|
||||
//
|
||||
// See go doc -u xsnet.applyConnExtensions
|
||||
func Dial(protocol string, ipport string, extensions ...string) (hc Conn, err error) {
|
||||
|
|
@ -982,25 +990,12 @@ func Dial(protocol string, ipport string, extensions ...string) (hc Conn, err er
|
|||
|
||||
// Close a hkex.Conn
|
||||
func (hc *Conn) Close() (err error) {
|
||||
hc.ShutdownChaff()
|
||||
hc.DisableChaff()
|
||||
s := make([]byte, 4)
|
||||
binary.BigEndian.PutUint32(s, uint32(*hc.closeStat))
|
||||
log.Printf("** Writing closeStat %d at Close()\n", *hc.closeStat)
|
||||
//(*hc.c).SetWriteDeadline(time.Now().Add(500 * time.Millisecond))
|
||||
hc.WritePacket(s, CSOExitStatus)
|
||||
|
||||
// HACK: Bug #22,#33: Need to wait for rcvr to get final data
|
||||
// TODO: Find a way to explicitly check if any outgoing data is pending
|
||||
|
||||
//Ensure socket has sent all data to client prior to closing
|
||||
//NOTE: This is not ideal, as it would be better to somehow
|
||||
//determine if there is any pending outgoing (write) data to the
|
||||
//underlying socket (TCP/KCP) prior to closing; however Go's net pkg
|
||||
//completely hides lower-level stuff. net.Conn.Close() according to
|
||||
//docs sends written data in the background, so how best to determine
|
||||
//all data has been sent? -rlm 2022-10-04
|
||||
time.Sleep(10 * time.Millisecond) //nolint:gomnd
|
||||
|
||||
err = (*hc.c).Close()
|
||||
logger.LogDebug(fmt.Sprintln("[Conn Closing]"))
|
||||
return
|
||||
|
|
@ -1095,7 +1090,7 @@ func (hl HKExListener) Close() error {
|
|||
return hl.l.Close()
|
||||
}
|
||||
|
||||
// Addr returns the listener's network address.
|
||||
// Addr returns a the listener's network address.
|
||||
//
|
||||
// See go doc net.Listener.Addr
|
||||
func (hl HKExListener) Addr() net.Addr {
|
||||
|
|
@ -1120,7 +1115,7 @@ func (hl *HKExListener) Accept() (hc Conn, err error) {
|
|||
return Conn{}, err
|
||||
}
|
||||
|
||||
logger.LogDebug(fmt.Sprintf("[net.Listener Accepted %v]\n", c.RemoteAddr()))
|
||||
logger.LogDebug(fmt.Sprintln("[net.Listener Accepted]"))
|
||||
}
|
||||
// Read KEx alg proposed by client
|
||||
var kexAlg KEXAlg
|
||||
|
|
@ -1194,8 +1189,10 @@ func (hl *HKExListener) Accept() (hc Conn, err error) {
|
|||
return Conn{}, err
|
||||
}
|
||||
|
||||
// Finally, ensure alg proposed by client is allowed by server config
|
||||
//if hc.kex.String() {
|
||||
log.Println("[hc.Accept successful]")
|
||||
return hc, err
|
||||
return
|
||||
}
|
||||
|
||||
/*---------------------------------------------------------------------*/
|
||||
|
|
@ -1207,7 +1204,7 @@ func (hl *HKExListener) Accept() (hc Conn, err error) {
|
|||
// packet processing.
|
||||
//
|
||||
// See go doc io.Reader
|
||||
func (hc *Conn) Read(b []byte) (n int, err error) {
|
||||
func (hc Conn) Read(b []byte) (n int, err error) {
|
||||
for {
|
||||
if hc.dBuf.Len() > 0 {
|
||||
break
|
||||
|
|
@ -1217,7 +1214,6 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
var hmacIn [HMAC_CHK_SZ]uint8
|
||||
var payloadLen uint32
|
||||
|
||||
//------------- Read ctrl/status opcode --------------------
|
||||
// Read ctrl/status opcode (CSOHmacInvalid on hmac mismatch)
|
||||
err = binary.Read(*hc.c, binary.BigEndian, &ctrlStatOp)
|
||||
if err != nil {
|
||||
|
|
@ -1225,8 +1221,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
return 0, io.EOF
|
||||
}
|
||||
if strings.HasSuffix(err.Error(), "use of closed network connection") {
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up(1)]"))
|
||||
//!rlm hc.SetStatus(CSENone) //FIXME: re-examine this (exit 9 w/o it - 2023-11-05)
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up]"))
|
||||
return 0, io.EOF
|
||||
}
|
||||
etxt := fmt.Sprintf("** Failed read:%s (%s) **", "ctrlStatOp", err)
|
||||
|
|
@ -1239,9 +1234,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
hc.Close()
|
||||
return 0, errors.New("** ALERT - remote end detected HMAC mismatch - possible channel tampering **")
|
||||
}
|
||||
//----------------------------------------------------------
|
||||
|
||||
//------------------ Read HMAC len ------------------------
|
||||
// Read the hmac and payload len first
|
||||
err = binary.Read(*hc.c, binary.BigEndian, &hmacIn)
|
||||
if err != nil {
|
||||
|
|
@ -1249,30 +1242,27 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
return 0, io.EOF
|
||||
}
|
||||
if strings.HasSuffix(err.Error(), "use of closed network connection") {
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up(2)]"))
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up]"))
|
||||
return 0, io.EOF
|
||||
}
|
||||
etxt := fmt.Sprintf("** Failed read:%s (%s) **", "HMAC", err)
|
||||
logger.LogDebug(etxt)
|
||||
return 0, errors.New(etxt)
|
||||
}
|
||||
//----------------------------------------------------------
|
||||
|
||||
//------------------ Read Payload len ---------------------
|
||||
err = binary.Read(*hc.c, binary.BigEndian, &payloadLen)
|
||||
if err != nil {
|
||||
if err.Error() == "EOF" {
|
||||
return 0, io.EOF
|
||||
}
|
||||
if strings.HasSuffix(err.Error(), "use of closed network connection") {
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up(3)]"))
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up]"))
|
||||
return 0, io.EOF
|
||||
}
|
||||
etxt := fmt.Sprintf("** Failed read:%s (%s) **", "payloadLen", err)
|
||||
logger.LogDebug(etxt)
|
||||
return 0, errors.New(etxt)
|
||||
}
|
||||
//----------------------------------------------------------
|
||||
|
||||
if payloadLen > MAX_PAYLOAD_LEN {
|
||||
logger.LogDebug(fmt.Sprintf("[Insane payloadLen:%v]\n", payloadLen))
|
||||
|
|
@ -1280,7 +1270,6 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
return 1, errors.New("Insane payloadLen")
|
||||
}
|
||||
|
||||
//-------------------- Read Payload ------------------------
|
||||
var payloadBytes = make([]byte, payloadLen)
|
||||
n, err = io.ReadFull(*hc.c, payloadBytes)
|
||||
if err != nil {
|
||||
|
|
@ -1288,21 +1277,19 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
return 0, io.EOF
|
||||
}
|
||||
if strings.HasSuffix(err.Error(), "use of closed network connection") {
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up(4)]"))
|
||||
logger.LogDebug(fmt.Sprintln("[Client hung up]"))
|
||||
return 0, io.EOF
|
||||
}
|
||||
etxt := fmt.Sprintf("** Failed read:%s (%s) **", "payloadBytes", err)
|
||||
logger.LogDebug(etxt)
|
||||
return 0, errors.New(etxt)
|
||||
}
|
||||
//----------------------------------------------------------
|
||||
|
||||
if hc.logCipherText {
|
||||
log.Printf(" <:ctext:\r\n%s\r\n", hex.Dump(payloadBytes[:n]))
|
||||
}
|
||||
//fmt.Printf(" <:ctext:\r\n%s\r\n", hex.Dump(payloadBytes[:n]))
|
||||
|
||||
//---------------- Verify Payload via HMAC -----------------
|
||||
hc.rm.Write(payloadBytes) // Calc hmac on received data
|
||||
hTmp := hc.rm.Sum(nil)[0:HMAC_CHK_SZ]
|
||||
//log.Printf("<%04x) HMAC:(i)%s (c)%02x\r\n", decryptN, hex.EncodeToString([]byte(hmacIn[0:])), hTmp)
|
||||
|
|
@ -1312,9 +1299,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
logger.LogDebug(fmt.Sprintln("** ALERT - detected HMAC mismatch, possible channel tampering **"))
|
||||
_, _ = (*hc.c).Write([]byte{CSOHmacInvalid})
|
||||
}
|
||||
//----------------------------------------------------------
|
||||
|
||||
//------------------- Decrypt Payload ----------------------
|
||||
db := bytes.NewBuffer(payloadBytes[:n]) //copying payloadBytes to db
|
||||
// The StreamReader acts like a pipe, decrypting
|
||||
// whatever is available and forwarding the result
|
||||
|
|
@ -1323,7 +1308,6 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
// The caller isn't necessarily reading the full payload so we need
|
||||
// to decrypt to an intermediate buffer, draining it on demand of caller
|
||||
decryptN, err := rs.Read(payloadBytes)
|
||||
//----------------------------------------------------------
|
||||
|
||||
if hc.logPlainText {
|
||||
log.Printf(" <:ptext:\r\n%s\r\n", hex.Dump(payloadBytes[:n]))
|
||||
|
|
@ -1332,7 +1316,6 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
log.Println("xsnet.Read():", err)
|
||||
//panic(err)
|
||||
} else {
|
||||
//------------ Discard Padding ---------------------
|
||||
// Padding: Read padSide, padLen, (padding | d) or (d | padding)
|
||||
padSide := payloadBytes[0]
|
||||
padLen := payloadBytes[1]
|
||||
|
|
@ -1343,33 +1326,15 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
} else {
|
||||
payloadBytes = payloadBytes[0 : len(payloadBytes)-int(padLen)]
|
||||
}
|
||||
//--------------------------------------------------
|
||||
|
||||
switch ctrlStatOp {
|
||||
case CSOChaff:
|
||||
// Throw away pkt if it's chaff (ie., caller to Read() won't see this data)
|
||||
// Throw away pkt if it's chaff (ie., caller to Read() won't see this data)
|
||||
if ctrlStatOp == CSOChaff {
|
||||
log.Printf("[Chaff pkt, discarded (len %d)]\n", decryptN)
|
||||
case CSOKeepAlive:
|
||||
//logger.LogDebug(fmt.Sprintf("[got keepAlive pkt, discarded (len %d)]\n", decryptN))
|
||||
// payload of keepalive (2 bytes) is not currently used (0x55aa fixed)
|
||||
_ = binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
hc.ResetKeepAlive()
|
||||
case CSORekey:
|
||||
// rekey
|
||||
//logger.LogDebug(fmt.Sprintf("[Got rekey [%02x %02x %02x ...]\n",
|
||||
// payloadBytes[0], payloadBytes[1], payloadBytes[2]))
|
||||
rekeyData := payloadBytes
|
||||
if (hc.opts & CORemodulateShields) != 0 {
|
||||
hc.Lock()
|
||||
hc.cipheropts = getNewStreamAlgs(rekeyData[0], rekeyData[1])
|
||||
hc.Unlock()
|
||||
}
|
||||
hc.r, hc.rm, err = hc.getStream(rekeyData)
|
||||
case CSOTermSize:
|
||||
} else if ctrlStatOp == CSOTermSize {
|
||||
fmt.Sscanf(string(payloadBytes), "%d %d", &hc.Rows, &hc.Cols)
|
||||
log.Printf("[TermSize pkt: rows %v cols %v]\n", hc.Rows, hc.Cols)
|
||||
hc.WinCh <- WinSize{hc.Rows, hc.Cols}
|
||||
case CSOExitStatus:
|
||||
} else if ctrlStatOp == CSOExitStatus {
|
||||
if len(payloadBytes) > 0 {
|
||||
hc.SetStatus(CSOType(binary.BigEndian.Uint32(payloadBytes)))
|
||||
} else {
|
||||
|
|
@ -1377,7 +1342,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
hc.SetStatus(CSETruncCSO)
|
||||
}
|
||||
hc.Close()
|
||||
case CSOTunSetup:
|
||||
} else if ctrlStatOp == CSOTunSetup {
|
||||
// server side tunnel setup in response to client
|
||||
lport := binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
rport := binary.BigEndian.Uint16(payloadBytes[2:4])
|
||||
|
|
@ -1389,7 +1354,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
logger.LogDebug(fmt.Sprintf("[Server] Got CSOTunSetup [%d:%d]", lport, rport))
|
||||
}
|
||||
(*hc.tuns)[rport].Ctl <- 'd' // Dial() rport
|
||||
case CSOTunSetupAck:
|
||||
} else if ctrlStatOp == CSOTunSetupAck {
|
||||
lport := binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
rport := binary.BigEndian.Uint16(payloadBytes[2:4])
|
||||
if _, ok := (*hc.tuns)[rport]; !ok {
|
||||
|
|
@ -1400,7 +1365,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
logger.LogDebug(fmt.Sprintf("[Client] Got CSOTunSetupAck [%d:%d]", lport, rport))
|
||||
}
|
||||
(*hc.tuns)[rport].Ctl <- 'a' // Listen() for lport connection
|
||||
case CSOTunRefused:
|
||||
} else if ctrlStatOp == CSOTunRefused {
|
||||
// client side receiving CSOTunRefused means the remote side
|
||||
// could not dial() rport. So we cannot yet listen()
|
||||
// for client-side on lport.
|
||||
|
|
@ -1412,7 +1377,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
} else {
|
||||
logger.LogDebug(fmt.Sprintf("[Client] CSOTunRefused on already-closed tun [%d:%d]", lport, rport))
|
||||
}
|
||||
case CSOTunDisconn:
|
||||
} else if ctrlStatOp == CSOTunDisconn {
|
||||
// server side's rport has disconnected (server lost)
|
||||
lport := binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
rport := binary.BigEndian.Uint16(payloadBytes[2:4])
|
||||
|
|
@ -1422,7 +1387,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
} else {
|
||||
logger.LogDebug(fmt.Sprintf("[Client] CSOTunDisconn on already-closed tun [%d:%d]", lport, rport))
|
||||
}
|
||||
case CSOTunHangup:
|
||||
} else if ctrlStatOp == CSOTunHangup {
|
||||
// client side's lport has hung up
|
||||
lport := binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
rport := binary.BigEndian.Uint16(payloadBytes[2:4])
|
||||
|
|
@ -1432,7 +1397,7 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
} else {
|
||||
logger.LogDebug(fmt.Sprintf("[Server] CSOTunHangup to already-closed tun [%d:%d]", lport, rport))
|
||||
}
|
||||
case CSOTunData:
|
||||
} else if ctrlStatOp == CSOTunData {
|
||||
lport := binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
rport := binary.BigEndian.Uint16(payloadBytes[2:4])
|
||||
//fmt.Printf("[Got CSOTunData: [lport %d:rport %d] data:%v\n", lport, rport, payloadBytes[4:])
|
||||
|
|
@ -1445,23 +1410,20 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
} else {
|
||||
logger.LogDebug(fmt.Sprintf("[Attempt to write data to closed tun [%d:%d]", lport, rport))
|
||||
}
|
||||
case CSOTunKeepAlive:
|
||||
} else if ctrlStatOp == CSOTunKeepAlive {
|
||||
// client side has sent keepalive for tunnels -- if client
|
||||
// dies or exits unexpectedly the absence of this will
|
||||
// let the server know to hang up on Dial()ed server rports.
|
||||
_ = binary.BigEndian.Uint16(payloadBytes[0:2])
|
||||
//logger.LogDebug(fmt.Sprintf("[Server] Got CSOTunKeepAlive"))
|
||||
// though CSOTunKeepAlive sends an endp (uint16), we don't use it,
|
||||
// preferring to refresh *all* tunnels on the message.
|
||||
// (?rlm 2023-11-04 -- TODO: verify this, it's been a while.)
|
||||
for _, t := range *hc.tuns {
|
||||
hc.Lock()
|
||||
t.KeepAlive = 0
|
||||
hc.Unlock()
|
||||
}
|
||||
case CSONone:
|
||||
} else if ctrlStatOp == CSONone {
|
||||
hc.dBuf.Write(payloadBytes)
|
||||
default:
|
||||
} else {
|
||||
logger.LogDebug(fmt.Sprintf("[Unknown CSOType:%d]", ctrlStatOp))
|
||||
}
|
||||
}
|
||||
|
|
@ -1481,18 +1443,13 @@ func (hc *Conn) Read(b []byte) (n int, err error) {
|
|||
// Write a byte slice
|
||||
//
|
||||
// See go doc io.Writer
|
||||
func (hc *Conn) Write(b []byte) (n int, err error) {
|
||||
//logger.LogDebug("[+Write]")
|
||||
func (hc Conn) Write(b []byte) (n int, err error) {
|
||||
n, err = hc.WritePacket(b, CSONone)
|
||||
//logger.LogDebug("[-Write]")
|
||||
return n, err
|
||||
}
|
||||
|
||||
// Write a byte slice with specified ctrlStatOp byte
|
||||
func (hc *Conn) WritePacket(b []byte, ctrlStatOp byte) (n int, err error) {
|
||||
hc.Lock()
|
||||
defer hc.Unlock()
|
||||
|
||||
//log.Printf("[Encrypting...]\r\n")
|
||||
var hmacOut []uint8
|
||||
var payloadLen uint32
|
||||
|
|
@ -1520,6 +1477,15 @@ func (hc *Conn) WritePacket(b []byte, ctrlStatOp byte) (n int, err error) {
|
|||
b = append([]byte{byte(padSide)}, append([]byte{byte(padLen)}, append(b, padBytes...)...)...)
|
||||
}
|
||||
|
||||
// N.B. Originally this Lock() surrounded only the
|
||||
// calls to binary.Write(hc.c ..) however there appears
|
||||
// to be some other unshareable state in the Conn
|
||||
// struct that must be protected to serialize main and
|
||||
// chaff data written to it.
|
||||
//
|
||||
// Would be nice to determine if the mutex scope
|
||||
// could be tightened.
|
||||
hc.Lock()
|
||||
payloadLen = uint32(len(b))
|
||||
if hc.logPlainText {
|
||||
log.Printf(" >:ptext:\r\n%s\r\n", hex.Dump(b[0:payloadLen]))
|
||||
|
|
@ -1577,6 +1543,7 @@ func (hc *Conn) WritePacket(b []byte, ctrlStatOp byte) (n int, err error) {
|
|||
} else {
|
||||
//fmt.Println("[a]WriteError!")
|
||||
}
|
||||
hc.Unlock()
|
||||
|
||||
if err != nil {
|
||||
log.Println(err)
|
||||
|
|
@ -1591,182 +1558,53 @@ func (hc *Conn) WritePacket(b []byte, ctrlStatOp byte) (n int, err error) {
|
|||
return retN, err
|
||||
}
|
||||
|
||||
func (hc *Conn) StartupChaff() {
|
||||
func (hc *Conn) EnableChaff() {
|
||||
hc.chaff.shutdown = false
|
||||
hc.chaff.enabled = true
|
||||
log.Println("Chaffing ENABLED")
|
||||
hc.chaffHelper()
|
||||
}
|
||||
|
||||
func (hc *Conn) DisableChaff() {
|
||||
hc.chaff.enabled = false
|
||||
log.Println("Chaffing DISABLED")
|
||||
}
|
||||
|
||||
func (hc *Conn) ShutdownChaff() {
|
||||
hc.Lock()
|
||||
hc.chaff.shutdown = true
|
||||
hc.Unlock()
|
||||
log.Println("Chaffing SHUTDOWN")
|
||||
}
|
||||
|
||||
func (hc *Conn) SetupChaff(msecsMin uint, msecsMax uint, szMax uint) {
|
||||
// Enforce bounds on chaff frequency and pkt size
|
||||
hc.Lock()
|
||||
if hc.chaff.msecsMin < CHAFF_FREQ_MSECS_MIN {
|
||||
hc.chaff.msecsMin = CHAFF_FREQ_MSECS_MIN
|
||||
}
|
||||
if hc.chaff.msecsMax > CHAFF_FREQ_MSECS_MAX {
|
||||
hc.chaff.msecsMax = CHAFF_FREQ_MSECS_MAX
|
||||
}
|
||||
hc.Unlock()
|
||||
|
||||
hc.chaff.msecsMin = msecsMin //move these to params of chaffHelper() ?
|
||||
hc.chaff.msecsMax = msecsMax
|
||||
hc.chaff.szMax = szMax
|
||||
}
|
||||
|
||||
func (hc *Conn) ShutdownRekey() {
|
||||
hc.Lock()
|
||||
hc.rekey = 0
|
||||
hc.Unlock()
|
||||
}
|
||||
|
||||
func (hc *Conn) RekeyHelper(intervalSecs uint) {
|
||||
if intervalSecs < REKEY_SECS_MIN {
|
||||
intervalSecs = REKEY_SECS_MIN
|
||||
}
|
||||
if intervalSecs > REKEY_SECS_MAX {
|
||||
intervalSecs = REKEY_SECS_MAX
|
||||
}
|
||||
|
||||
go func() {
|
||||
hc.Lock()
|
||||
hc.rekey = intervalSecs
|
||||
hc.Unlock()
|
||||
|
||||
for {
|
||||
hc.Lock()
|
||||
rekey := hc.rekey
|
||||
hc.Unlock()
|
||||
|
||||
if rekey != 0 {
|
||||
jitter := rand.Intn(int(rekey)) / 4
|
||||
rekey = rekey - uint(jitter)
|
||||
if rekey < 1 {
|
||||
rekey = 1
|
||||
}
|
||||
|
||||
//logger.LogDebug(fmt.Sprintf("[rekeyHelper Loop]\n"))
|
||||
time.Sleep(time.Duration(rekey) * time.Second)
|
||||
|
||||
// Send rekey to other end
|
||||
rekeyData := make([]byte, 64)
|
||||
_, err := crand.Read(rekeyData)
|
||||
//logger.LogDebug(fmt.Sprintf("[rekey [%02x %02x %02x ...]\n",
|
||||
// rekeyData[0], rekeyData[1], rekeyData[2]))
|
||||
//logger.LogDebug("[+rekeyHelper]")
|
||||
_, err = hc.WritePacket(rekeyData, CSORekey)
|
||||
hc.Lock()
|
||||
if (hc.opts & CORemodulateShields) != 0 {
|
||||
hc.cipheropts = getNewStreamAlgs(rekeyData[0], rekeyData[1])
|
||||
}
|
||||
hc.w, hc.wm, err = hc.getStream(rekeyData)
|
||||
//logger.LogDebug("[-rekeyHelper]")
|
||||
hc.Unlock()
|
||||
if err != nil {
|
||||
log.Printf("[rekey WritePacket err! (%v) rekey dying ...]\n", err)
|
||||
return
|
||||
}
|
||||
} else {
|
||||
return
|
||||
}
|
||||
}
|
||||
}()
|
||||
}
|
||||
|
||||
// Helper routine to spawn a chaffing goroutine for each Conn
|
||||
func (hc *Conn) chaffHelper() {
|
||||
go func() {
|
||||
var nextDuration int
|
||||
for {
|
||||
//logger.LogDebug(fmt.Sprintf("[chaffHelper Loop]\n"))
|
||||
hc.Lock()
|
||||
shutdown := hc.chaff.shutdown
|
||||
hc.Unlock()
|
||||
if !shutdown {
|
||||
var nextDuration int
|
||||
if hc.chaff.enabled {
|
||||
var bufTmp []byte
|
||||
bufTmp = make([]byte, rand.Intn(int(hc.chaff.szMax)))
|
||||
min := int(hc.chaff.msecsMin)
|
||||
nextDuration = rand.Intn(int(hc.chaff.msecsMax)-min) + min
|
||||
_, _ = rand.Read(bufTmp)
|
||||
//logger.LogDebug("[+chaffHelper]")
|
||||
_, err := hc.WritePacket(bufTmp, CSOChaff)
|
||||
//logger.LogDebug("[-chaffHelper]")
|
||||
if err != nil {
|
||||
log.Println("[ *** error - chaffHelper shutting down *** ]")
|
||||
hc.Lock()
|
||||
hc.chaff.shutdown = true
|
||||
hc.Unlock()
|
||||
log.Println("[ *** error - chaffHelper quitting *** ]")
|
||||
hc.chaff.enabled = false
|
||||
break
|
||||
}
|
||||
} else {
|
||||
log.Println("[ *** chaffHelper shutting down *** ]")
|
||||
break
|
||||
}
|
||||
time.Sleep(time.Duration(nextDuration) * time.Millisecond)
|
||||
}
|
||||
}()
|
||||
}
|
||||
|
||||
func (hc *Conn) StartupKeepAlive() {
|
||||
hc.ResetKeepAlive()
|
||||
log.Println("KeepAlive ENABLED")
|
||||
hc.keepaliveHelper()
|
||||
}
|
||||
|
||||
func (hc *Conn) ShutdownKeepAlive() {
|
||||
log.Println("Conn SHUTDOWN")
|
||||
hc.Close()
|
||||
}
|
||||
|
||||
func (hc *Conn) ResetKeepAlive() {
|
||||
hc.Lock()
|
||||
hc.keepalive = 3
|
||||
hc.Unlock()
|
||||
log.Println("KeepAlive RESET")
|
||||
}
|
||||
|
||||
// Helper routine to spawn a keepalive goroutine for each Conn
|
||||
func (hc *Conn) keepaliveHelper() {
|
||||
go func() {
|
||||
for {
|
||||
nextDuration := 10000
|
||||
bufTmp := []byte{0x55, 0xaa}
|
||||
//logger.LogDebug("[+keepaliveHelper]")
|
||||
_, err := hc.WritePacket(bufTmp, CSOKeepAlive)
|
||||
//logger.LogDebug("[-keepaliveHelper]")
|
||||
//logger.LogDebug(fmt.Sprintf("[keepalive]\n"))
|
||||
if err != nil {
|
||||
logger.LogDebug(fmt.Sprintf("[ *** error - keepaliveHelper quitting *** ]\n"))
|
||||
break
|
||||
}
|
||||
time.Sleep(time.Duration(nextDuration) * time.Millisecond)
|
||||
hc.Lock()
|
||||
hc.keepalive -= 1
|
||||
hc.Unlock()
|
||||
//logger.LogDebug(fmt.Sprintf("[keepAlive is now %d]\n", hc.keepalive))
|
||||
|
||||
//if rand.Intn(8) == 0 {
|
||||
// hc.keepalive = 0
|
||||
//}
|
||||
|
||||
if hc.keepalive == 0 {
|
||||
logger.LogDebug(fmt.Sprintf("*** keepaliveHelper shutting down\n"))
|
||||
hc.SetStatus(CSEConnDead)
|
||||
hc.ShutdownKeepAlive()
|
||||
if hc.Pproc != 0 {
|
||||
//fmt.Printf("[pid %d needs to be killed]\n", hc.Pproc)
|
||||
//syscall.Kill(hc.Pproc, syscall.SIGABRT) //nolint:errcheck
|
||||
//exec.Command("taskkill", "/f", "/pid", strconv.Itoa(hc.Pproc)).Run()
|
||||
hc.kill()
|
||||
}
|
||||
break
|
||||
}
|
||||
if hc.chaff.shutdown {
|
||||
log.Println("*** chaffHelper shutting down")
|
||||
break
|
||||
}
|
||||
|
||||
}
|
||||
}()
|
||||
}
|
||||
|
|
|
|||
|
|
@ -1,13 +0,0 @@
|
|||
//go:build linux
|
||||
// +build linux
|
||||
|
||||
package xsnet
|
||||
|
||||
import (
|
||||
"syscall"
|
||||
)
|
||||
|
||||
func (hc *Conn) kill() {
|
||||
syscall.Kill(hc.Pproc, syscall.SIGABRT) //nolint:errcheck
|
||||
}
|
||||
|
||||
|
|
@ -1,13 +0,0 @@
|
|||
//go:build windows
|
||||
// +build windows
|
||||
|
||||
package xsnet
|
||||
|
||||
import (
|
||||
"os/exec"
|
||||
"strconv"
|
||||
)
|
||||
|
||||
func (hc *Conn) kill() {
|
||||
exec.Command("taskkill", "/f", "/pid", strconv.Itoa(hc.Pproc)).Run()
|
||||
}
|
||||
|
|
@ -37,8 +37,6 @@ type (
|
|||
// client starts worker to receive/send data using lport
|
||||
// ... client disconnects: sends remhost [CSOTunClose:rport]
|
||||
// ... or server disconnects: sends client [CSOTunClose:lport]
|
||||
// ... or server disconnects: due to client failing to send TunKeepAlive
|
||||
// events for too long
|
||||
// server at any time sends [CSOTunRefused:rport] if daemon died
|
||||
// --
|
||||
|
||||
|
|
|
|||
|
|
@ -1,16 +1,10 @@
|
|||
.PHONY: clean all vis lint
|
||||
|
||||
ifeq ($(GARBLE),y)
|
||||
GO = garble -tiny -literals -debugdir=garbled
|
||||
else
|
||||
GO = go
|
||||
endif
|
||||
|
||||
EXTPKGS = bytes,errors,flag,fmt,internal,io,log,net,os,path,runtime,time,strings,sync,syscall,binary,encoding
|
||||
EXE = $(notdir $(shell pwd))
|
||||
|
||||
all:
|
||||
$(GO) build $(BUILDOPTS) .
|
||||
go build $(BUILDOPTS) .
|
||||
|
||||
clean:
|
||||
$(RM) $(EXE) $(EXE).exe
|
||||
|
|
|
|||
|
|
@ -1,7 +1,7 @@
|
|||
// Util to generate/store passwords for users in a file akin to /etc/passwd
|
||||
// suitable for the xs server, using bcrypt.
|
||||
// suitable for the demo hkexsh server, using bcrypt.
|
||||
//
|
||||
// Copyright (c) 2017-2025 Russell Magee
|
||||
// Copyright (c) 2017-2020 Russell Magee
|
||||
// Licensed under the terms of the MIT license (see LICENSE.mit in this
|
||||
// distribution)
|
||||
//
|
||||
|
|
|
|||
Loading…
Reference in New Issue